NumaMoney Hack Analysis
NumaMoney Hack Analysis
Overview:
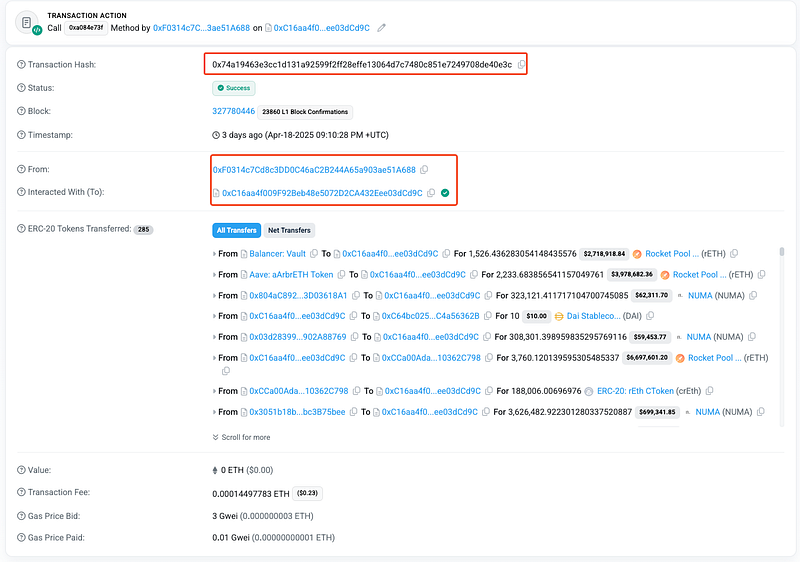
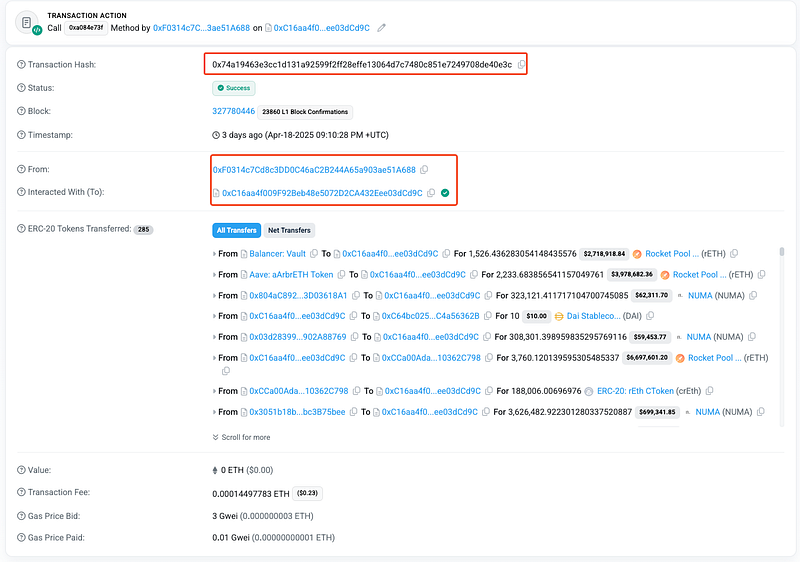
On April 18, 2025, the Numa protocol (@numamoney), a non-custodial and decentralized LST-backed synthetics protocol on the Arbitrum ($ARB) chain, suffered a sophisticated exploit. The attacker leveraged a price manipulation scheme using a flash loan from Aave V3, Balancer Vault and Uniswap V3 pools. The exploit targeted the NumaVault contract, manipulating the NUMA token price to enable excessive borrowing and collateral withdrawal, stealing ~$527,328 from the victim address. This vulnerability falls under OWASP SC02:2025 Price Oracle Manipulation.
Numa’s official response confirms the price manipulation, collateral removal, and ongoing investigation. Read more- here.
Smart Contract Hack Overview:
- Attack Transaction: 0x74a19
- Attacker’s Address: 0xF0314
- Victim’s Address: 0x3051b
- Exploit Contract: 0xC16aa
- OWASP SC Top 10: SC02:2025 Price Oracle Manipulation.
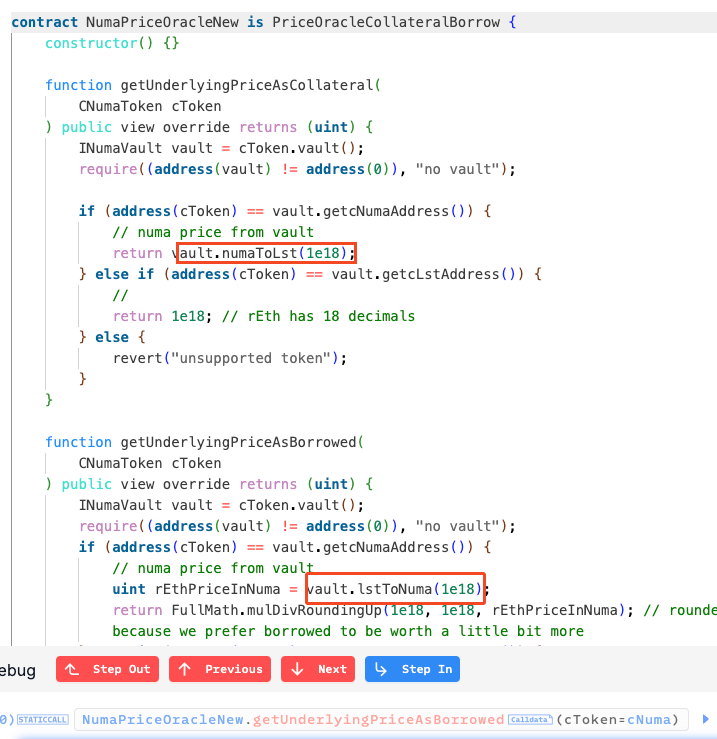
Decoding the Smart Contract Vulnerability:
- The root cause of the NumaMoney exploit lay in a critical lack of real-time price validation and slippage protection within the
NumaVaultcontract’ssell()function. This flaw allowed the attacker to manipulate thelast_lsttokenvalueWeivariable using a massive flash loan, bypassing the protocol’s zero-slippage trading promise.
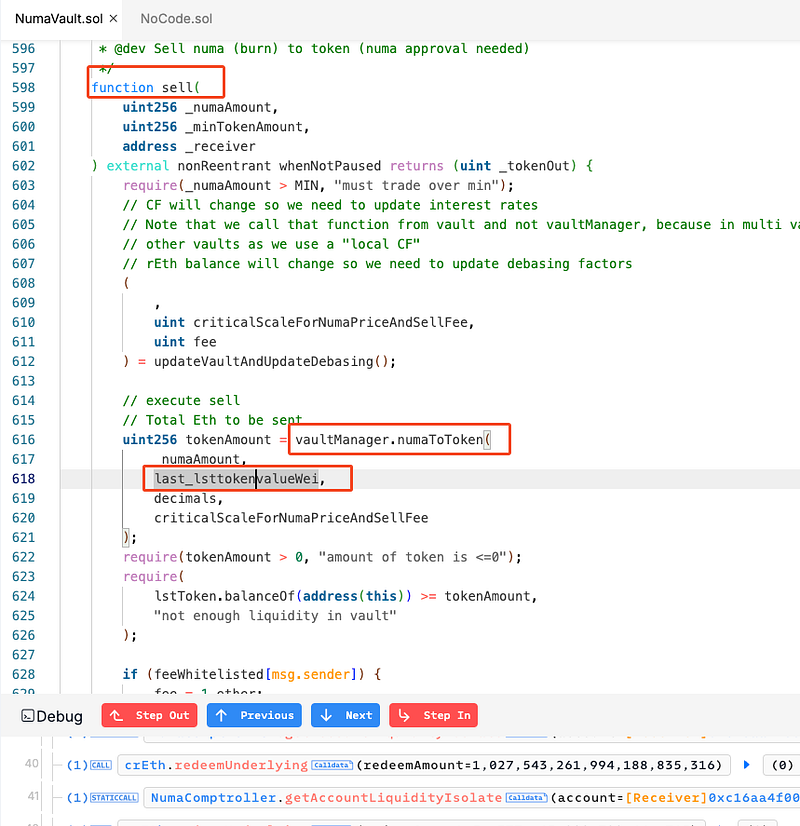
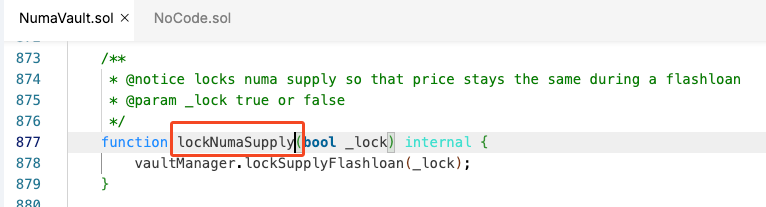
- The
lockNumaSupply()function—intended to stabilize native yield—was exploited to freeze the manipulated price, amplifying the attack.
- Additionally, NumaMoney’s reliance on internal
NumaPriceOracleNewdata without external validation left it vulnerable to this sophisticated flash loan attack. - Both functions rely on
INumaVaultmethods (numaToLst()andlstToNuma()), which use the manipulatedlast_lsttokenvalueWeifromsell(). The absence of external oracle integration creates a circular dependency, allowing the skewed price (trace shows a shift from148,850,422,003,959to116,943,924,501,586post-sell()) to propagate without validation. TheFullMath.mulDivRoundingUp()rounding further favored the attacker by inflating borrowed asset values.
- The attacker called
sell()with a massive NUMA amount, skewinglast_lsttokenvalueWei. This propagated toNumaPriceOracleNew, enabling downstream exploitation. The lack of real-time checks was the entry point. - During the flash loan,
lockNumaSupply(true)was invoked, ensuring the skewedlast_lsttokenvalueWeipersisted, preventing yield-driven rebalancing. - After the price manipulation and freezing, the attacker redeemed rETH using
CNumaLst.redeemFresh(), exploiting the inflated exchange rate from the manipulatedNumaPriceOracleNewdata. They then donated 150 rETH to the vault, further skewing the$NUMAprice to facilitate profit extraction, and repurchased 85,511$NUMAviaNumaVault.buyNoMax()at the artificial price, locking in approximately$529,102.12in profits.
Attack Flow:
Flash Loan and Deposit: The attacker secured 3,760
rETHand 631,422$NUMAvia flash loans (Aave V3,Balancer,Uniswap V3,apNUMA), depositedrETHinto Numa, and mintedcrEthusingNumaComptroller.enterMarkets, exploiting the lack of flash loan safeguards.
Borrowing and Transfer: They borrowed 3,626,482
$NUMAviaCNumaLst.borrowFreshNoTransfer, which lacked supply caps and relied on manipulablevault.getMaxBorrow()pricing fromNumaPriceOracleNew, transferring it to Address #2 (0x8594a) to mintcNUMA, repeated five times.
Price Manipulation and Freezing: Then, the attacker borrowed another 3,626,482
$NUMA, calledNumaVault.sell()to crash the price (exploiting no slippage protection inlast_lsttokenvalueWei), propagated the skewed price toNumaPriceOracleNewviavault.numaToLst(), donated150 rETHto manipulate further, and froze it withlockNumaSupply(true).
Redemption and Repurchase: They redeemed 283
rETHviaCNumaLst.redeemFresh, exploiting inflatedexchangeRateStoredInternal(), repurchased 85,511$NUMAwithNumaVault.buyNoMax, and Address #2 redeemed remaining collateral, mischaracterized as liquidation.
Final Extraction and Laundering: Address #2 borrowed 131
rETH, and the attacker swapped assets toETH, bridged them viazkBridge/Meson, and deposited them intoTornado Cash, exploiting the lack of withdrawal monitoring.
Mitigation and Best Practices:
- To mitigate future exploits, NumaMoney should integrate reputed oracles into
NumaPriceOracleNewfor real-time price validation, add slippage protection toNumaVault.sell()to prevent price crashes, and implement circuit breakers to halt trading during anomalies. - Introduce strict supply caps and per-block mint/borrow limits in
CNumaLst.borrowFreshNoTransfer()andbuyNoMax()to restrict how much synthetic $NUMA can be minted or borrowed per transaction or block. - Add a circuit breaker mechanism to halt trading (e.g., sell/mint/borrow/redeem) if price deviation exceeds a configured threshold, triggered on abnormal movement of
last_lsttokenvalueWeior exchange rates. - To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Our public audit reports can be found on https://github.com/Credshields/audit-reports. Schedule a call at https://credshields.com/
- Scan your Solidity contracts against the latest common security vulnerabilities with 494+ detections at SolidityScan.
Conclusion:
SolidityScan is an advanced smart contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
