Dexible Hack Analysis — Never Blindly Trust Smart Contracts
Dexible Hack Analysis — Never Blindly Trust Smart Contracts
Overview
On February 17, 2023, a hack occurred on the Dex Aggregator platform called Dexible, resulting in a loss of 2 million dollars to users who allowed Dexible’s contract to exchange tokens on their behalf. The affected addresses primarily belong to 17 traders. In this blog post, we will provide an analysis of the hack and discuss mitigation strategies to prevent similar incidents in the future.
Smart Contract Hack Overview:
- Attacker’s address: 0x684083
- Attacker’s transaction: 0x138daa
- Dexible Vulnerable Contract: 0xde62e1
- Dexible Contract: 0x33e690

Decoding the Smart Contract Vulnerability:
- Dexible recently released v2 contracts that let users provide routing information to the selfSwap function in accordance with their own preferences. Each swap request was a
routethat specified which DEX to contact and what information should be sent to DEX in order to carry out the swap. - Because there were no checks to ensure that the router address was verified on-chain, attackers could pass any contract address, which they exploited by calling a token contract with
transferFromany account that had approval on the Dexible contract. - TokenID and router information were supplied as caller data when the attacker used the
selfSwap()method. Further modifications to the call data were sent to thefill()method, which lacked routerID validation and enabled attackers to submit the routerID of their owned contract address which was not verified on-chain.
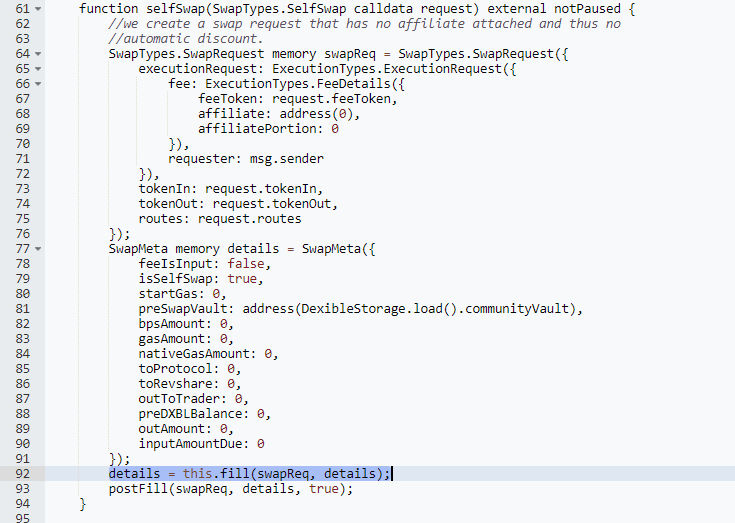
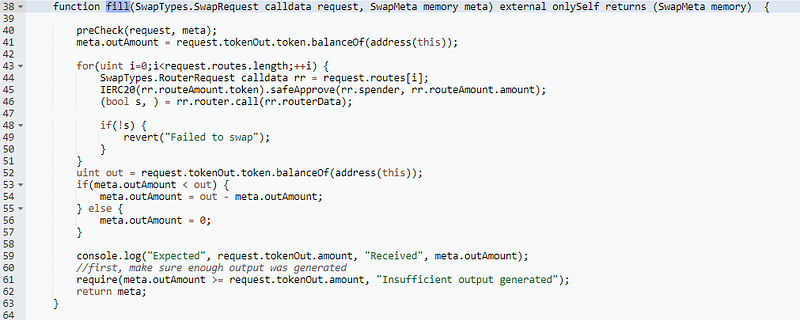
- For those users who had authorized the swap contracts to exchange tokens on their behalf, the
fill()function performed a delegate call to therouterDatapassed by the attacker and swapped the victim’s unspent already-approved tokens straight to the attacker’s account.
- This resulted in the breach of 17 user accounts and the loss of 2 million dollars to Dexible users.
Mitigation and Best Practices:
- The caller’s data must be thoroughly verified and validated.
- To prevent users from enabling attackers to alter the
routerIdto another router, implement whitelisting on the routers. - Use openZepplin libraries to implement access control mechanisms appropriately, ensuring that everything is secure and that there are no broken authorizations.
- Be aware of the number of tokens you are approving for a contract and revoke approvals regularly.
- To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Schedule a call at https://credshields.com/
- Scan your Solidity contracts against the latest common security vulnerabilities with 130+ detection at SolidityScan including access control vulnerabilities.

Conclusion:
SolidityScan is an advanced smart-contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
SolidityScan — LinkedIn | Twitter | Telegram | Discord
