StepHeroNFTs Hack Analysis
StepHeroNFTs Hack Analysis
Overview:
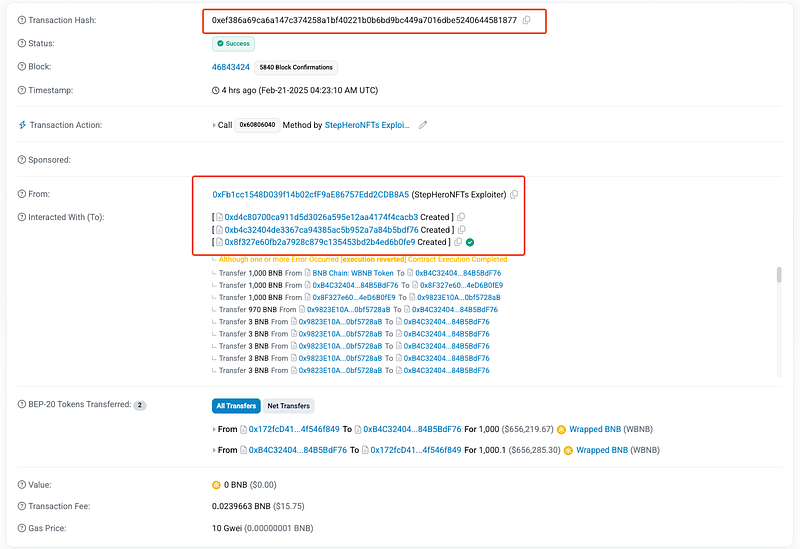
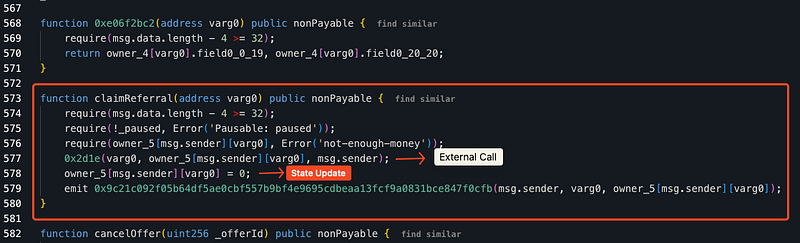
On February 21, 2025, the StepHeroNFTs (@StepHeroNFTs)- an inactive NFT project on BSC Chain– was attacked, resulting in the loss of assets due to a reentrancy vulnerability in the claimReferral function. The attacker exploited recursive calls to drain the contract before state updates were finalized. This attack resulted in a total loss of approximately ~$90,000.
Smart Contract Hack Overview:
Decoding the Smart Contract Vulnerability:
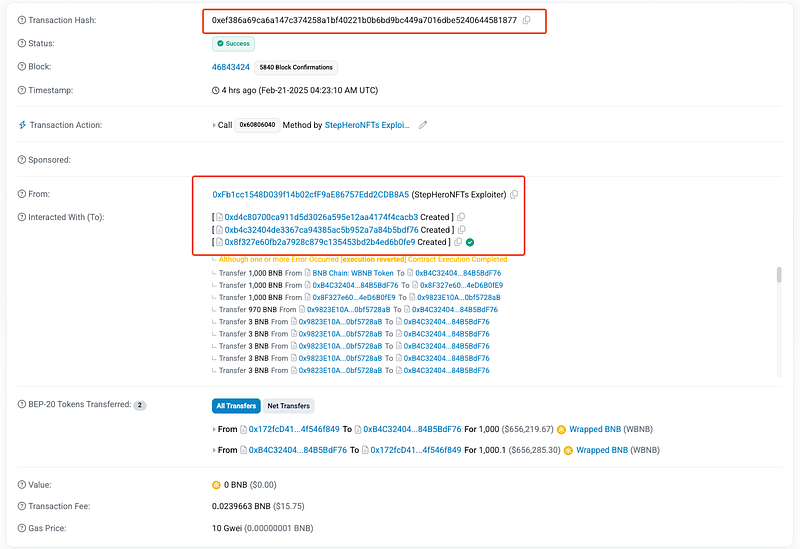
- The root cause of the exploit was an unchecked reentrancy vulnerability in the
claimReferralfunction, which transferred assets before updating the referral balance. - The victim contract is unverified, and its source code is not public; however, by decompiling the contract, we can extract and analyze the vulnerable
claimReferralfunction responsible for the exploit.
- The attacker bought NFTs using their own referral code, inflating
owner_5[msg.sender][varg0]. - This function (
0x2d1e) represents an external call, likely transferring assets. - Since the balance was only updated after the transfer, the attacker repeatedly withdrew funds before the contract recognized the depletion.
- Attacker’s malicious contract recursively called
claimReferral(), allowing the attacker to drain the contract in a single transaction.

Mitigation and Best Practices:
- Use the Checks-Effects-Interactions Pattern which ensures that the contract states are updated before executing external calls to prevent reentrancy.
- Implement
nonReentrantmodifiers to prevent recursive function calls within the same transaction. - Also, utilize OpenZeppelin’s
ReentrancyGuardto block recursive calls within the same transaction. - To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Our public audit reports can be found on https://github.com/Credshields/audit-reports. Schedule a call at https://credshields.com/
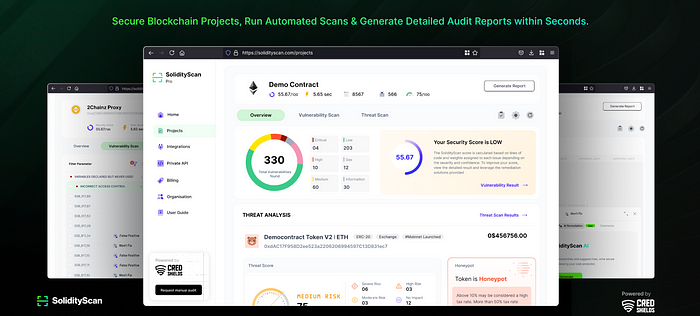
- Scan your Solidity contracts against the latest common security vulnerabilities with 494+ detections at SolidityScan.
Conclusion:
SolidityScan is an advanced smart contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
