Dynamic Finance Hack Analysis — Incorrect Deposit Logic
Dynamic Finance Hack Analysis — Incorrect Deposit Logic
Overview:
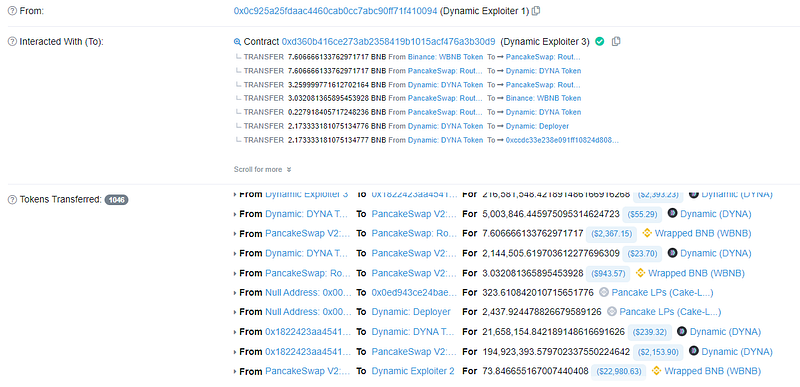
On February 22, 2023, 74 BNB of $DYNA tokens were lost as a result of a hack on the Dynamic Finance project at the BSC network. The deposit function logic contained flawed computations for claiming rewards upon deposits, which allowed the hackers to trick it.
Smart Contract Hack Overview:
- Attacker’s address: 0x0c925a25,0x35596bc5
- Attacker’s Transaction: 0xc09678fe
- Attacker’s Exploit Contract: 0xd360b4
- Vulnerable contract code: 0xa7B5eabC
- DYNA Official Contract: 0x5c0d011
Decoding the Smart Contract Vulnerability:
- During our investigation, we discovered that the StakingDYNA contract calculated interest based on the user’s initial deposit and saved it in the duration variable, which was then added to the staking information.
The formula used for interest calculation :
duration = now — lastProcessAt
interest = k * (stakeAmount * duration)
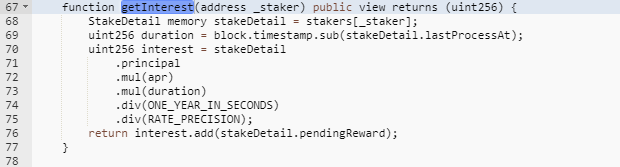
- The above ‘lastProcessAt’ amount was calculated using the deposit() function, which, as can be seen, only checks to see if a user has made a deposit for the first time. If the user has not made a deposit, the contract will calculate the interest based on the timestamp of the user’s first deposit, which was obtained from the stakeDetails structure.
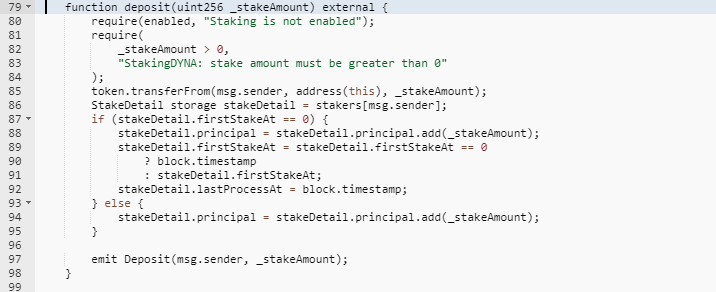
- The combination of the contract’s two weaknesses allowed an attacker to be rewarded with additional interest by just investing a modest amount and waiting a few days. The attackers took advantage of this weakness by exploiting it with flash loans and making large gains by tricking the smart contract.
Mitigation and Best Practices:
lastProcessAtshould be fair to all depositors on the contract and should award rewards based on individual deposits rather than on a user’s most recent deposit.- Verify that the
block.timestampis correctly set and reflects the current time. Note that theblock.timestampis the timestamp of the current block and may differ from the current time. - Ensure that the lastProcessAt variable of the stakeDetail struct has been correctly set to the last time the Staker’s information was updated.
- To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Schedule a call at https://credshields.com/
- Scan your Solidity contracts against the latest common security vulnerabilities with 130+ detection at SolidityScan including access control vulnerabilities.

Conclusion:
SolidityScan is an advanced smart-contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
SolidityScan — LinkedIn | Twitter | Telegram | Discord
