WazirX Hack Analysis
WazirX Hack Analysis
Overview:
On July 18th, 2024, WazirX (@WazirXIndia)- one of the biggest Indian Cryptocurrency exchange fell victim to an attack as one of their self-custody multi-sig wallets was compromised, resulting in a loss of approximately $230 Million.
Smart Contract Hack Overview:
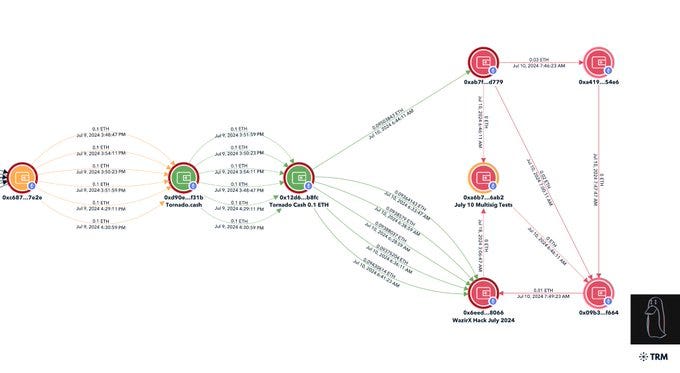
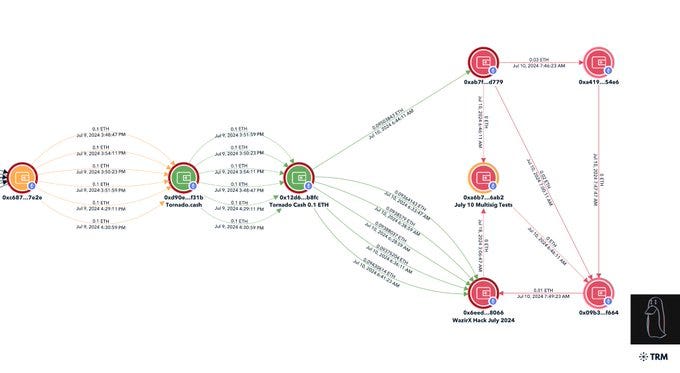
Attacker’s Address: 0x6eedf
Related Address Chain (Stolen fund is in these addresses): 0x04b21, 0x35feb, 0x90ca7, 0x36138
Malicious Contract Address used for phishing: 0xef279
Affected WazirX Address: 0x27fd4
Attack Transaction: 0x48164
Decoding the Smart Contract Vulnerability:
· The root cause is that the attackers upgraded the multi-sig wallet to a malicious contract, and made the wallet execute incorrect logic; which allowed them to drain the multi-sig.
· The attackers chose this method because directly draining would have required multiple transactions and signatures; which would have raised the risk of detection.
· They compromised private keys & phished two signatures of the multi-sig signers. One of the phished signatures was a pre-validated signature from Liminal Custody, indicating msg.sender authorization.
· The attacker used a delegate call to the malicious contract deployed 8 days prior to the attack.
· Delegate call data: 0x804e1f0a000000000000000000000000ef279c2ab14960aa319008cbea384b9f8ac35fc6, where ef279c (address) is a parameter.
· The delegate call targeted the function 0x804e1f0a, which modified `slot0` of the multisig proxy storage.
· Due to the nature of delegate calls, the multisig’s own slot0 was modified to point to a new implementation contract.
· Prior to the attack, slot0 contained the standard safe implementation address. After the delegate call, slot0 was updated to point to the new malicious contract address deployed by the attacker.
· The new implementation contract was designed to transfer assets out of the multi-sig wallet. Each subsequent transaction to the multi-sig triggered a delegate call to this malicious contract, enabling continuous draining of funds.
References: Twitter post by Mudit Gupta
Mitigation and Best Practices:
· Implement strict upgrade mechanisms for multi-sig wallets that require multiple layers of authentication and signatures for any contract upgrade.
·Implement time delays for contract upgrades with the ability to cancel if suspicious activity is detected.
· Always validate your code by writing comprehensive test cases that cover all the possible business logic.
· To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Our public audit reports can be found on https://github.com/Credshields/audit-reports. Schedule a call at https://credshields.com/
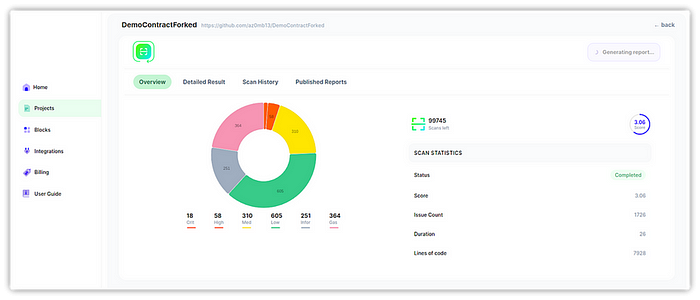
· Scan your Solidity contracts against the latest common security vulnerabilities with 225+ detections at SolidityScan.
Conclusion:
SolidityScan is an advanced smart contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
