Uwulend Hack Analysis
Uwulend Hack Analysis
Overview:
On June 10, 2024, UwuLend, a lending protocol, was hacked for $19.4 million due to an Oracle manipulation attack.
Smart Contract Hack Overview:
Decoding the Smart Contract Vulnerability:
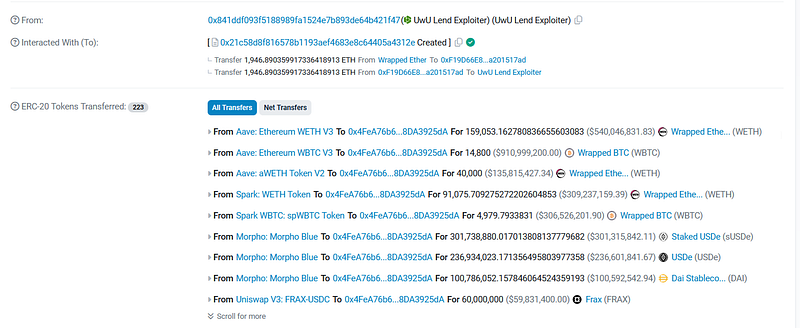
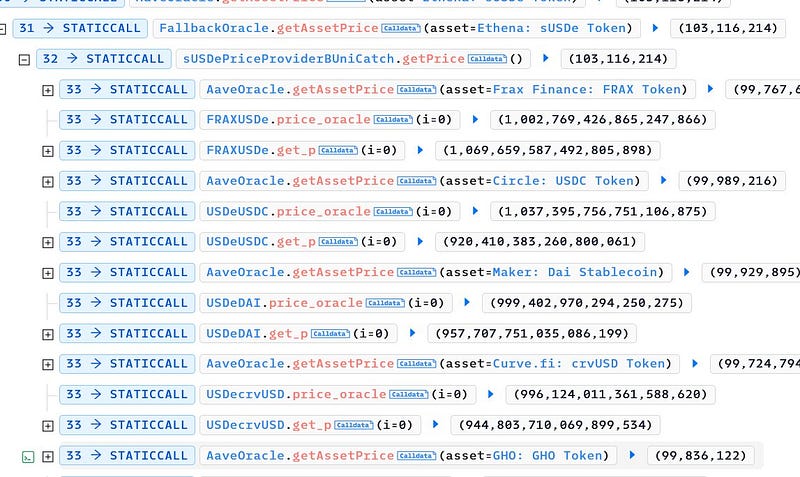
- The attack exploited a price discrepancy in UwuLend’s oracles through a series of transactions, utilizing a flash loan to manipulate the price feed.
- The attacker used a flash loan to manipulate the state of several Curve pools.
- The fallback oracle calculated prices based on the manipulated pool states.
- The attacker borrowed sUSDe at a manipulated low rate and liquidated at an inflated rate.
Mitigation and Best Practices:
- Avoid reliance on DEX prices as fallback oracles.
- Always validate your code by writing comprehensive test cases that cover all the possible business logic.
- To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Schedule a call at https://credshields.com/
- Scan your Solidity contracts against the latest common security vulnerabilities with 130+ detections at SolidityScan
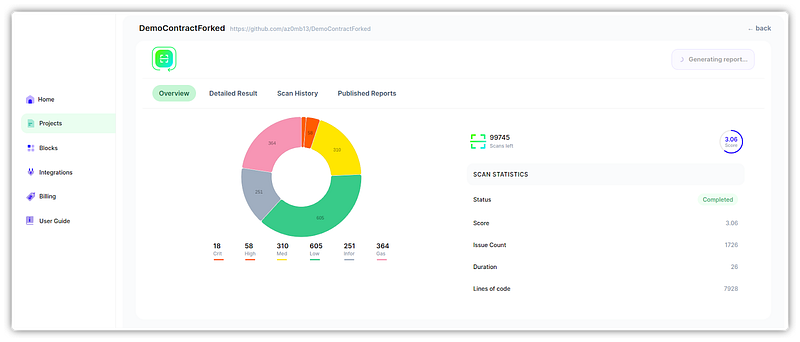
Conclusion:
SolidityScan is an advanced smart contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
SolidityScan — LinkedIn | Twitter | Telegram | Discord
