StarsArena Hack Analysis
StarsArena Hack Analysis
Overview:
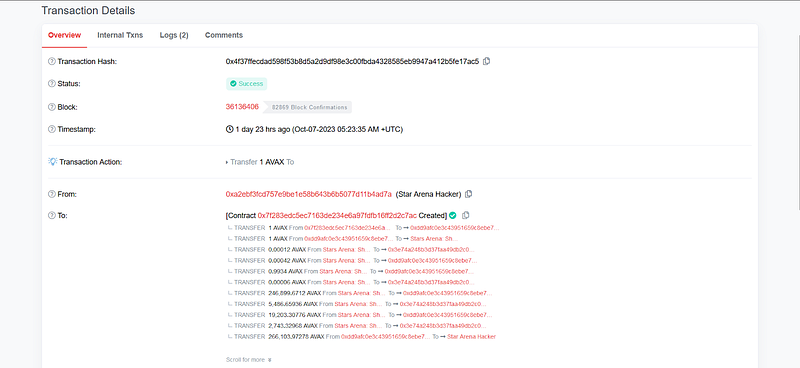
On October 7, 2023, StarsArena suffered a hack due to a Re-entrancy vulnerability, leading to an approximate loss of ~3M USD.
Smart Contract Hack Overview:
- Attacker address: 0xa2ebf3
- Attack Contract: 0x7f283e
- Vulnerable Contract: 0xa481b1
- Attack Transaction: 0x4f37ff
Decoding the Smart Contract Vulnerability:
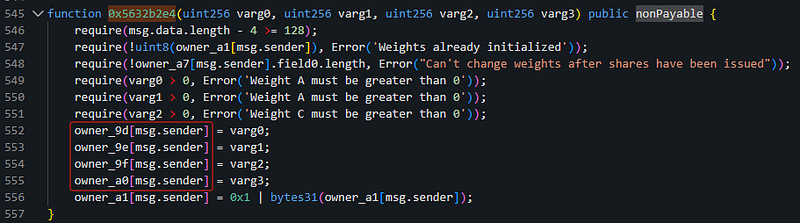
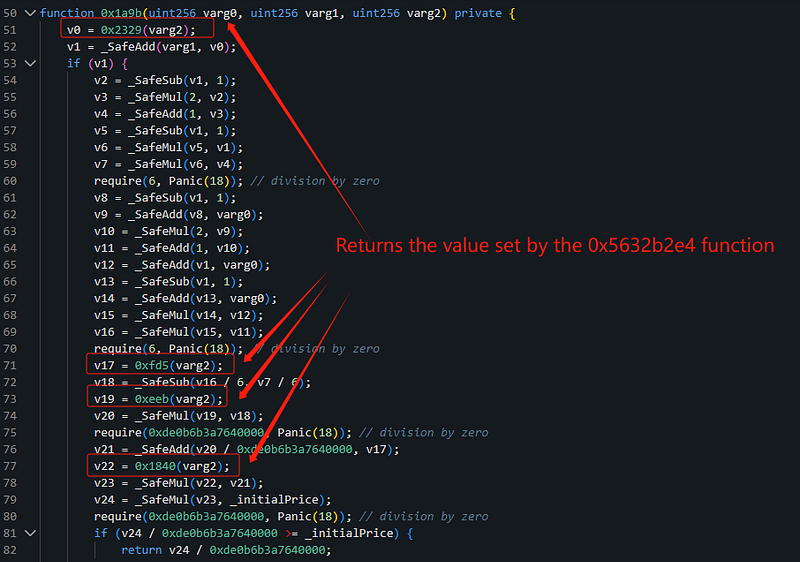
- The attacker performed a reentrancy attack during the 0xe9ccf3a3 function execution.
- Within this attack, they made a call to the 0x5632b2e4 function and set a block height.
- In the “sellShares” function, the attacker used this block height as a parameter for a calculation, resulting in an abnormally large amount of $AVAX.
- As a consequence of their actions, the attacker managed to gain a substantial profit.
Mitigation and Best Practices:
- Use reentrancy-preventive function modifiers, such as Open Zepplin’s Re-entrancy guard.
- Always make sure that any state changes occur internally first, such as updating balances or calling internal functions before calling external code.
- To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Schedule a call at https://credshields.com/
- Scan your Solidity contracts against the latest common security vulnerabilities with 130+ detections at SolidityScan including reentrancy vulnerabilities.
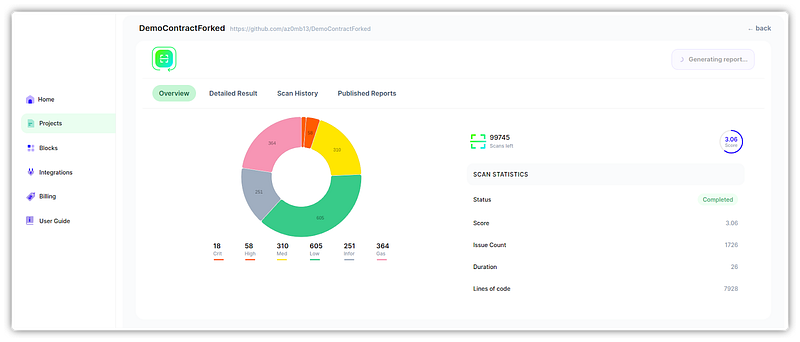
Conclusion:
SolidityScan is an advanced smart contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
SolidityScan — LinkedIn | Twitter | Telegram | Discord
