Penpie Hack Analysis
Penpie Hack Analysis
Overview:
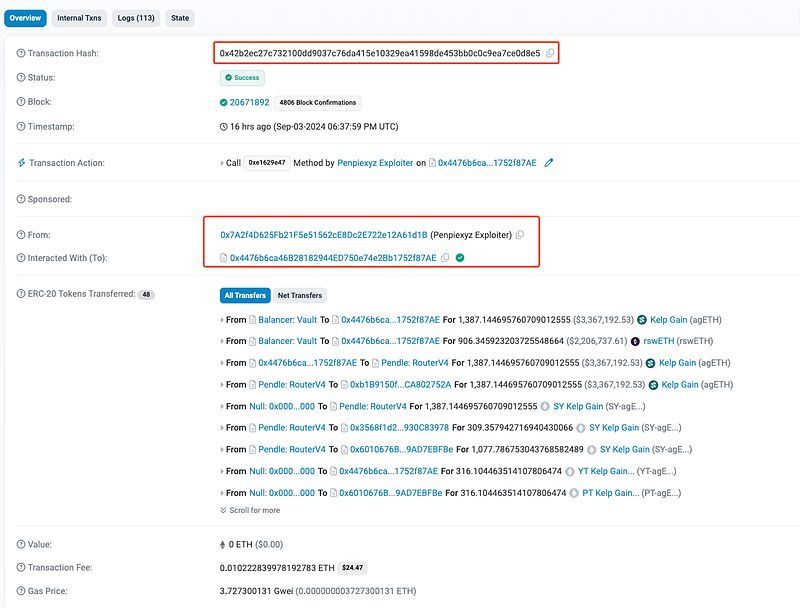
On September 3rd, 2024, Penpie (@Penpiexyz_io), a farming protocol built on top of the Pendle Protocol, suffered a reentrancy attack resulting in a significant loss of approximately $27 Million USD. The attack exploited a critical vulnerability in the Penpie Staking contract, specifically the `_harvestBatchMarketRewards` function. This function lacked proper reentrancy protection, allowing the attacker to reenter the contract during its execution and manipulate the reward distribution mechanism to their advantage.
Smart Contract Hack Overview:
- Attack Transactions: 0x42b2e, 0x7e7f9, 0x56e09
- Attacker’s Address: 0x7A2f4
- Stolen Funds held by: 0x2f2dD
Decoding the Smart Contract Vulnerability:
· The root cause of the vulnerability is that the `_harvestBatchMarketRewards()` function lacks a reentrancy guard, which is crucial for preventing reentrant calls during its execution.
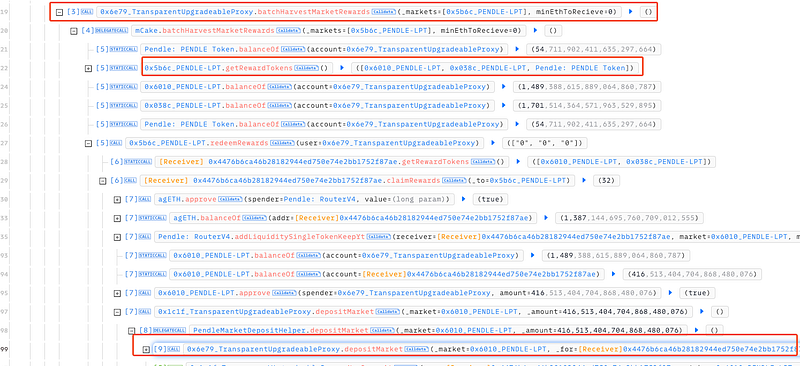
· The function executes token transfers and rewards calculations based on balances before and after calling the `redeemRewards()` function. The attacker exploited this by reentering the function during the `redeemRewards()` execution to manipulate the token balances and inflate the rewards as shown in flow above.
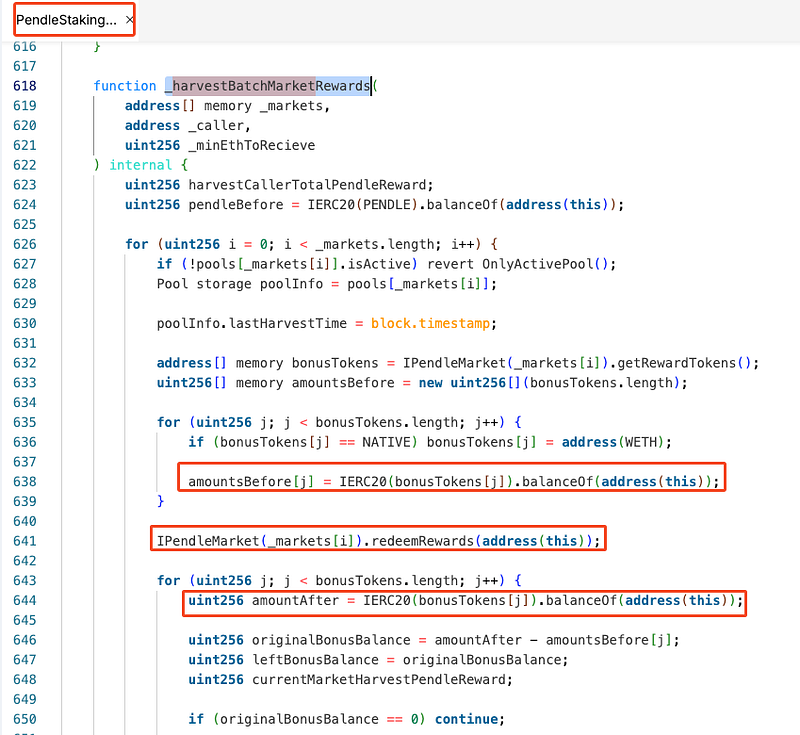
· The rewards are computed based on the difference in token balances before and after the redeemRewards() function call `(amountAfter — amountsBefore[j])`. The attacker can deposit additional tokens in the redeemRewards() function to increase the amountAfter balance, thereby inflating the reward amount. This exploitation allowed the attacker to withdraw more rewards than they were entitled to.
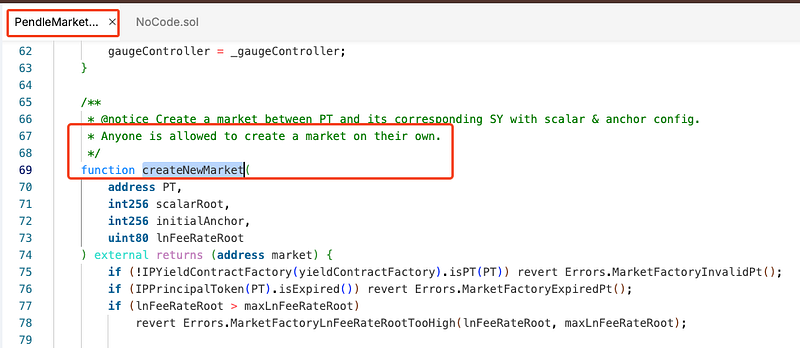
· The attacker had created a counterfeit SY (Standardized Yield) token contract and registered it as a valid market on the Pendle Protocol using the `PendleMarketFactoryV3`. This market was then used to exploit the `_harvestBatchMarketRewards()` function.
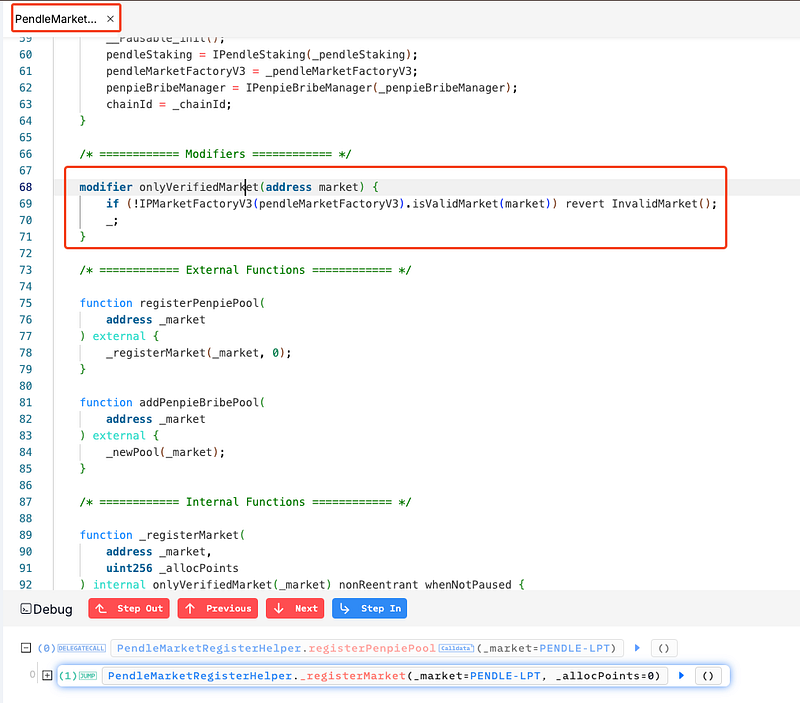
· Here, the function `_harvestBatchMarketRewards()` relies on the `getRewardTokens()` function of the market to determine the reward tokens. Since the market used by the attacker was created with a fake SY token, the protocol’s validation checks (i.e., pendleMarketFactoryV3.isValidMarket()) failed to prevent this exploitation. The isValidMarket check was ineffective because anyone could create a market with the factory, bypassing the expected validation logic.
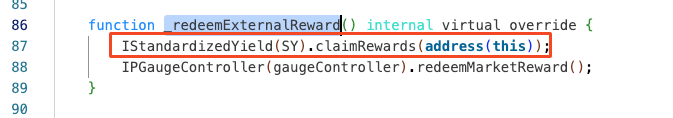
· The `redeemRewards()` function triggered by the attacker’s call allowed for token deposits during reward calculation. The absence of reentrancy protection enabled the attacker to reenter the contract, deposit tokens, and increase the reward amount based on the inflated balance, further worsening the loss.
· Co-Founder of Pendle clarified that the assets on Pendle itself were unaffected and secure. The exploit targeted Penpie, an independent protocol built on top of Pendle. The Pendle team acted swiftly to provide assistance and safeguard the assets, successfully protecting $107 million. Details are provided here.
Mitigation and Best Practices:
· In this scenario, adding a reentrancy guard to the `_harvestBatchMarketRewards` function by using a mutex lock to prevent reentrant calls would help protect it.
· Improve the validation mechanisms for market authenticity to ensure that only verified and legitimate markets are registered and utilized within the Pendle protocol. Implement centralized or permissioned controls for market registration to prevent the use of fraudulent or malicious markets.
· Ensure that all state changes (effects) are made before interacting with external contracts (interactions). This pattern helps to mitigate reentrancy attacks by minimizing the chance of external calls modifying the contract’s state unexpectedly.
· Always validate your code by writing comprehensive test cases that cover all the possible business logic.
· To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Our public audit reports can be found on https://github.com/Credshields/audit-reports. Schedule a call at https://credshields.com/
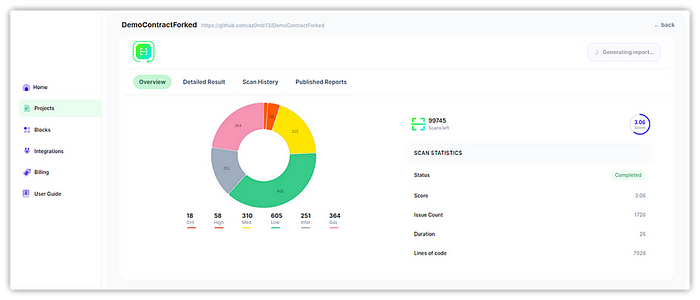
· Scan your Solidity contracts against the latest common security vulnerabilities with 225+ detections at SolidityScan.
Conclusion:
SolidityScan is an advanced smart contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
