Zoth Hack Analysis
Zoth Hack Analysis
Overview:
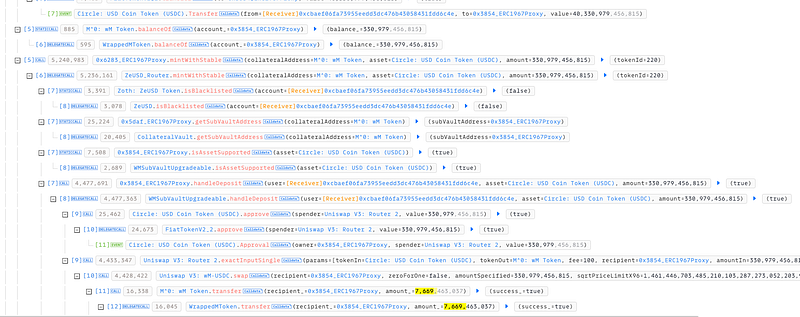
On March 1, 2025, Zoth (@zothdotio), a restaking layer for real-world assets (RWAs), suffered an exploit resulting in a loss of approximately $285,000. The attacker exploited a logic flaw (SC03: Logic Errors)in the LTV (Loan-To-Value) validation within the mintWithStable() function. The attacker manipulated Uniswap V3 liquidity pools to exploit an incorrect calculation of collateral received after a swap, allowing them to mint ZeUSD without depositing sufficient collateral.
Smart Contract Hack Overview:
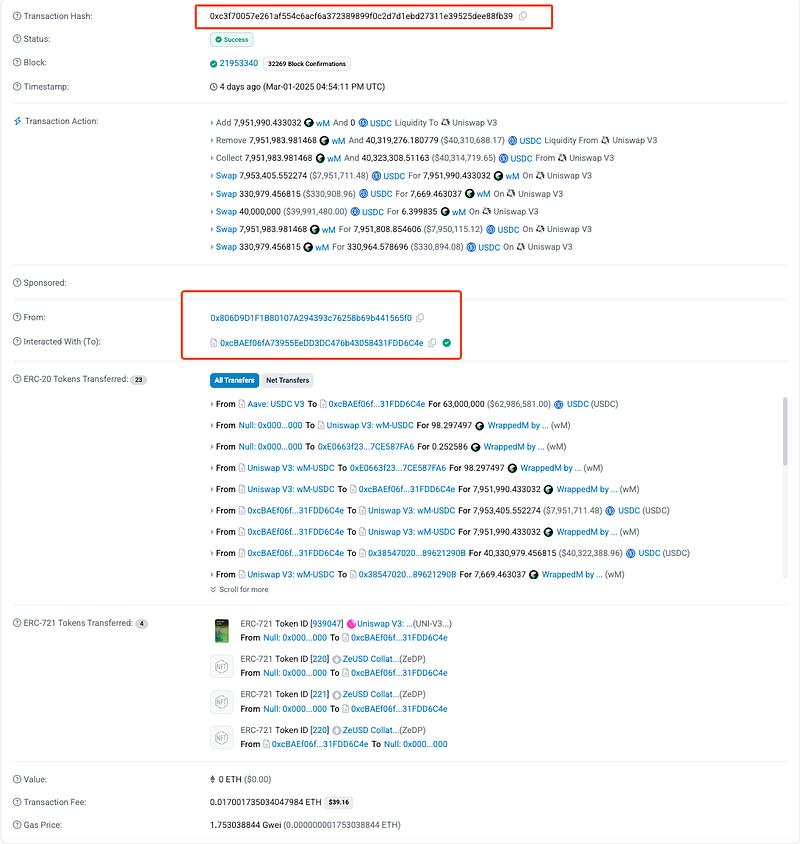
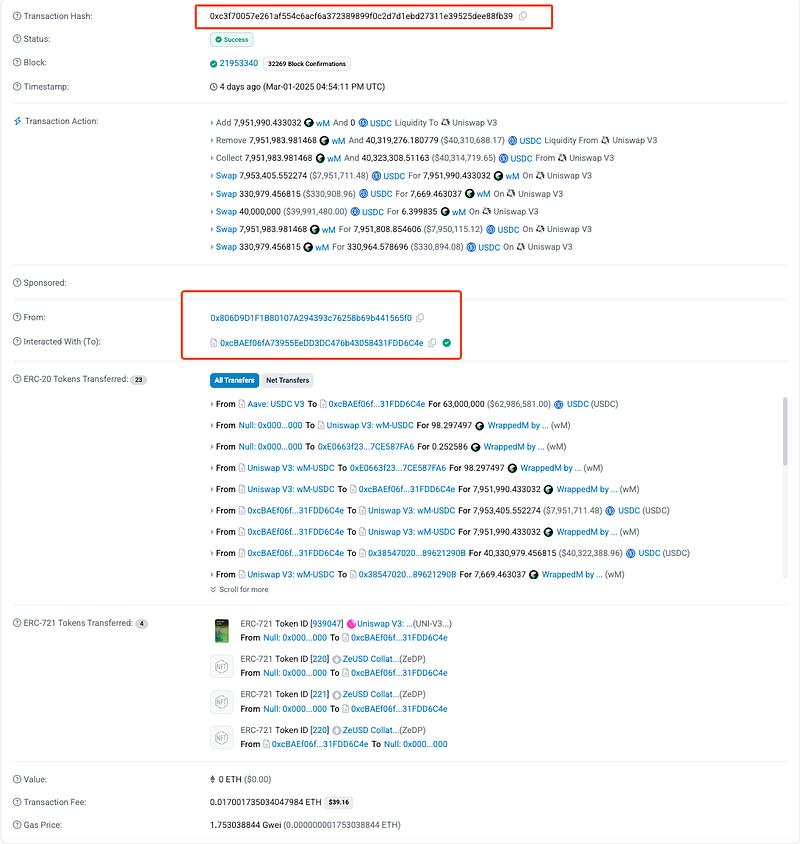
- Attack Transaction: 0xc3f70
- Attacker’s Address: 0x806D9
- Zoth Contract’s Address: 0xe2574
- OWASP SC Top 10: SC03: Logic Errors
Decoding the Smart Contract Vulnerability:
- The root cause of the exploit was a logic flaw in the Loan-to-Value (LTV) validation within the
mintWithStable()function, which incorrectly used the user’s deposit amount instead of the actual collateral received after the swap, allowing the attacker to manipulate Uniswap V3 liquidity and mint ZeUSD without sufficient backing. - The
mintWithStable()function enables users to deposit stablecoins (e.g., USDC) to receive ZeUSD. Internally, these stablecoins are swapped for collateral (e.g., wM tokens), and the amount of collateral received is used to determine how much ZeUSD can be minted based on LTV rules. - The Loan-to-Value (LTV) ratio is supposed to ensure users mint ZeUSD only up to a certain percentage of the collateral deposited.
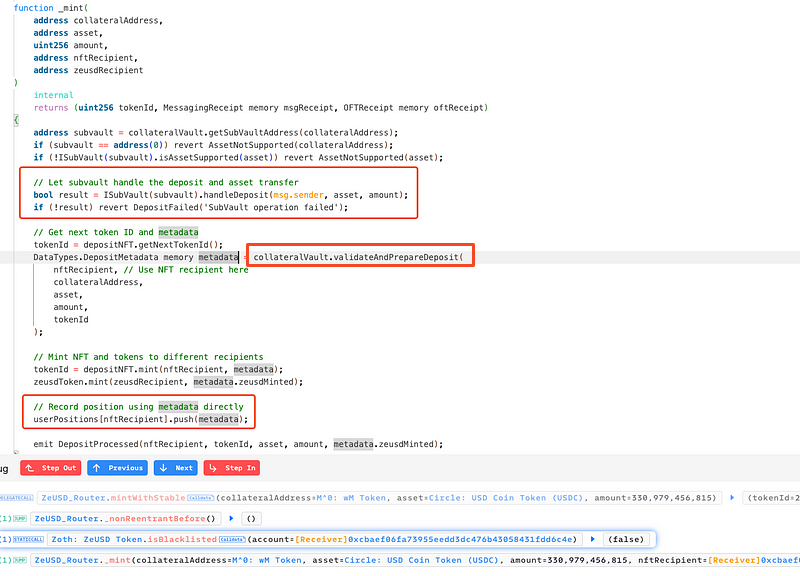
- The
mintWithStable()function calls_mint(), which relies onISubVault(subvault).handleDeposit()to deposit stablecoins and swap them for the required collateral. However, the validation logic contained a critical flaw:
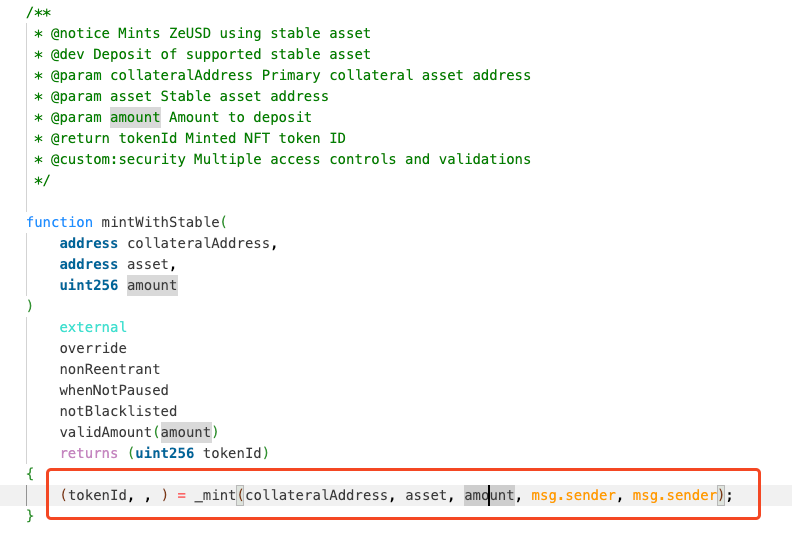
mintWithStable() Function- LTV was validated using
amount(the initial stablecoin deposit) instead of the actual collateral received (collateralReceived) after the swap. - As the attacker manipulated the Uniswap V3 pool, the swap would return far fewer collateral tokens than expected. However, the contract would still assume full collateralization based on
amount. - The contract did not enforce slippage tolerance or post-swap collateral validation, meaning that even if the swap resulted in fewer collateral tokens than expected, the system blindly assumed full collateralization and credited the attacker with an inflated collateral value.
- The
metadatastorage also recorded an inflated collateral value, allowing the attacker to later withdraw an amount of collateral that was never actually deposited. - The
validateAndPrepareDeposit()function in_mint()failed to verify the LTV correctly. It blindly assignedmetadata.zeusdMinted, enabling the attacker to mint more ZeUSD than they should have. - As a result, the attacker was able to mint significantly more ZeUSD than they were entitled to, despite not having sufficient collateral backing.
Attack Methodology:
The attacker manipulated the Uniswap V3 pool to distort the swap rates. This caused the swap to return far fewer collateral tokens than expected.
They then called
mintWithStable(), depositing stablecoins, but due to the manipulated swap, they received only 7,669 collateral tokens while the system incorrectly recorded 330,979 as collateral.
Since the LTV validation used the incorrect
amount, the attacker was able to mint ZeUSD as if they had provided 330,979 collateral tokens instead of the actual 7,669.
Finally, the attacker burned ZeUSD to withdraw the recorded 330,979 collateral tokens, profiting $285k from the mismatch.
Mitigation and Best Practices:
- Ensure the LTV check is based on the actual
collateralReceivedafter the swap rather than the initial deposit amount. Implement a strictrequirestatement that validates whether the received collateral meets the minimum required backing before minting ZeUSD. - Introduce a tolerance check (e.g., 99% threshold) to reject transactions where the received collateral is significantly lower than expected.
- Integrate Chainlink or other decentralized oracles to fetch real-time collateral prices and validate LTV ratios dynamically.
- Enforce slippage limits on swaps to prevent price manipulation and ensure users receive the correct amount of collateral.
- To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Our public audit reports can be found on https://github.com/Credshields/audit-reports. Schedule a call at https://credshields.com/
- Scan your Solidity contracts against the latest common security vulnerabilities with 494+ detections at SolidityScan.
Conclusion:
SolidityScan is an advanced smart contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
