KiloEx Vault Hack Analysis
KiloEx Vault Hack Analysis

Overview:
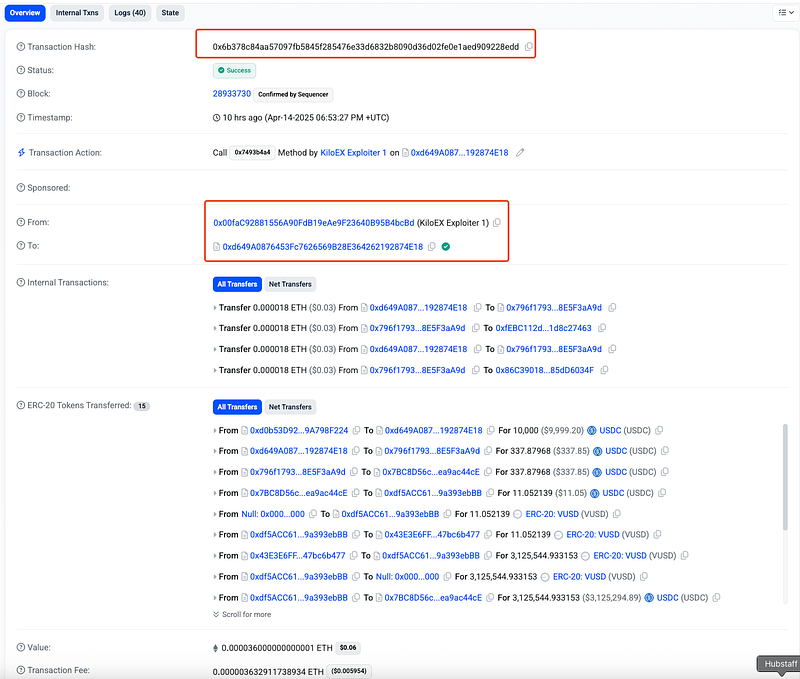
On April 14, 2025, KiloEx (@KiloEx_perp) , a decentralized perpetual trading platform operating on BNB, Base, and Taiko, suffered a coordinated exploit resulting in losses of over ~$7.4 million (~$3.3M in Base, ~$1M in BSC and ~$3.1M in opBNB). The attacker leveraged a critical access control vulnerability (OWASP SC01)in the MinimalForwarder contract to spoof trusted roles via a crafted signature, granting unauthorized access to the setPrices() function in the KiloPriceFeed contract.
This manipulation allowed the attacker to control oracle prices and drain funds by exploiting position openings and closings at manipulated price levels.
Smart Contract Hack Overview:
- Attack Transactions: Base- 0x6b378 , 0xde7f5 , BSC– 0x38b25 , 0x1aaf5
- Attacker’s Address: 0x00faC
- Victim’s Address: 0xdf5AC
- Attacker Funded From: 0x00faC
- OWASP SC Top 10: SC01:2025 Access Control Vulnerabilities
Decoding the Smart Contract Vulnerability:
- The root cause of the KiloEx exploit was a missing access control check in the
MinimalForwardercontract, which allowed the attacker to chain privileged calls through multiple contracts (PositionKeeper → Keeper → KiloPriceFeed) and ultimately manipulate oracle prices viasetPrices()— a critical function meant only for trusted actors (Keepers). - The attacker exploited this flaw to artificially set token prices, open a leveraged position at a favorable rate, and close it at a manipulated price, realizing substantial profits.
- The exploit involved a chain of smart contracts, each playing a role in enabling the attack:
MinimalForwarder Contract: A contract designed to forward transactions to other smart contracts. However, it lacked proper access control and signature validation, which was key to the exploit.
PositionKeeper Contract: This contract is responsible for managing positions and executing trades.
Keeper Contract: The Keeper contract interacts with the oracle and updates token prices via the
setPrices()function.
KiloPriceFeed Contract: Contains the oracle price data and the critical
setPrices()function that was manipulated by the attacker.
- The execute() function in the MinimalForwarder allowed users to pass a
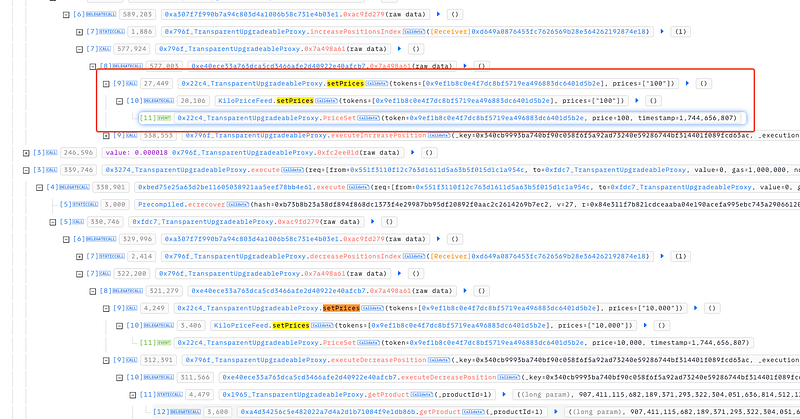
fromaddress and a signature. The attacker was able to forge valid signatures and bypass security checks, allowing arbitrary calls to other contracts. - The 0xac9fd279 function in PositionKeeper is designed to pass control to the Keeper contract to trigger actions like price manipulation and position changes. Under normal circumstances, only trusted entities should be able to initiate such processes, but this was circumvented due to flaws in MinimalForwarder.
- Once the long position was open, the attacker increased the token price to an inflated level. The setPrices() function was used to manipulate the price again, and at this inflated price, the attacker closed the long position. By doing so, the attacker gained significant profits from the price difference, exploiting the gap created by their manipulation.
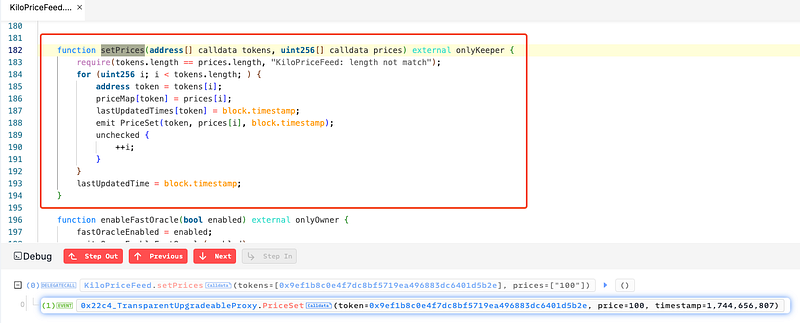
- The function
setPricesallows the price data of multiple tokens to be updated in one call. It uses theonlyKeepermodifier, which restricts access to addresses that are designated as “keepers.” As theMinimalForwardercontract lacked proper access control checks on the signatures or the caller’s address, the attacker was able to impersonate akeeperor bypass signature validation, potentially triggering thesetPrices()function with arbitrary data. - The critical factor enabling the attack was the ability to chain privileged function calls. The MinimalForwarder contract’s execute() function allowed the attacker to pass arbitrary
fromaddresses and manipulate signatures, leading to an unbroken chain of function calls: - From MinimalForwarder → PositionKeeper → Keeper → KiloPriceFeed, all without triggering any security mechanisms.
Attack Mechanics Simplifcation: Price Manipulation:
The attacker first lowered the price of the asset by using the setPrices() function.
The attacker then opened a long position at this artificially low price, essentially acquiring more leverage.
Afterward, the attacker used the setPrices() function again to inflate the price of the asset.
With the inflated price, the attacker closed the position, gaining a significant profit from the price difference.
- The exploiter was funded via Tornado Cash prior to the attack. And now, the stolen funds are being bridged via zkBridge and Meson, indicating an attempt to obfuscate and launder the proceeds cross-chain.
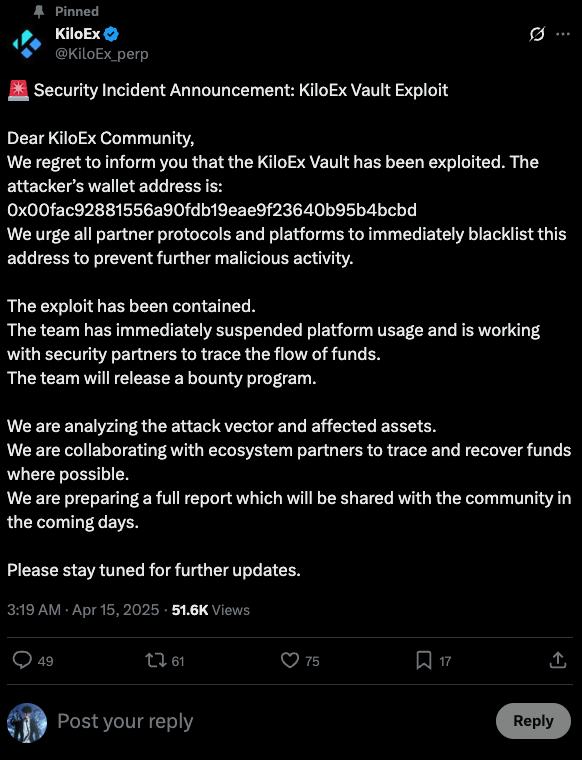
- The KiloEX team is actively collaborating with BNB Chain, Manta Network, and security firms including Seal-911, SlowMist, and Sherlock to investigate the breach.
- The protocol has been paused, the exploit has been contained and a bounty program is being prepared. A full official incident report is expected in the coming days.
- More details and updates can be found here: https://x.com/KiloEx_perp/status/1911899600849617330
Mitigation and Best Practices:
- Ensure only whitelisted and verified sources (e.g., Chainlink or internally validated feeds) can update price data. The
setPrices()function should: Use signature-based access control with non-replayable parameters (nonces, deadlines). - Enforce role gating via
AccessControlorOwnablelogic that cannot be bypassed through forwarded or proxy calls. - Do not allow MinimalForwarder or meta-transactions to execute sensitive calls like price setting or liquidation.
- If meta-transactions are essential, ensure
msg.senderis never blindly trusted. Always validate thesignerand match it against an authorized address list - To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Our public audit reports can be found on https://github.com/Credshields/audit-reports. Schedule a call at https://credshields.com/
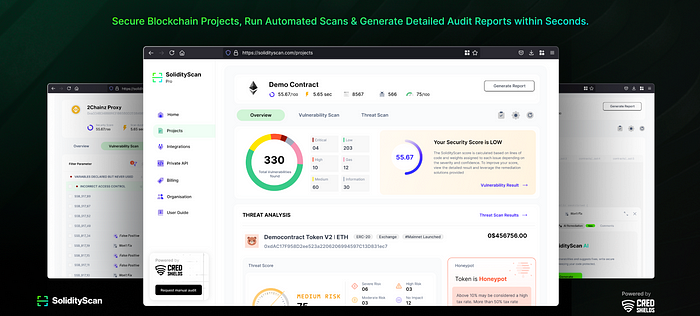
- Scan your Solidity contracts against the latest common security vulnerabilities with 494+ detections at SolidityScan.
Conclusion:
SolidityScan is an advanced smart contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
