Bankroll Network Hack Analysis
Bankroll Network Hack Analysis
Overview:
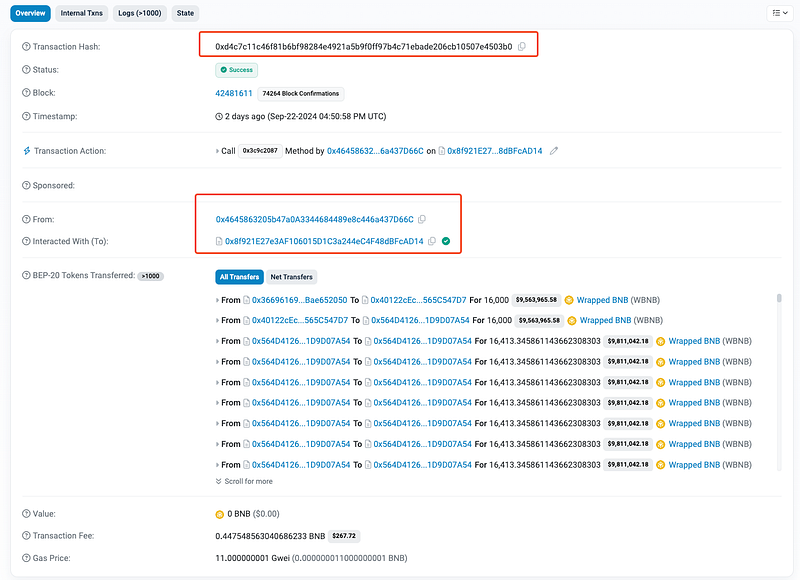
On September 23rd, 2024, the Bankroll Network (@Bankroll_Status), was exploited resulting in the loss of $235K (~404 WBNB) due to a vulnerability in its token sale contract. The exploit was enabled by a flaw in the `buyFor` function, which allowed the attacker to manipulate the contract and profit significantly without sending any WBNB tokens.
Smart Contract Hack Overview:
- Attack Transaction: 0xd4c7c
- Attacker’s Address: 0x46458
- Malicious Contract: 0x8f921
- Vulnerable Contract: 0x564D4
Decoding the Smart Contract Vulnerability:
· The root cause is that the token sale contract’s `buyFor` function allowed any user to set the `_customerAddress` to the victim contract’s address, enabling manipulation of the `profitPerShare_` variable without sending WBNB.
· The token sale contract was designed to allow token purchases through a `buyFor` function, enabling users to buy tokens on behalf of others. This function took a parameter `_customerAddress` to specify the recipient of the tokens.
· The implementation did not include proper validation for the `_customerAddress` parameter. Specifically, there were no restrictions to prevent the ` _customerAddress` from being set to the address of the token sale contract itself.
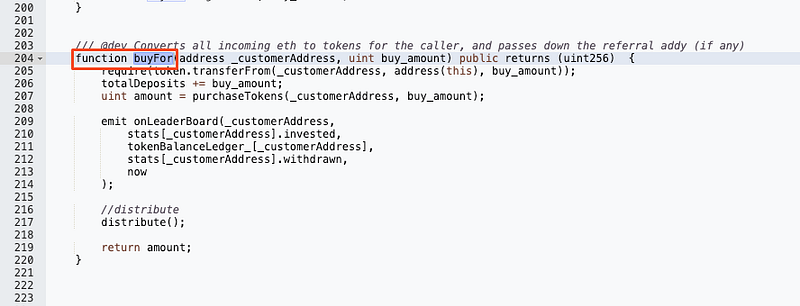
· And the line `require(token.transferFrom(_customerAddress, address(this), buy_amount));` allowed the transfer of tokens without sufficient checks on the sender’s balance when `src` is `msg.sender`. This was used during the attack.
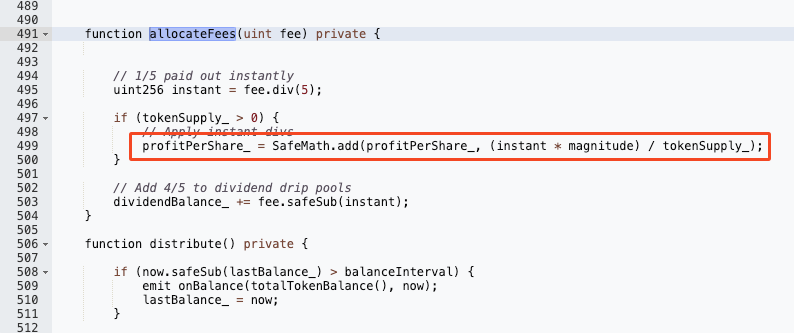
· The contract had a profit-sharing mechanism that relied on the `profitPerShare_` variable. When a user purchased tokens, the value of `profitPerShare_` would increase, rewarding token holders with WBNB based on their share.

· The attacker repeatedly called the `buyFor` function, transferring WBNB (Wrapped BNB) from the contract to themselves. Each call increased the `profitPerShare_` variable significantly without the need for actual WBNB tokens. The attacker exploited the fact that calling `buyFor` for the victim contract allowed for artificial inflation of `profitPerShare_`.
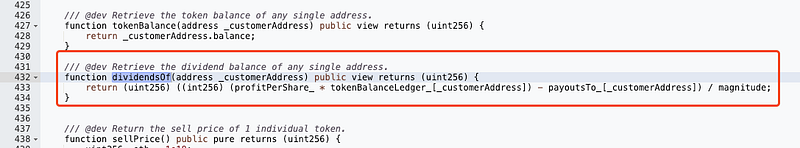
· The `dividendsOf` function calculates the dividend owed to a specific address using the manipulated `profitPerShare_`. By inflating this value, the attacker artificially increases their dividends, which can then be withdrawn.
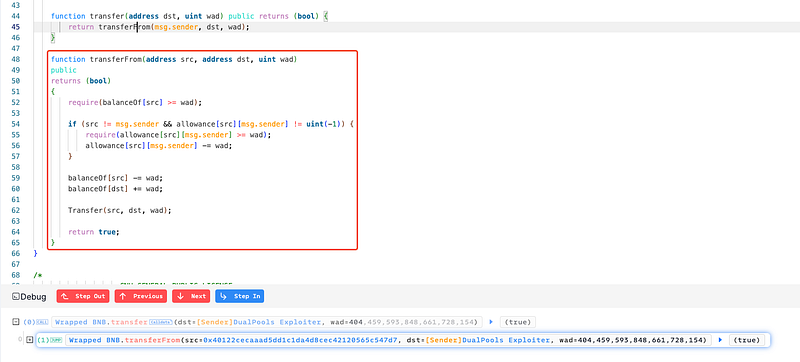
· Setting `_customerAddress` to the token sale contract itself then enabled the attacker to invoke `transferFrom` without any actual transfer of WBNB.
· After inflating `profitPerShare_`, the attacker was able to withdraw a large amount of WBNB tokens compared to their initial investment.
· The attack resulted in the hacker withdrawing $235,000, representing a significant profit at the expense of other users.
Mitigation and Best Practices:
· Implement strict validation checks in the `buyFor` function to ensure that `_customerAddress` cannot be set to the address of the token sale contract itself or any other unauthorized addresses.
Enhance the logic in the `transferFrom` and `buyFor` functions to ensure sufficient checks are in place to verify the sender’s balance and allowance.
· Implement robust access control mechanisms to restrict who can invoke critical functions. Utilize roles or ownership patterns to ensure that only authorized addresses can perform sensitive operations. Use modifiers to enforce access control, such as onlyOwner or role-based access control patterns using libraries like OpenZeppelin.
· Always validate your code by writing comprehensive test cases that cover all the possible business logic.
· To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Our public audit reports can be found on https://github.com/Credshields/audit-reports. Schedule a call at https://credshields.com/
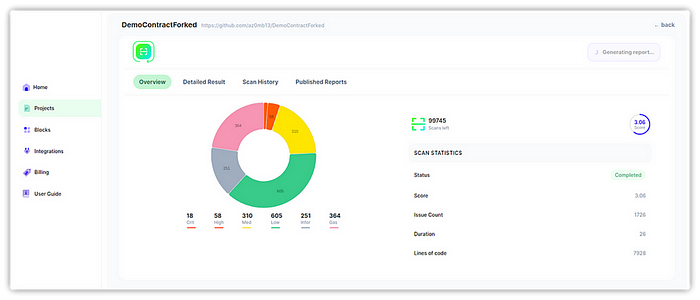
· Scan your Solidity contracts against the latest common security vulnerabilities with 225+ detections at SolidityScan.
Conclusion:
SolidityScan is an advanced smart contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
