SushiSwap Hack Analysis — Improper Router Approve Parameters
SushiSwap Hack Analysis — Improper Router Approve Parameters
Overview:
On April 9, 2023, a flaw in sushi swap’s router processor smart contract was exploited, which lead to the loss of over $3.3M. The vulnerability did not validate the inputs given by the user and enabled an attacker to create a malicious router parameter that directed users to an attacker-controlled pool.
Smart Contract Hack Overview:
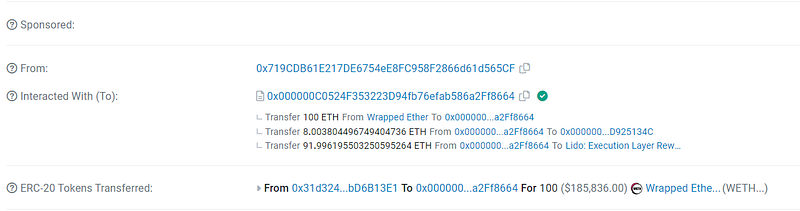
- Attacker’s address: 0x719
- Attacker’s transaction: 0xea3
- RouteProcessor2 Vulnerable Contract: 0x044b
- Attacker’s Contract: 0x000000c05
- Revoke approval for below address:
- ETH: 0x044b75f554b886A065b9567891e45c79542d7357
- polygon: 0x5097cbb61d3c75907656dc4e3bba892ff136649a
- arbitrum nova:0x1c5771e96C9d5524fb6e606f5B356d08C40Eb194
- arbitrum:0xA7caC4207579A179c1069435d032ee0F9F150e5c
- bsc:0xD75F5369724b513b497101fb15211160c1d96550
- avax:0xbACEB8eC6b9355Dfc0269C18bac9d6E2Bdc29C4F
- boba:0x2f686751b19a9d91cc3d57d90150bc767f050066
- fantom:0x3e603C14aF37EBdaD31709C4f848Fc6aD5BEc715
- fuse:0x2f686751b19a9d91cc3d57d90150Bc767f050066
- gnosis:0x145d82bCa93cCa2AE057D1c6f26245d1b9522E6F
- moonbeam:0x1838b053E0223F05FB768fa79aA07Df3f0f27480
- moonriver: 0x3d2f8ae0344d38525d2ae96ab750b83480c0844f
- optimism: 0xF0cBce1942A68BEB3d1b73F0dd86C8DCc363eF49
- polygon zkevm: 0x93395129bd3fcf49d95730D3C2737c17990fF328
Decoding the Smart Contract Vulnerability:
- The attack began when the vulnerable contract’s processRoute() method was invoked and a long argument was given by the attacker, causing the router to read the attacker-created contract.
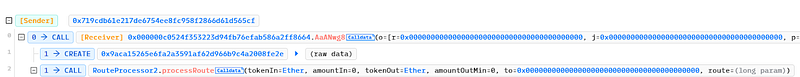
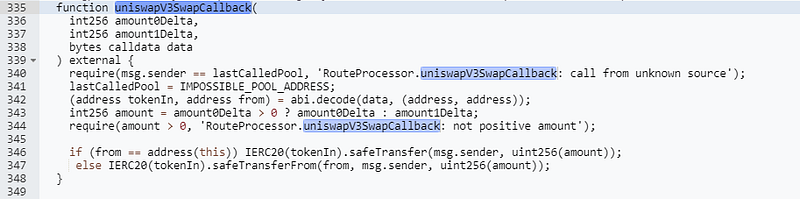
- The uniswapV3SwapCallBack() method was called by the vulnerable contract’s internal swap() function to send tokens from the source account to the recipient’s address.
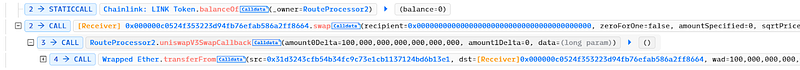
- Since there were no legal checks or pool verifications performed before passing the user-provided pool parameter to the swap. It gave an attacker the ability to run the swap function and set their pool address as the LastCallPool variable address.
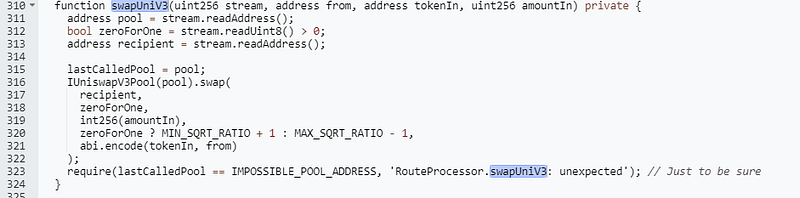
- The attacker stole the tokens of other users who had previously accepted the Routerprocessor2 contract by using the fraudulent pool’s uniswapV3SwapCallback function in its swap function to bypass the msg.sender check.
- Major chains that had previously authorized the RouterProcessor2 contract were impacted by the hack, which caused a loss of $3.3M.
Mitigation and Best Practices:
- It’s recommended to validate all users’ input and use modifiers on critical functionalities that may affect the bool balances and users’ funds.
- Access control must be properly implemented, and only the owner of that contract should be allowed to perform critical transactions and required conditions should not be able to be bypassed by any form of privilege escalations.
If you liked our blog. Do check out our product SolidityScan!
SolidityScan is an advanced smart-contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
SolidityScan — LinkedIn | Twitter | Telegram | Discord
