Ronin Hack Analysis
Ronin Hack Analysis
Overview:
On March 29, Ronin officially reported that the Ronin Bridge had been hacked due to a private key theft. The hackers took 173,600 ETH and 25.5 million USDC, which at the time amounted to almost $625 million.
Smart contract hack overview:
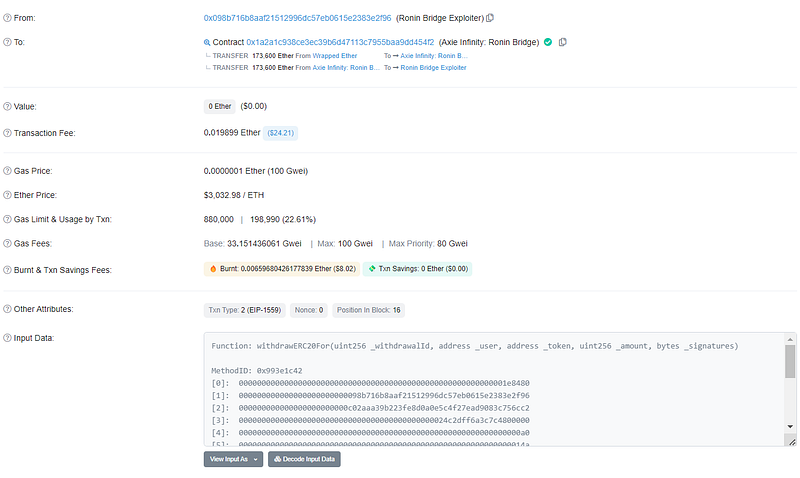
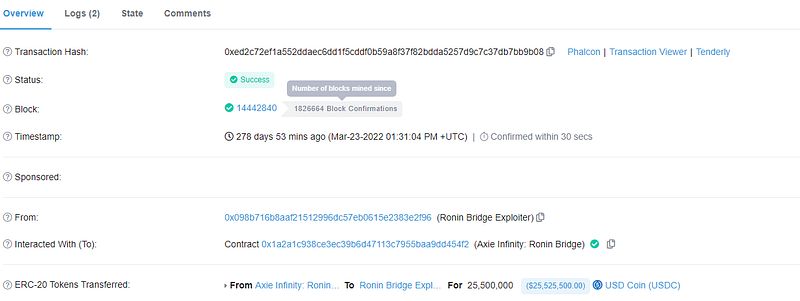
- Attacker’s address: 0x098B71
- Attacker first transaction: 0xc28fad
- Attacker’s second transaction: 0xed2c7
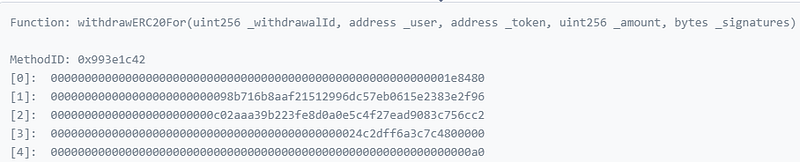
- The 5 signature accounts here are as follows:
0x11360
0x1a15a
0x70bb
0xb9e5
0xf224
Decoding the smart contract vulnerability
- In November of last year, the company requested Axie DAO’s assistance to distribute free transactions on its network, which permitted listed Sky Mavis to sign a plethora of transactions caused due to a heavy user load.
- The system was abandoned in December, but the authorizations that made it possible were never taken away.
- Five Sky Mavis nodes were responsible for the authority of the Axie DAO and were used to validate the transaction before they were compromised by the attacker. They then obtained the signature from the Axie DAO validator using the gas-free RPC.
- A deposit or withdrawal needed permissions by a majority of five of the nine validator nodes utilized by the Ronin Network to validate transactions on the bridge.
- The attacker successfully overruled all transaction security once five out of the nine validator nodes were hacked, allowing them to withdraw any amount of money they wished from withdrawERC20For ()
- Sky Mavis neglected important security best practices, including the need for monitoring and the significance of least privilege in favor of the Ronin Network’s performance above its security which led to the largest hack in Defi history.
Mitigation and best practices:
- The system needs to be totally decentralized, and transactions and DAO operations shouldn’t be overseen or approved by a group of centralized parties.
- Excessive permissions should never allow for exploitation and should always be carefully evaluated before being withdrawn after the goal is met.
- The DAO should constantly watch for malicious transactions and stop users who are attempting to take advantage of other funds.
- The strongest encryption should be used to keep the private keys, which shouldn’t be done on a centralized server.
- If necessary, utilize multi-sig wallets with 8–10 validators.
- To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShieldsprovide not only Smart Contract security but also provide end-to-end security of web applications and externally exposed networks. Schedule a call at https://credshields.com/
- Scan your contract against the latest common security vulnerabilities with 130+ patterns at SolidityScan, which includes the detection of Re-entrancy vulnerabilities.

Conclusion:
SolidityScan is an advanced smart-contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
