Sentiment Hack Analysis — Reentrancy Attack
Sentiment Hack Analysis — Reentrancy Attack
Overview:
On April 4, 2023, the Sentiment was reported to have experienced a read-only reentrancy attack, resulting in price manipulation on the protocol and a total loss of $1M.
Smart Contract Hack Overview:
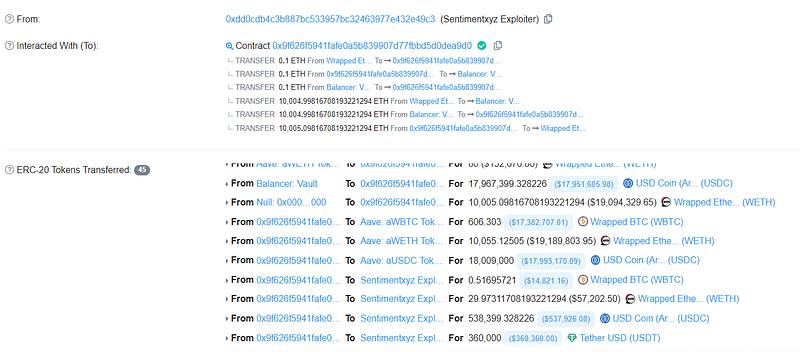
- Attacker’s transaction: 0xa9ff2b
- 0x62c5 proxy contract: 0x62c5
- Attackers address:0xdd0cdb
- Lending Pool: 0x270,0x794
- Balancer vault: 0xba12
- Vulnerable code:#L108
Decoding The Smart Contract Vulnerability:
- The attacker began the attack with a flashloan of 10,050 ETH from the sentiments lending pool some WBTC and USDC.

- The attacker then manipulated the LP pool balance by using
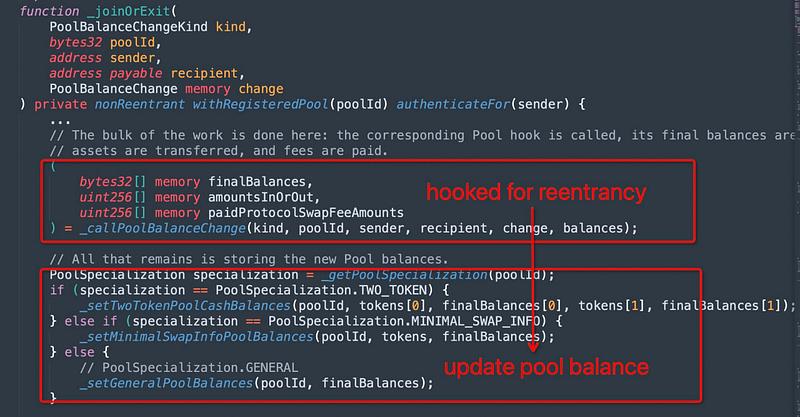
joinPool()first to join the pool, and the balance was updated with a new balance when the attacker moved liquidity in the pool.
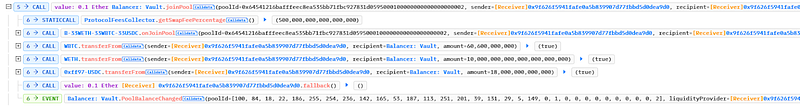
- The attacker then used the
exitPool()function to withdraw the money, and the balance vault contract delivered eth to the attacker’s contract, which used thefallback()mechanism to remove the funds.
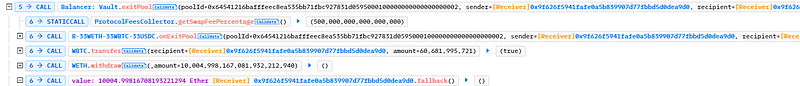
- In the fallback function, the attacker invoked the proxy contract’s borrow function, which computed a price based on the Balancer Vault return data. getPoolTokens().
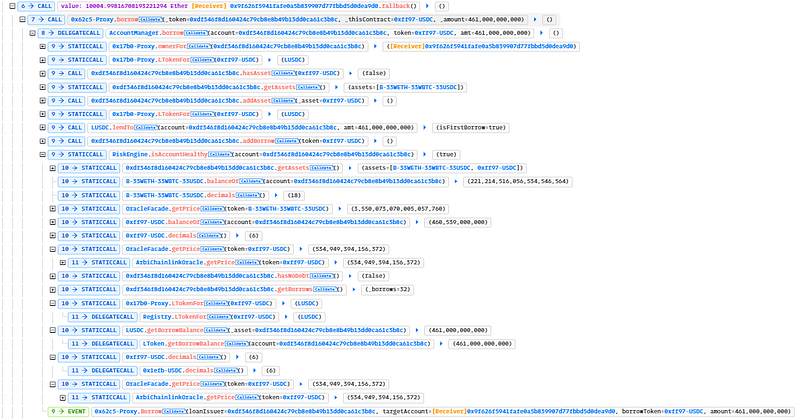
- As soon as the attacker executed exitPool(), the attacker re-entered, and the overall supply of the pool was lowered since the attacker withdrew all of the deposited LP tokens between the exit transaction and its successful completion.
- The attacker subsequently moved all of the ETH to their wallet, resulting in a total loss of $1 million.
Mitigation and Best Practices:
- The attack could have been prevented if the sentiment protocol would have stayed up to date with the latest hack as the balancer was compromised with the same attack a month and changes should have been done to the sentiments architecture and code accordingly.
- Use reentrancy-preventive function modifications, such as Open Zepplin’s Re-entrancy guard
- Always make sure that any state changes occur internally first, such as updating balances or calling internal functions before calling external code.
- Use the check-effect pattern for interaction, Checks highlight the veracity of the circumstances. Effects highlight the state changes that result from interactions. The transactions carried out between contracts or functions are referred to as interactions.
- To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Schedule a call at https://credshields.com/
- Scan your Solidity contracts against the latest common security vulnerabilities with 130+ detection at SolidityScan including access control vulnerabilities.

Conclusion:
SolidityScan is an advanced smart-contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
SolidityScan — LinkedIn | Twitter | Telegram | Discord
