Sturdy Finance Hack Analysis
Sturdy Finance Hack Analysis
Overview
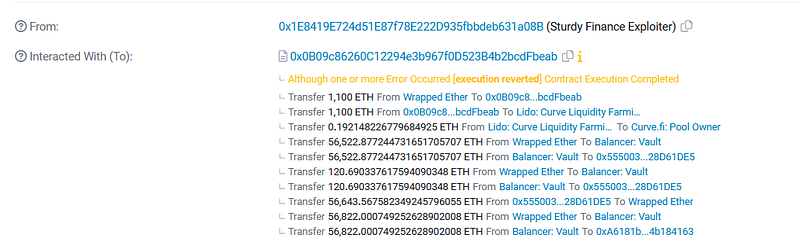
On June 12, 2023, Sturdy Finance suffered an attack, due to a read-only reentrancy vulnerability leading to a loss of ~800K USD.
Smart Contract Hack Overview:
Decoding the Smart Contract Vulnerability:
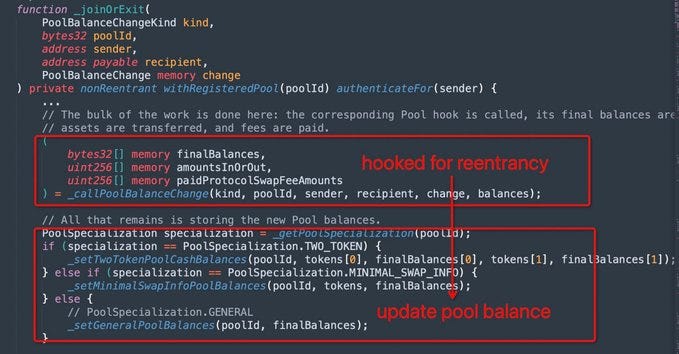
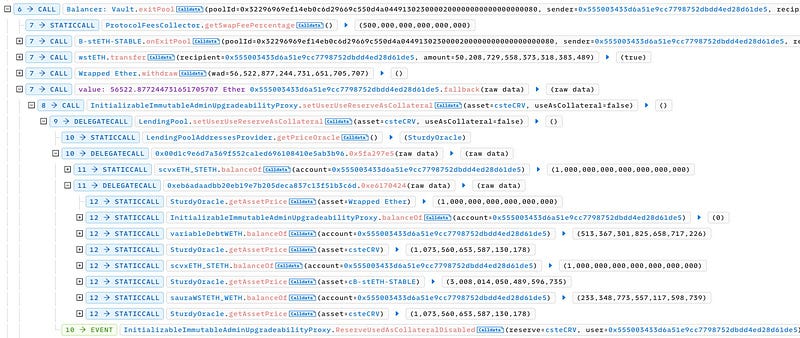
- The root cause behind this incident was the exploitation of Balancer’s read-only reentrancy vulnerability, which occurred during the manipulation of the B-stETH-STABLE price.
- The attacker borrowed 50,000 WstETH and 60,000 WETH from Aave as a flashloan.
- They added 1,100 ETH to the steCRV pool to mint 1,023 steCRV.
- The attacker added 50,000 wstETH and 57,000 WETH to the Balancer B-stETH-STABLE pool to mint 109.4,517 B-stETH-STABLE.
- They deposited 1,000 steCRV and 233 B-stETH-STABLE as collateral into Sturdy.
- Then, they borrowed 513 WETH from Sturdy.
- The attacker manipulated the price of B-stETH-STABLE and set steCRV as non-collateral during the manipulation. As the price of B-stETH-STABLE increased threefold, the protocol considered the attacker’s 233 collateralised B-stETH-STABLE enough to cover the 513 WETH debt. Consequently, the attacker’s steRV could no longer be used as collateral.
- They withdrew 1,000 steCRV from Sturdy.
- As the price of B-stETH-STABLE returned to normal, the attacker liquidated their position with 236 WETH to reclaim 233 B-stETH-STABLE (worth approximately 106 wstETH + 120 WETH).
- Note that steps 3–8 listed above were repeatedly executed with 5 different contracts.
- Finally, the attacker repaid the flashloan and finalized their profit.
Mitigation and Best Practices:
- Use reentrancy-preventive function modifiers, such as Open Zepplin’s Re-entrancy guard
- Always make sure that any state changes occur internally first, such as updating balances or calling internal functions before calling external code.
- Use the check-effect pattern for interaction, Checks highlight the veracity of the circumstances. Effects highlight the state changes that result from interactions. The transactions carried out between contracts or functions are referred to as interactions.
- To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Schedule a call at https://credshields.com/
- Scan your Solidity contracts against the latest common security vulnerabilities with 130+ detections at SolidityScan

Conclusion:
SolidityScan is an advanced smart-contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
SolidityScan — LinkedIn | Twitter | Telegram | Discord
