Rubic Exchange Hack Analysis — Whitelisting does not always work effectively
Rubic Exchange Hack Analysis — Whitelisting does not always work effectively
Overview:
On December 25th, 2022, an exploit on Rubic Exchange resulted in the loss of more than $1.4 million in customer funds. The Rubic protocol improperly added USDC tokens to the Router whitelist, which resulted in the theft of USDC tokens from RubicProxy contract users.
Smart Contract Hack Overview:
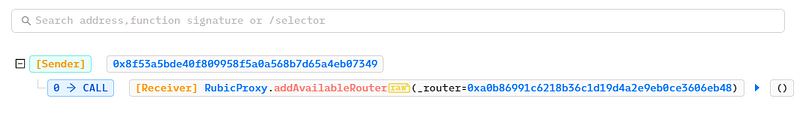
- Attackers transaction: 0x9a97d8, 0x6551b9
- Attackers address: 0x001B91c7
- Attackers contract: 0x253dD8
- RubicProxy contract: 0x3335a8
- USDC misconfiguration exploit transaction: 0x30679e7

Decoding the smart contract vulnerability:
- The user-supplied target Router value sent in the
calldatais first checked by Rubic’s contract to identify if it is on the protocol’s whitelist. - The user-supplied
calldatawill be provided to the target Router when the whitelist check is successful.
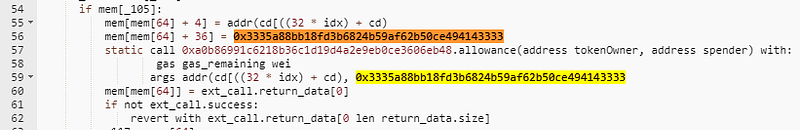
- However, because
routerCallNative()lacked validity checks and the protocol added USDC tokens to its router whitelist, it allowed random users to call the RubicProxy Contract directly.
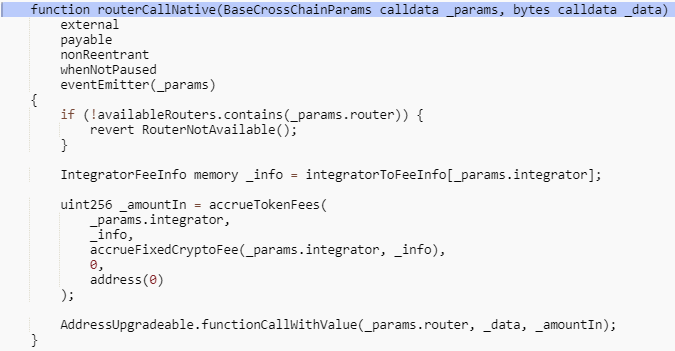
- Thus, the attacker used the routerCallNative() function to call the USDC contract and transferred the USDC tokens from the users’ accounts who had previously approved the RubicProxy contract to their address.
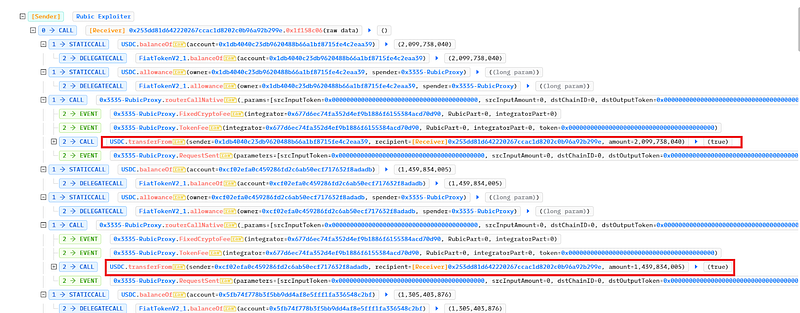
- The attacker subsequently transferred the stolen to Tornado Cash worth 1,100 ETH.
- Due to the fact that Rubic is a cross-chain DEX aggregator, users of their platform can exchange tokens by calling a function in the RubicProxy contract. The router contract permitted arbitrary calls to whitelisted locations, and the hacker was able to siphon off all payments from customers who had accepted the RubicProxy since the routerCallNative method lacked validation.
Mitigation and best practices:
- Calldata needs to be thoroughly examined for access control validations. Read about our blog post on Access Control in Smart Contracts.
- If whitelisting is included in the contract, it should undergo a comprehensive audit, and smart contracts should forbid whitelisting for crucial operations accountable for transferring users’ funds.
- To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide not only Smart Contract security but also provide end-to-end security of web applications and externally exposed networks. Schedule a call at https://credshields.com/
- Scan your contract against the latest common security vulnerabilities with 130+ patterns at SolidityScan, which includes the detection of Re-entrancy vulnerabilities.

Conclusion:
SolidityScan is an advanced smart-contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security related updates.
SolidityScan — LinkedIn | Twitter | Telegram | Discord
