Sovryn Finance Hack Analysis

Sovryn Finance Hack Analysis
Overview:
On October 4, 2022, a hacker exploited a serious flaw in the platform’s Legacy Sovryn loan and borrowing pool to steal almost $1.1 million from the Bitcoin-focused decentralized finance (Defi) trading and lending protocol Sovryn.
Due to the multi-layered security approach, Sovryn lost money from two legacy lending pools through a flash loan attack. The developers noticed the unusual interactions with the protocol and immediately alerted the security team. The team then immediately protected half of their funds by pausing the protocol until the analysis was finished and the stolen money was recovered.
Smart Contract Hack Overview:
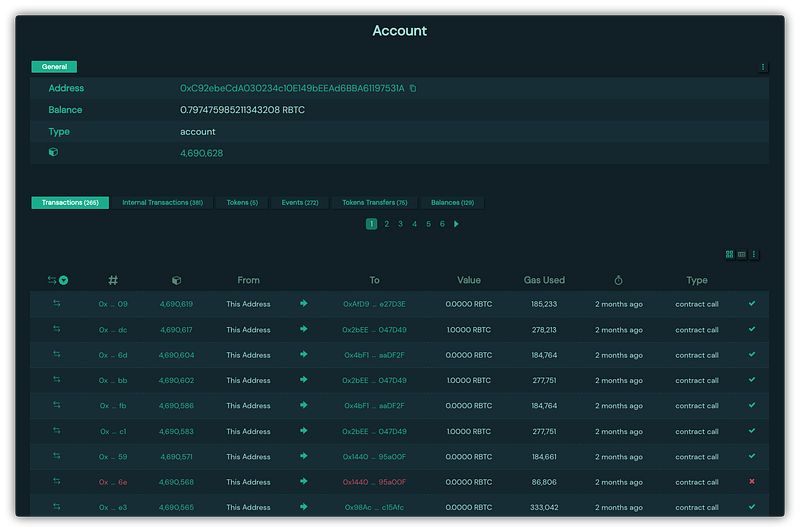
Attacker’s Transaction: 0xc92e
Decoding the Smart Contract Vulnerability
- The hacker acquired WRBTC (Wrapped RBTC) from RskSwap via a flash swap before borrowing more WRBTC from the protocol’s loan contract using its own stablecoin token, XUSD, as collateral.
- The attacker then contributed liquidity to the RBTC lending contract, completed their loan with a swap using their XUSD collateral, redeemed (burned) their iRBTC token, and returned the WRBTC to RskSwap to finish the flash swap.
- Through the procedure, the exploiter deflated iToken’s price, allowing them to extract more RBTC than they had previously invested.
Here’s How the attack works:
- The attacker first deployed the contract and transferred 0.03 RBTC.
- They then use the attack contract to flashloan 8.20 RBTC to three pairs of addresses before depositing the remaining 8.23 RBTC. The attacker borrows 52,999 side tokens using the LP.
- Finally, the closeWithDeposit method is called to refund the collateral.
- 26.900 side tokens were exchanged for 4.17 RBTCs. The attacker, on the other hand, minted 26,000 side tokens into 22,653 load tokens, but the closeWithDeposit method does not have a mint function.
- The attacker then utilized the side tokens externally call attackers contract and then used the attack contract to run the mint function.
- The Load token price is calculated by the
tokenPricefunction depending on the number of side tokens. The total number of tokens has not been updated, resulting in the attacker acquiring more Load tokens. - Using the burn function, the attacker then burns ens to get 27,086.
- The attacker then runs through the relevant method to acquire the side token, which is converted to RBTC.
- The perpetrators then used Tornado cash to launder the stolen cash.
Mitigation best practices:
- Price manipulation attempts can be mitigated to a larger extent via oracles such as Chain Links and input validation on those feed parameters to prevent stale data
- To prevent such assaults, the best Smart Contract auditors must examine Defi apps. We at CredShields provide not only Smart Contract security but also provide end-to-end security of web applications and externally exposed networks. Schedule a call at https://credshields.com/
- Sudden fluctuations in token prices must be confirmed on a regular basis, and gaming audits must be performed.
- Examine the visibility of functions to ensure that any functions that may be defined as external are marked external and not public to save the gas fees.
- Document the system’s access control roles with proper permissions to prevent loss of funds.
- Scan your contract against the latest common security vulnerabilities with 130+ patterns at SolidityScan, which includes the detection of Re-entrancy vulnerabilities.

Conclusion:
SolidityScan is an advanced smart-contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
