Spearx USDs Stablecoin Hack — Rebasing Discrepancy Bug
Spearx USDs Stablecoin Hack — Rebasing Discrepancy Bug
Description:
On February 4, 2023, a stablecoin attack on Spearx’s unpublished updated code resulted in the protocol losing $300,000 as a result of an internal account balance accounting error that happened when the account was switched from non-rebasing to rebasing-based accounting.
Smart Contract Hack Overview:
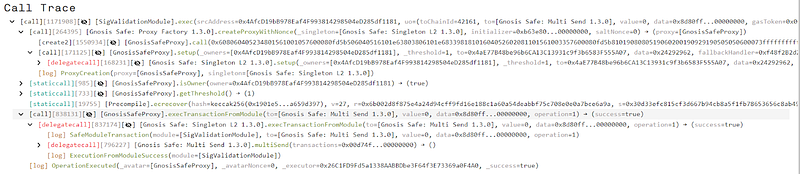
- Spearx USDs contract: 0xd74f525
- Attacker’s transaction: 0xe74641b4b7,0xfaf84cab
- Attacker’s address: 0x4afcd19
- Attacker’s Multi-Sig Contract: 0x5c978df5
- Attacker’s pre-compute address: 0xfeedb6f
- Rebasing/Non-Rebasing binary contract code: https://arbiscan.io/bytecode-decompiler?a=0x97a7e6cf949114fe4711018485d757b9c4962307

Decoding the smart contract vulnerability:
- The code was upgraded internally and the method “_ensureRebasingMigration()” conducted internal accounting balances and functioned as a safeguard for rebasing/non-rebasing accounts.
- The method failed to handle the situation in which a smart contract account that was a rebasing holder account and had not been configured by the admin would immediately become a non-rebasing account if the USDs token were interacted with in any way (transfer, burn, mint)
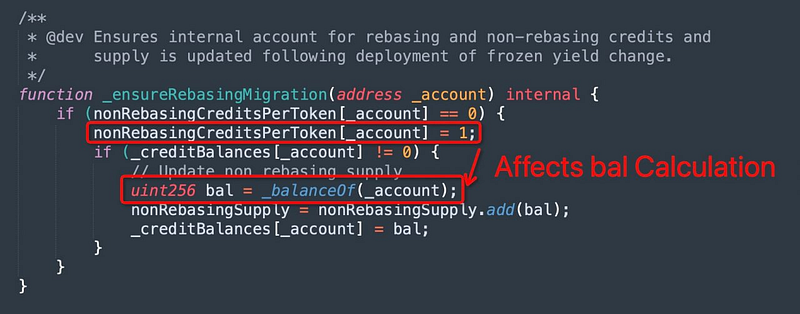
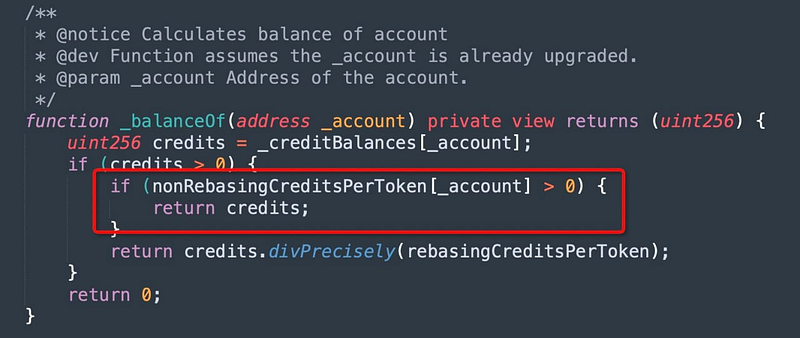
- The function fails to handle the case when a smart contract already possessed a USDs token. Due to this “nonRebaseCreditsPerToken” was changed to 1 and “_balanceOf( account)” returned credits rather than
credits / creditPerToken.
- In order to take advantage of the abovementioned situation, the attacker transferred 11 USDS to initiate
_ensureRebasingMigration(), which caused_balanceOf( account)to return credits rather than credits / creditPerToken. The address’s balance increased to 9.7 billion.
Mitigation and Best Practices:
- The code was internally improved, but it wasn’t made public. This goes against the secure design principles and makes it harder to protect users’ funds from being stolen because the code wasn’t audited and deployed to production, which is what should have happened.
- According to the most recent public code, the balance computation was incorrect since the events were not thrown correctly.
- It is advised against upgrading the contract internally, and if modifications are made, please have them verified by security auditors before deploying them.
- To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Schedule a call at https://credshields.com/
- Scan your Solidity contracts against the latest common security vulnerabilities with 130+ detection at SolidityScan

Conclusion:
SolidityScan is an advanced smart-contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
SolidityScan — LinkedIn | Twitter | Telegram | Discord
