Temple DAO Hack Analysis
Temple DAO Hack Analysis
Overview
In yet another decentralized heist, Temple DAO, a DeFi protocol that offers yields on user deposits, was drained for $2.4 million due to a rather simple vulnerability — Lack of Access Controls. Let’s take a look at how it was exploited. Read our other blog post about Access Control.
The Exploit
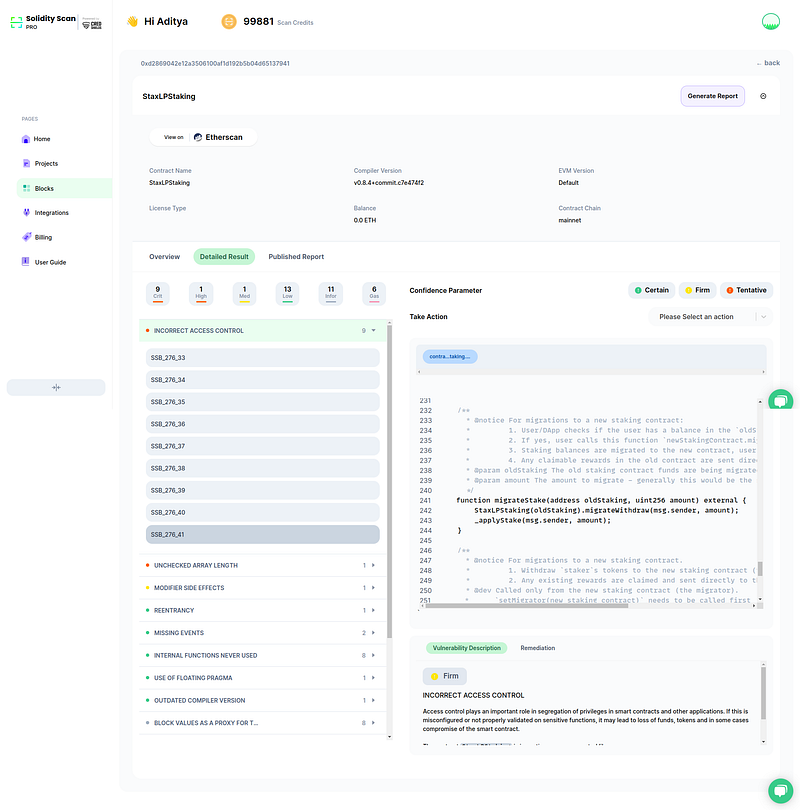
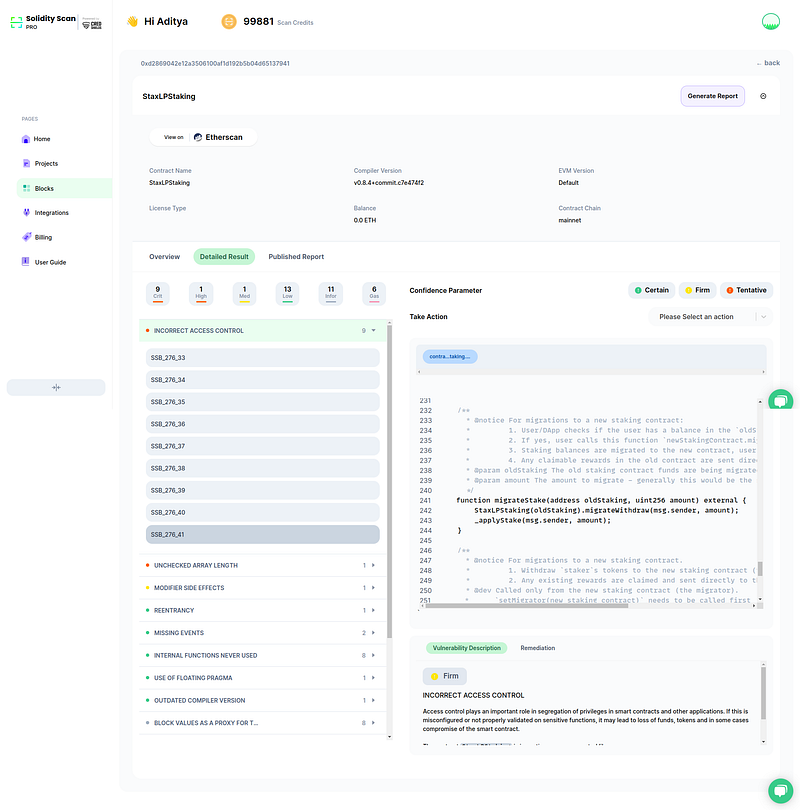
The Temple DAO’s STAX LP Staking contract’s code can be found on Etherscan at https://etherscan.io/address/0xd2869042e12a3506100af1d192b5b04d65137941#code#F1#L241.
The vulnerability lies on Line 241 in the function migrateStake()
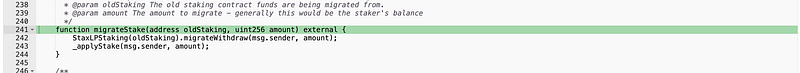
This function lacked access control validations and allowed anyone to call the function, not just the migrator contract.
It also lacked any validation on the oldStakingparameter.
Combining these two issues, it was possible for the attacker to create a malicious contract and use it as the first parameter for oldStaking and an arbitrary value for the amount, which was then withdrawn from the underlying vault and minted to the attacker.
The stolen tokens were then swapped for ETH in the attacker’s contract.
What did we learn?
Access controls and input validations still remain one of the simplest yet most impactful vulnerabilities in the smart contract ecosystem, where even the slightest mishap from the developers can cause millions in loss and damage to the company’s reputation.
Our tool SolidityScan detected this vulnerability upon scanning the vulnerable contract. SolidityScan allows developers and auditors to scan verified deployed contracts at a click of a button and find potential vulnerabilities in the contract. Signup for a free trial at https://solidityscan.com/signup