Roast Football Hack Analysis
Roast Football Hack Analysis
Overview:
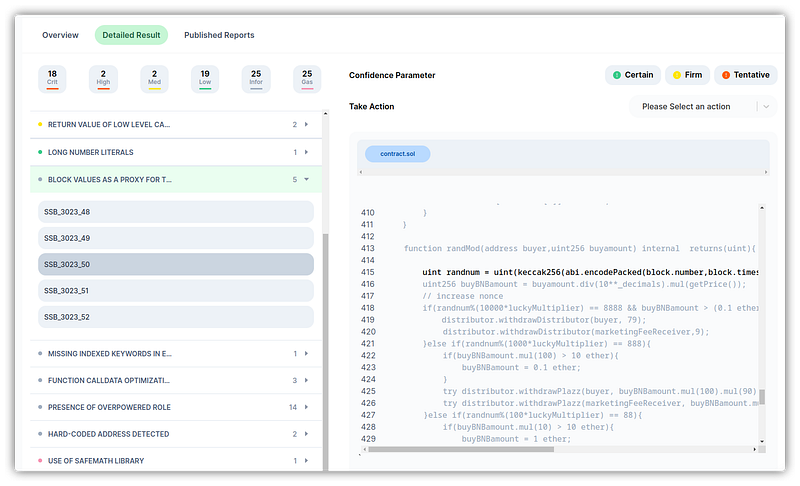
The Roast Football Protocol was hacked on December 5, 2022. The attacker took advantage of a vulnerability in the lottery function’s pseudorandom number generation to buy transactions only when there was a significantly higher probability of winning the lottery. In fifty trials, the intruder was successful twice, earning 12 BNB. This vulnerability could have been found if SolidityScan had been used to scan the contract.
Smart contract hack overview:
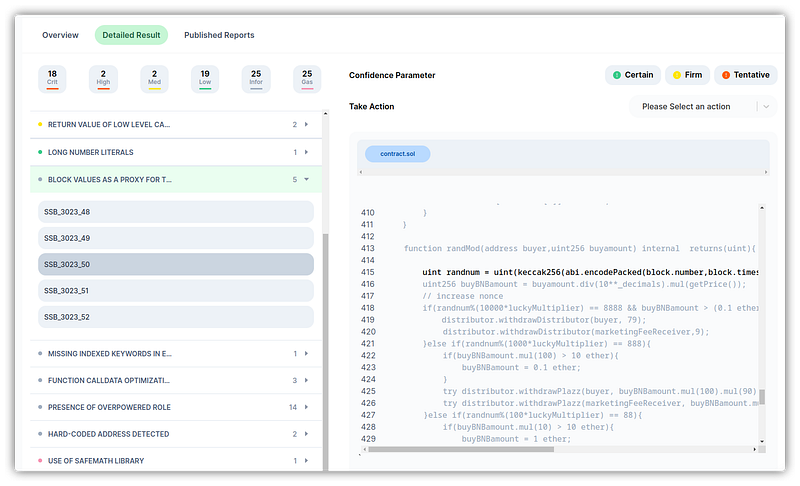
- Attacker’s address: 0x5f7db41e
- Attacker’s transactions: 0xcc8fdb3
- RFB contract’s code: 0x26f14
- Vulnerable function: #L417
Decoding the smart contract vulnerability:
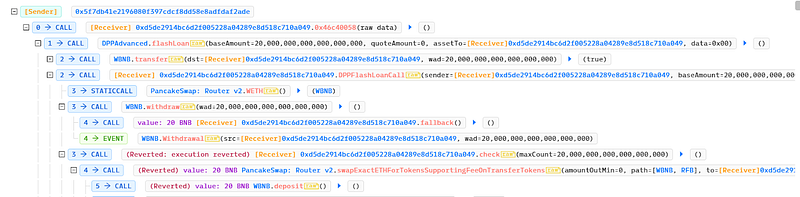
- The lottery’s random number generator used the
randModfunction. - It accepted the “buyer” address and the “buyAmount” as parameters and returned an integer token that was created at random.
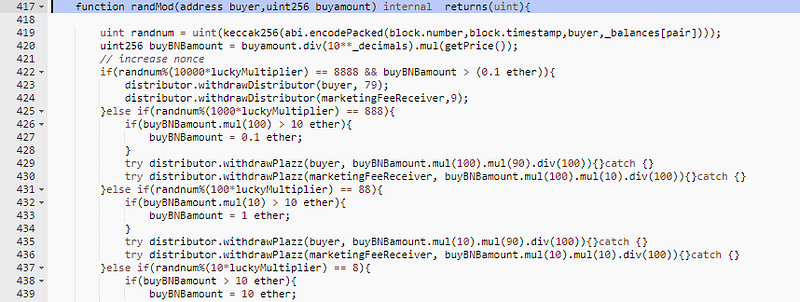
- When customers bought the RFB, they had a chance to win a ten times reward through a lottery system.
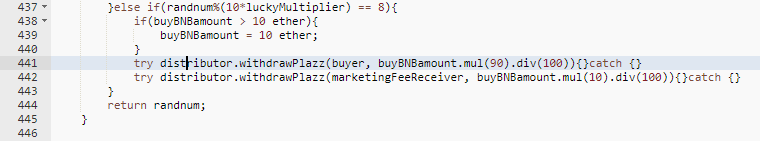
- The logic for random number generation can be seen in the following code:
uint randnum = uint(keccak256(abi.encodePacked(block.number,block.timestamp,buyer,_balances[pair])));
- The generator is taking input as
block.number,block.timestamp, buyer address, and the balance. All of which can be obtained by the attacker when they call the function. This makes it possible to guess or enumerate the random numbers used inside therandMod()function. - The attacker only bought the RFB tokens when they were sure of their winning probability.
- If they lost, the function reverted, costing the attacker only the gas amount.
Mitigation and Best Practices:
- Block variables shouldn’t be used to source entropy (general terms; there are few exceptions), as they may be altered by miners, obtained by attackers and external users, and the contract shouldn’t be biased and should be the same for everyone.
- The payoff for mining a block should be less than the expected value of the random trial for every bet in a single block.
- Examine suspect addresses for instances of fraudulent transactions and remove them from the pool.
- Refer to our blog —https://blog.solidityscan.com/weak-block-based-prng-in-solidity-f29e089de594
- To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide not only Smart Contract security but also provide end-to-end security of web applications and externally exposed networks. Schedule a call at https://credshields.com/
- Scan your contract against the latest common security vulnerabilities with 130+ patterns at SolidityScan, which includes the detection of Re-entrancy vulnerabilities.
Conclusion:
SolidityScan is an advanced smart-contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
