Ronin Bridge Hack Analysis
Ronin Bridge Hack Analysis
Overview:
On August 6th, 2024, the Ronin Network Bridge (@Ronin_Network), was exploited resulting in the loss of $12 Million (comprising $2 Million in USDC and 4K ETH) due to a vulnerability introduced during a recent contract upgrade, which was exploited by an MEV-bot.
Smart Contract Hack Overview:
- Frontrunning Attack Transaction: 0x26195
- Bridge Manager: 0xa7145
- Upgraded Implementation: 0xfc274
- MEV-Bot: 0xc6aec
Decoding the Smart Contract Vulnerability:
· The root cause is that the Ronin team had deployed a faulty upgrade with an uninitialized variable to their bridge manager, transitioning from version 2 to version 4.
· In the latest upgrade of the Ronin Bridge, the `totalWeight` value, previously fetched from the `MainchainBridgeManager` contract, was moved to be stored directly in the contract’s storage under the variable `_totalOperatorWeight`.
· During this process, they introduced a new implementation contract, MainchainGatewayV3. However, the team neglected to call the `initializeV3` function, which was critical for setting up the `_totalOperatorWeight` variable.
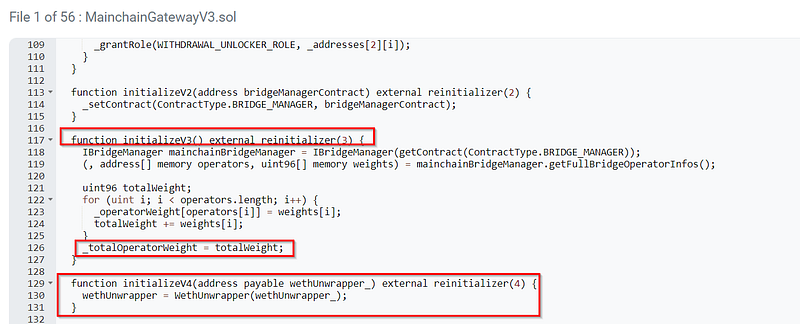
· The failure to call `initializeV3` left the `_totalOperatorWeight` variable uninitialized, defaulting to zero. This had the unintended consequence of disabling the `minimumVoteWeight` parameter, a key security check for cross-chain verification, effectively leaving the bridge vulnerable to unauthorized withdrawals.
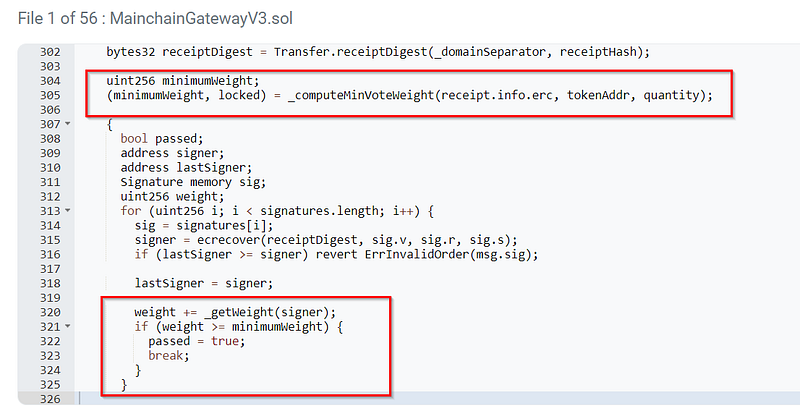
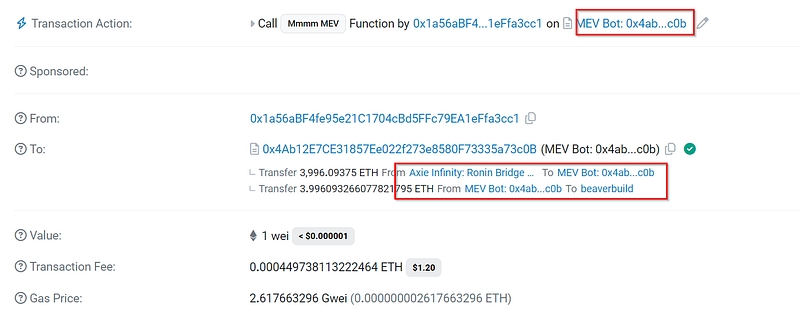
· The MEV bot detected the disabled `minimumVoteWeight` parameter and executed a withdrawal transaction, pulling 4,000 ETH and 2 million USDC from the bridge.
· The Ronin Bridge had a daily withdrawal limit of $12 Million, a critical safeguard that capped the maximum amount that could be withdrawn in a single transaction. This limit prevented the loss of an additional $72 million, which would have been at risk without this control.
· The Ronin team was alerted to the exploit and managed to pause the bridge contract approximately 38 minutes after the first unauthorized transaction.
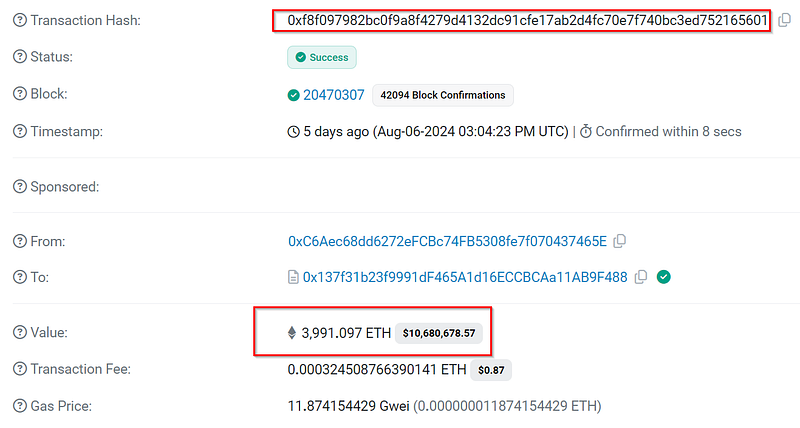
· The ETH, valued at approximately $10 million, has been returned and also, the USDC too.
Mitigation and Best Practices:
· Implement a thorough testing process for all contract upgrades, with a specific focus on ensuring that all critical variables, such as _totalOperatorWeight in this case, are properly initialized.
· Adopt an incremental deployment approach for significant contract upgrades, deploying them in stages and with built-in safeguards like lower withdrawal limits initially. This allows for the detection and correction of potential issues before the full upgrade is completed and larger funds are at risk.
· Always validate your code by writing comprehensive test cases that cover all the possible business logic.
· To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Our public audit reports can be found on https://github.com/Credshields/audit-reports. Schedule a call at https://credshields.com/
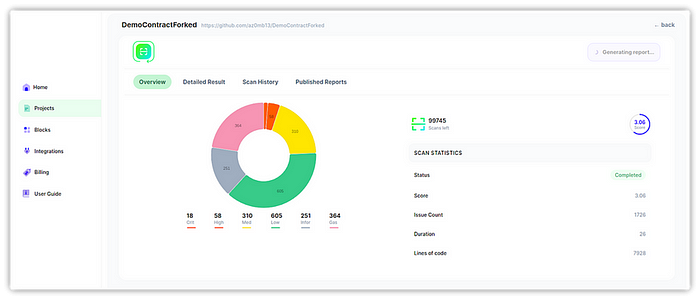
· Scan your Solidity contracts against the latest common security vulnerabilities with 225+ detections at SolidityScan.
Conclusion:
SolidityScan is an advanced smart contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
