Unveiling the ERC-2771 Context and Multicall Vulnerability
Unveiling the ERC-2771 Context and Multicall Vulnerability
Introduction:
In the ever-evolving landscape of blockchain technology, security is paramount. On December 4th, 2023, OpenZeppelin was made aware of a crucial security disclosure from the Thirdweb team. They highlighted a potential vulnerability resulting from the integration of ERC-2771 and Multicall standards. This disclosure set in motion a rapid response from the OpenZeppelin team
Overview and Description:
The OpenZeppelin team conducted a thorough analysis and promptly confirmed that the identified issue wasn’t exclusive to their Contracts library implementations. Despite this, recognizing the potential widespread impact on the ecosystem. Their primary focus was to identify and mitigate potentially vulnerable contracts.
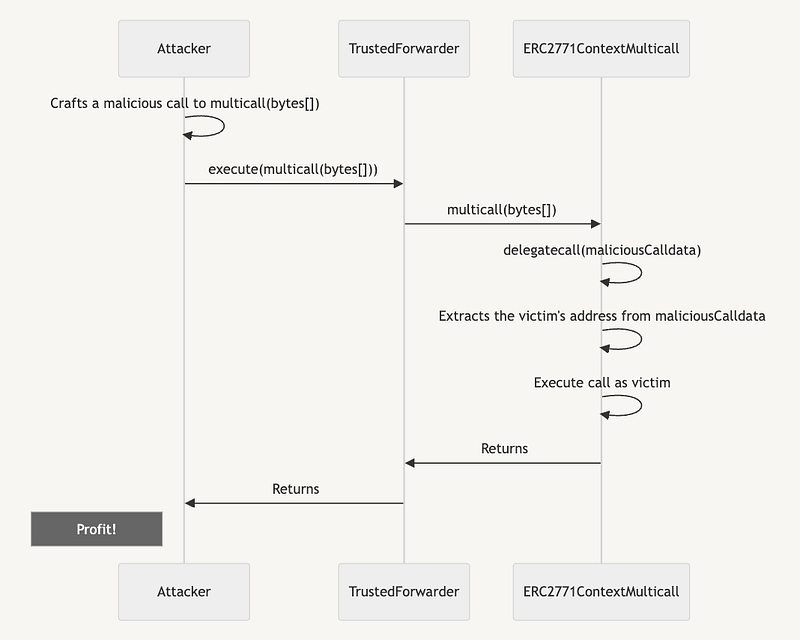
This issue stems from a problematic integration pattern affecting contracts implementing both Multicall and ERC-2771. This vulnerability allows attackers to engage in address spoofing by wrapping malicious calldata within forwarded requests. The attacker can then exploit Multicall’s delegatecall feature to manipulate the _msgSender() resolution in subcalls, posing a serious threat to the affected contracts.
The Attack in the Wild: Real-world Consequences
The severity of the situation became apparent as OpenZeppelin observed attacks in the wild. These attacks targeted various contracts, including Thirdweb users and forks, resulting in notable asset losses:
- 84.59 ETH Transaction Link
- 17,394 USDC Transaction Link
- 1.06 ETH Transaction Link
- 0.73 ETH Transaction Link
- 0.36 ETH Transaction Link
- 0.29 ETH Transaction Link
Understanding the Vulnerability:
- ERC-2771 is a standard for meta transactions, defining how the caller’s address should be resolved for calls relayed by a trusted forwarder. During such calls,
msg.senderis the forwarder’s address, with the actual caller only known to the forwarder. The standard details how this caller information is relayed to the contract being called. - A simple representation illustrates how an attacker can wrap multiple spoofed calls within a single multicall(bytes[]) to manipulate
_msgSender()resolution. - OpenZeppelin Defender’s Code Inspector detects vulnerable contracts by examining their imports and specific characteristics. Vulnerable contracts typically integrate ERC2771Context and Multicall, meet specific importing conditions, and involve the extraction of context details from trusted contracts.
Mitigation Steps:
The OpenZeppelin team provides comprehensive mitigation steps based on the instance details of affected contracts:
- Disable every trusted forwarder (if possible): Temporarily prevent gasless transactions to limit potential exploits.
- Pause your contract (if possible): While affecting users, pausing can reduce vulnerability, adding a temporary obstacle for attackers.
- Ask users to remove any approval to your contracts (if relevant): Guide users to tools like Revoke.cash to decrease attack profitability.
- Prepare an upgrade (if possible): Coordinate with the OpenZeppelin Upgrades plugin to patch vulnerabilities and ensure backward compatibility.
- Evaluate snapshot options: For contracts unable to upgrade, consider taking a snapshot of the contract state, planning a migration based on a “safe” block number.
Solution:
To address this challenge, OpenZeppelin released an update for both 4.x and 5.x versions of OpenZeppelin Contracts, enabling the use of Multicall alongside ERC2771Context. While acknowledging the integration challenges, the updates provide a safe and backward-compatible solution. The new Multicall version introduces a context suffix length for ERC2771Context data, enhancing identification and adaptation to every subcall originating from a trusted forwarder.
