The ShadowFI Hack Analysis

The ShadowFI Hack Analysis
On the 2nd of September, one of our clients informed us about the ShadowFI hack and gave us the transaction of the hack. Our team decoded the hack in 5 minutes and determined the root cause of the hack, and posted it on Twitter. This is a detailed analysis of the ShadowFI hack.
Decoding the Hack:
Below was the transaction by the malicious hacker.
https://bscscan.com/tx/0xe30dc75253eecec3377e03c532aa41bae1c26909bc8618f21fb83d4330a01018

The biggest hint was the 4th transaction, where a huge number of SDF tokens were sent to a zero address/ Null address. A null address or a zero address is a special address that is popularly used for burning tokens, as no one has control over the zero address. We can notice the millions of tokens at the null address.
https://bscscan.com/address/0x000000000000000000000000000000000000dead
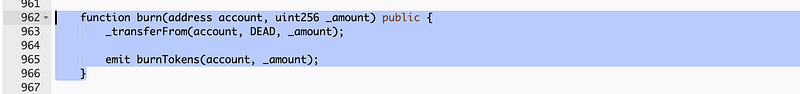
So, our first hint was that the hacker called the burn function. Meanwhile, we scanned the code on our product SolidityScan — A cloud-based smart contract security scanner and found that the burn function was public.
Now looking at other transactions made by the hacker, we figured out the hack was similar to the HospoWise hack.
1. The hacker bought a small amount of SDF tokens at the current price using WBNB
2. The hacker burns around 10 million SDF tokens calling the public burn function. This causes inflation and the value of SDF token sores.
3. Now the hacker sells his 9 SDF token for a crazy amount of 316,000$ in WBNB
Conclusion:
The hack happened because of improper access control on the burn function, as onlyOwner modifier was missing on the burn function. Our product, SoldityScan, can detect such vulnerabilities at a click of a button. Signup for a free trial at SolidityScan
