Bankroll Network Hack Analysis
Bankroll Network Hack Analysis
Overview:
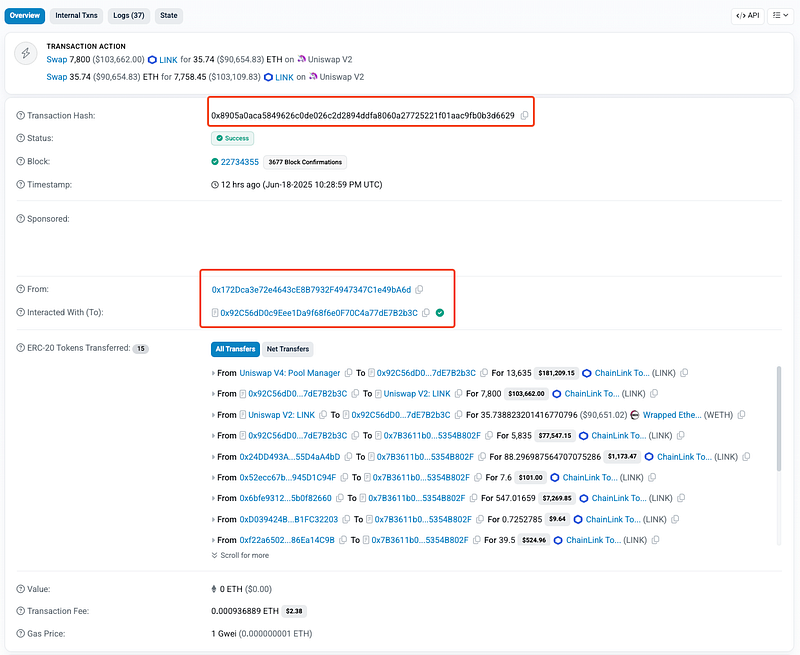
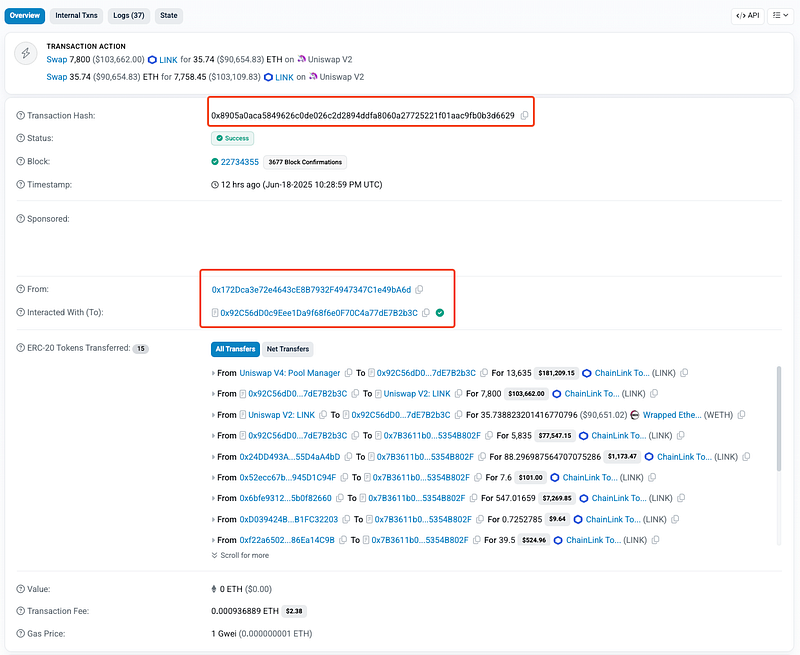
On June 19, 2025, a previously dormant DeFi protocol called Bankroll Network (@bankroll_status) — specifically, its BankrollNetworkStack contract—was exploited due to a critical integer underflow vulnerability in its sell() function. This vulnerability existed in contracts deployed on Ethereum Mainnet and Binance Smart Chain (BSC). The attacker exploited this flaw to manipulate dividend accounting and drain funds from users who had previously interacted with or approved the contract. The attack has resulted in an approximate loss of $65,000 so far. This vulnerability is an example of OWASP SC08:2025 — Integer Overflow and Underflow.
Bankroll Network was previously exploited for nearly $235K on September 23rd, 2024. Read more here: https://blog.solidityscan.com/bankroll-network-hack-analysis-e77fd8442dfa
Smart Contract Hack Overview:
- Victim Contract: BSC:
0xAdEfb - Attack Transactions: Ethereum: 0x8905a , BSC: 0x7226b
- Attacker Addresses:
0x2deA4,0x172Dc - OWASP SC Top 10: SC08:2025 — Integer Overflow and Underflow
Decoding the Smart Contract Vulnerability:
- The root cause of the vulnerability lies in the
sell()function of theBankrollNetworkStackcontract. Thesell()function is intended to allow users to burn tokens in exchange for ETH-equivalents, update internal dividend trackers, and allocate exit fees. However, its internal logic failed to securely handle accounting updates, especially for signed integers. - The
sell()function directly subtracts a calculated signed integer value from a user’s payout balance without overflow or underflow protection:
payoutsTo_[_customerAddress] -= _updatedPayouts;
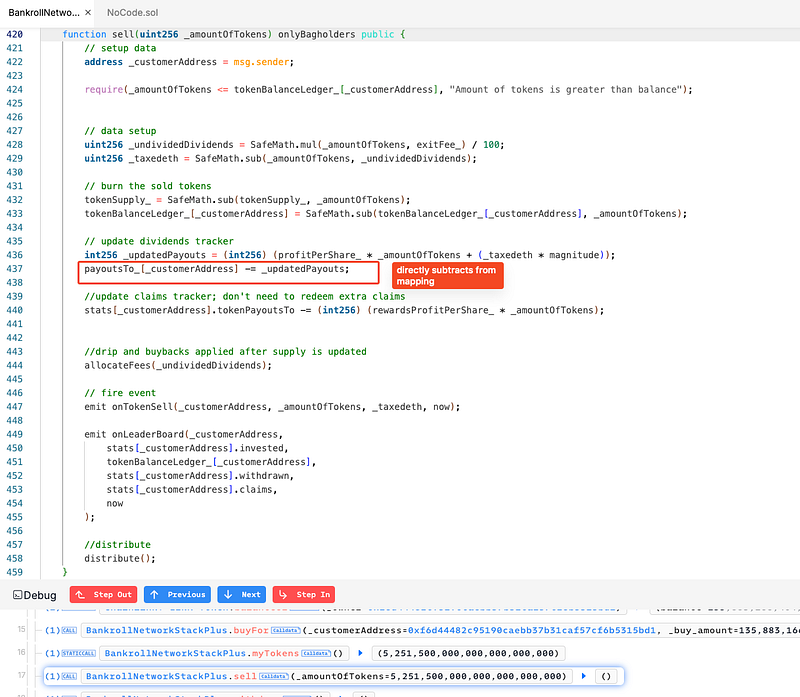
- In Solidity 0.6.8, such arithmetic on
int256types does not revert when an underflow occurs. This is unlike Solidity 0.8+, where built-in checks prevent such errors. - The contract was compiled with Solidity 0.6.8, a version in which integer overflow and underflow do not revert by default. As a result, attacker was able to exploit this legacy behavior to manipulate contract state.
- Users who have interacted with the compromised Bankroll contracts are strongly advised to immediately revoke token approvals to prevent unauthorized withdrawals.
- If you have previously approved any of the following BSC contract addresses, revoke permissions as soon as possible:
0x16d0a151297a0393915239373897bcc955882110
0xAdEfb902CaB716B8043c5231ae9A50b8b4eE7c4e
0x0a15B914388d48d77fE70c8a832cD992dD05e76E
0x313E71df70b106BD8e456cfbAfd3583595EdE490
0xeF6676536a1d98942d149f52708770e11Db47BcE
Mitigation and Best Practices:
- Upgrade all smart contracts to Solidity version 0.8.0 or later, which includes automatic overflow and underflow checks for both
uintandinttypes, eliminating silent arithmetic errors like the one exploited in this attack. - If using older Solidity versions is unavoidable, implement or import a
SafeMathIntlibrary to securely handle arithmetic operations onint256values, ensuring overflows/underflows revert safely. - Add explicit state transition validations (e.g., bounds checks on payouts and balances) to ensure logical consistency and prevent arithmetic or accounting manipulation.
- To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Our public audit reports can be found on https://github.com/Credshields/audit-reports. Schedule a call at https://credshields.com/
- Scan your Solidity contracts against the latest common security vulnerabilities with 494+ detections at SolidityScan.
Conclusion:
SolidityScan is an advanced smart contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
