AAVE Repay Adapter Hack Analysis
AAVE Repay Adapter Hack Analysis
Overview:
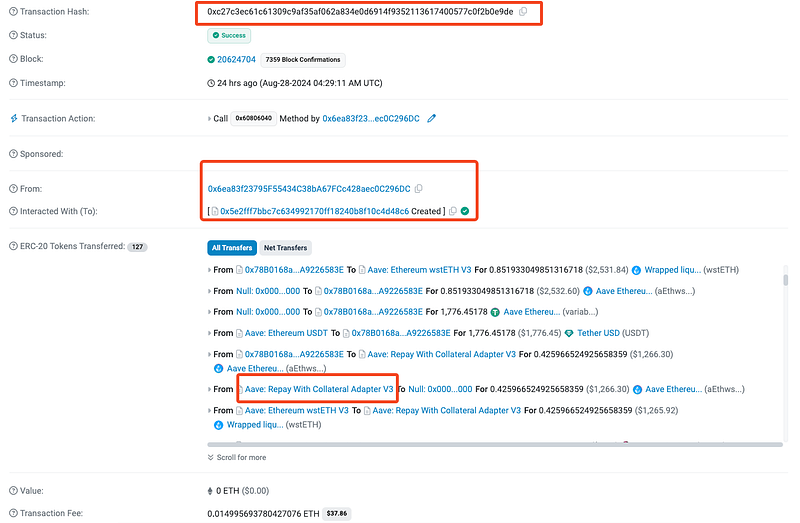
On August 28th, 2024, the periphery contract of one of the biggest lending protocols in DeFi- Aave (@aave), was exploited resulting in a loss of $56K USD (on different chains) due to a vulnerability in the Repay With Collateral Adapter V3 contract. The peripheral contract, used only on the app.aave.com user interface, was not part of Aave’s core smart contracts involving pool dynamics and has no relation to these theft transactions.
Smart Contract Hack Overview:
- Attack Transaction: 0xc27c3
- Attacker’s Address: 0x6ea83
- Aave Collateral Repay Adapter V3: 0x02e7b
- Paraswap Contract: 0xdef17
Decoding the Smart Contract Vulnerability:
- The root cause of the vulnerability in the `_buyOnParaSwap` function is that it leaves a high token allowance unadjusted if the swap fails, processes unvalidated/ unsanitized `paraswapData`, and lacks proper swap outcome verification, allowing attackers to exploit and withdraw unauthorized tokens.
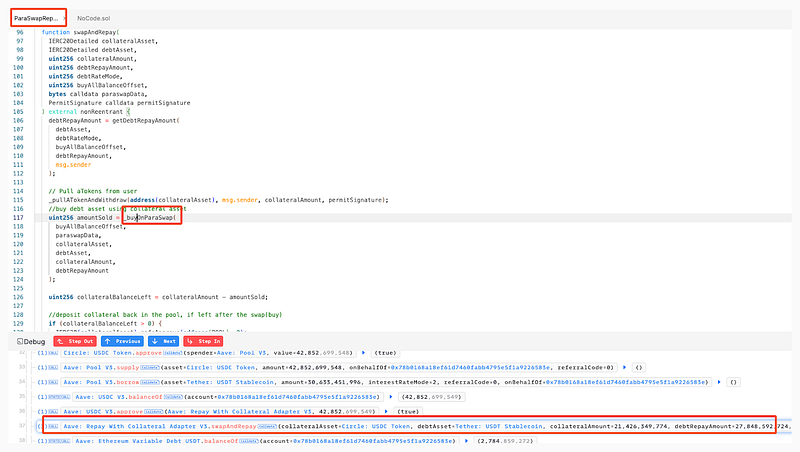
- Here, the function sets an allowance for `assetToSwapFrom` by calling `safeApprove` on `tokenTransferProxy` with `maxAmountToSwap`.
- However, it does not account for the scenario where the swap does not occur or only a partial swap happens. If the swap is not executed or if fewer tokens are swapped than allowed, the remaining allowance remains in place.
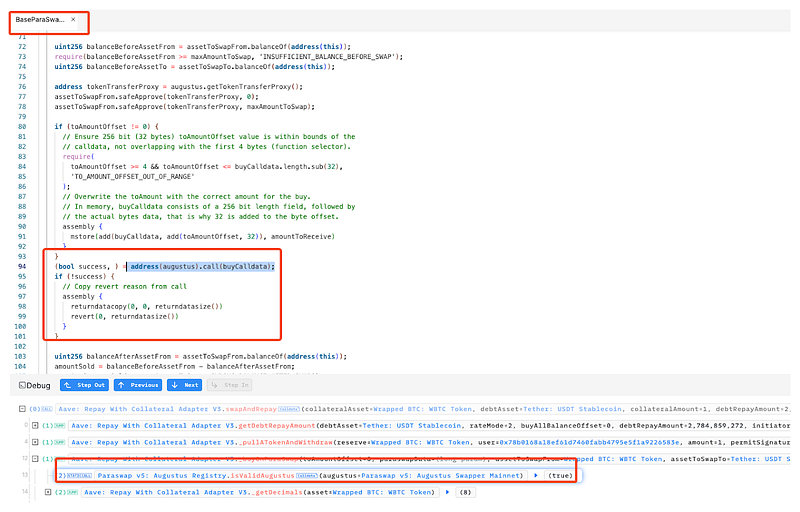
- This function relies on external contract interaction `(augustus.call(buyCalldata))` to perform the swap. If the `paraswapData` is maliciously crafted, it can manipulate the swap process or avoid the swap altogether.
- The `paraswapData` is directly decoded into `buyCalldata` and `augustus`. This data can be manipulated by an attacker as they have control over unsanitized `paraswapData`.
- After the swap attempt, the function does not reduce or check the allowance for `assetToSwapFrom`, leaving the allowance unchanged even if the swap failed or was bypassed.
- The attacker then exploited the unchecked token allowance for `assetToSwapFrom` to withdraw tokens from the contract, bypassing the intended swap logic and executing unauthorized fund transfers.
- According to data from DeFiLlama, Aave, which holds assets valued at over $11 billion, has confirmed that the attack, which began around 04:30 UTC, did not jeopardize any user funds. Both founder Stani Kulechov and governance delegate Marc Zeller reassured users via X.
Mitigation and Best Practices:
- Implement validation checks on `paraswapData` before decoding and executing it to ensure it adheres to expected formats and values
- Implement logic to adjust or revoke token allowances after the swap, regardless of whether the swap operation succeeds or fails. Additionally, verify the success and correctness of the swap by checking the token balances before and after the transaction.
- Minimize interactions with external contracts by implementing a strict whitelist and performing rigorous checks on any external contract calls to avoid unexpected behavior.
- Always validate your code by writing comprehensive test cases that cover all the possible business logic.
To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Our public audit reports can be found on https://github.com/Credshields/audit-reports. Schedule a call at https://credshields.com/
· Scan your Solidity contracts against the latest common security vulnerabilities with 225+ detections at SolidityScan.
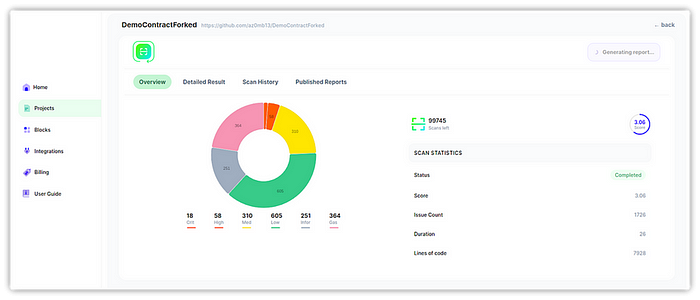
Conclusion:
SolidityScan is an advanced smart contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
