Polter Finance Hack Analysis

Polter Finance Hack Analysis

Overview:
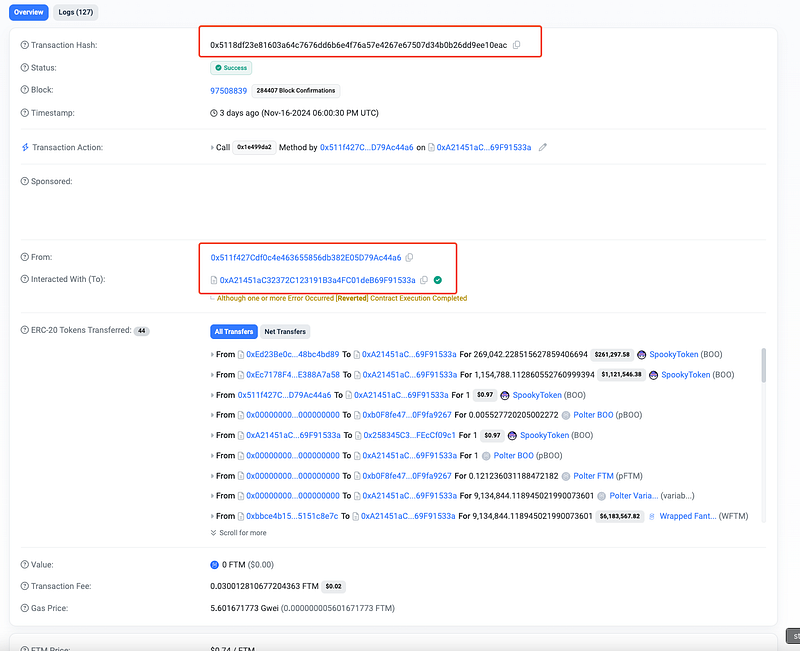
On November 16th, 2024, Polter Finance (@polterfinance), a DeFi lending protocol on the Fantom network, suffered a devastating exploit that resulted in the loss of approximately $8.7 million. The exploit was caused by a price manipulation vulnerability in its oracle system, specifically in the ChainlinkUniV2Adapter contract, which miscalculated the price of the BOO token due to spot price reliance. This enabled the attacker to artificially inflate the value of collateral and drain multiple lending pools.
Polter Finance responded by pausing the platform, notifying bridges, and reaching out to authorities to investigate and recover funds.
Smart Contract Hack Overview:
- Attack Transaction: 0x5118d
- Attacker’s Address:
0x511f4 - Attacker’s Exploit Contract Address:
0xA2145
Decoding the Smart Contract Vulnerability:
- The root cause of the exploit lies in the incorrect price validation logic within the AaveOracle contract, which Polter Finance relied on. Specifically, the ChainlinkUniV2Adapter contract used for price fetching contained a flaw in its price validation mechanism.
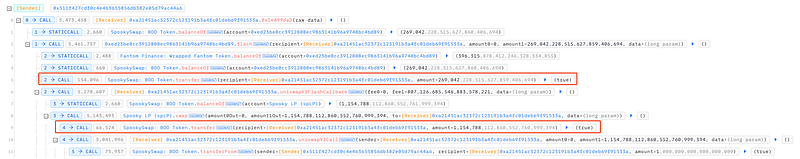
- The attacker initiated a flash loan of 269,042 BOO and 1,154,788 BOO tokens from Spooky V2 and Spooky V3 LPs, respectively. This left a minimal amount of BOO tokens on each liquidity pair, causing a drastic price imbalance.

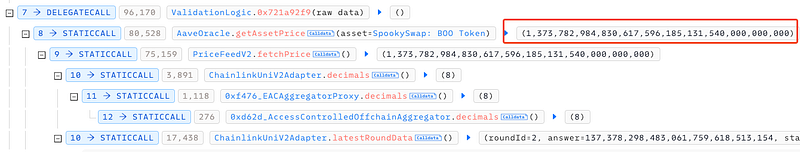
- Using this manipulated spot price, the attacker was able to deposit just 1 BOO token into a Polter lending pool as collateral. Due to a logic flaw in the oracle, the AaveOracle used a flawed price feed that evaluated the 1 BOO token at an inflated value of $1.37 trillion instead of its actual market value.
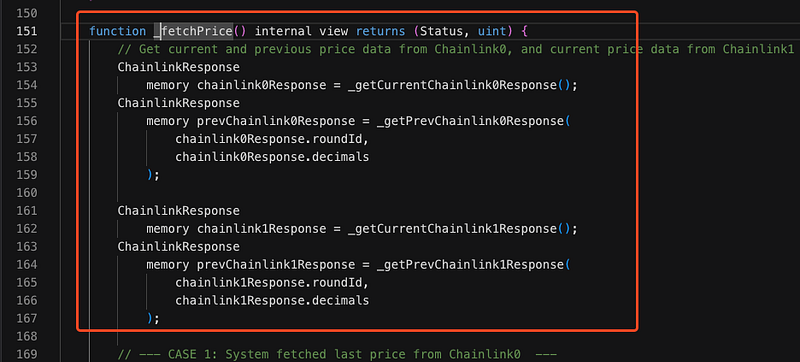
- The ChainlinkUniV2Adapter contract was used to fetch the current price of the BOO token. However, the contract did not have any safeguards in place to check for drastic price fluctuations resulting from the flash loan. The
_fetchPricefunction, which retrieves the price data, fetched the manipulated, inflated price from the liquidity pools, which led to the incorrect collateral evaluation.
- The
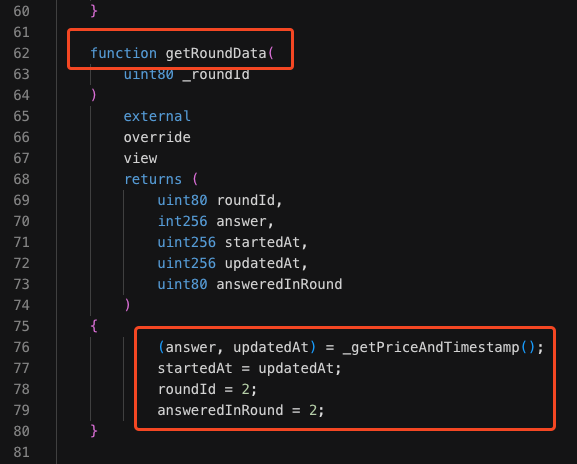
getRoundData()function, used for retrieving historical price data, also failed to validate significant price changes. It relied on the_getPriceAndTimestamp()function to fetch the price, but this function did not have checks in place to detect drastic price fluctuations, such as those caused by the flash loan manipulation.
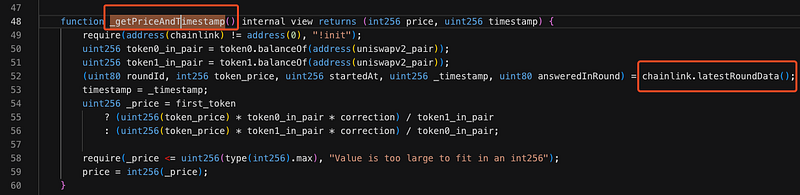
- As a result, the manipulated price was not validated before being returned. Additionally, the hardcoded
answeredInRound = 2value in the function did not account for whether the price data was accurate for the current round, further allowing the flawed price to pass unchecked.
- The
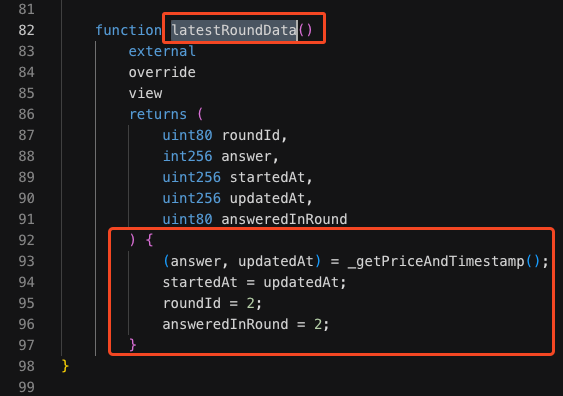
latestRoundData()function, which is supposed to return the most recent price data, was now returning incorrectly inflated prices due to the changes in liquidity caused by the attacker’s flash loan. It lacks validation to ensure the retrieved price (answer) is accurate and hasn’t been manipulated. It also uses hardcoded values forroundIdandansweredInRound, bypassing any dynamic price updates or validation. - The
getRoundData()andlatestRoundData()functions were supposed to ensure that the price of BOO tokens was consistent and accurate, but they failed to validate the large price changes resulting from the flash loan. The attacker exploited this flaw by providing a small amount of collateral but receiving an inflated price feed in return.
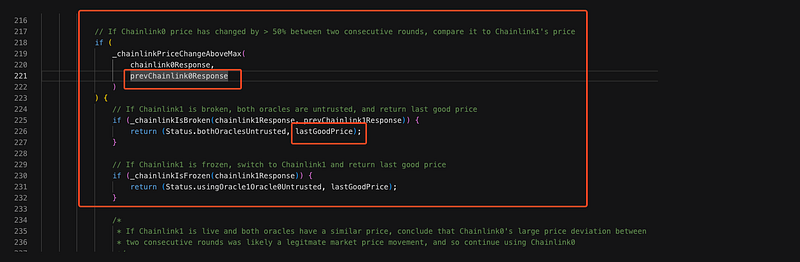
previousChainlink0Response mechanism- Additionally, the
previousChainlink0Responsemechanism, which was supposed to detect whether the price change exceeded a set threshold, failed to do so due to the lack of proper validation. As a result, the inflated price of 1 BOO token passed the oracle’s validation checks, leading to the miscalculation of collateral value. - The attacker continued to borrow wFTM tokens against the inflated collateral. As long as the manipulated price was maintained, they could repeat the borrowing process and drain the liquidity pools without limits. The oracle contract failed to detect these repeat borrowings because the price validation was not functioning properly.
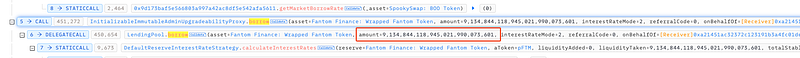
- The attacker borrowed 9,134,844 wFTM by using the inflated price of the BOO token as collateral, ultimately draining approximately $8.7 million from the Polter Finance lending pools.
- Polter Finance Team has initiated efforts to communicate with the attacker in order to retrieve the stolen funds: https://x.com/polterfinance/status/1858158065264324769
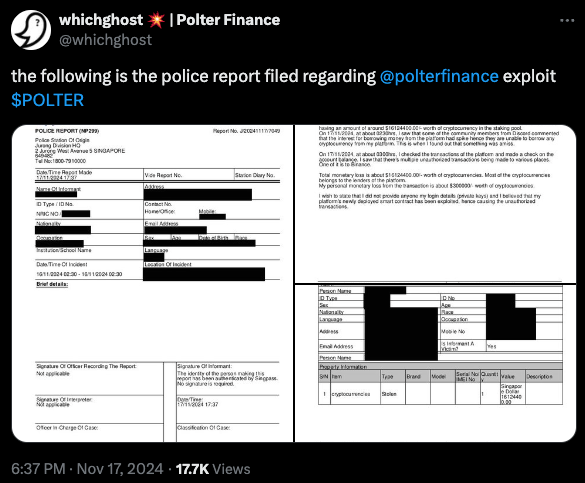
- A police report also has been filed: https://x.com/whichghost/status/1858134916632080648
Mitigation and Best Practices:
- Implement a mechanism to detect significant price changes over a short period, such as using a threshold or limit on price fluctuations. This would prevent drastic price changes caused by flash loans or manipulation from being accepted as valid.
- Introduce specific checks to detect flash loan activity. Since flash loans are often used for price manipulation in liquidity pools, adding logic to detect and counteract such activity (e.g., by ensuring that the price data used in calculations does not come from a pool with a drastically altered liquidity balance) could prevent exploits relying on flash loan manipulation.
- Limit the frequency of oracle price updates or add additional data sources for price validation to reduce the risk of relying on a single manipulated source.
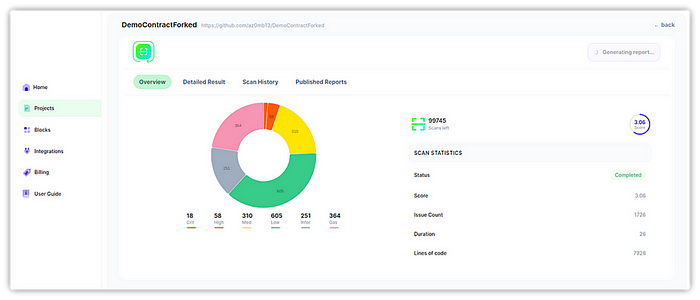
- To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Our public audit reports can be found on https://github.com/Credshields/audit-reports. Schedule a call at https://credshields.com/
- Scan your Solidity contracts against the latest common security vulnerabilities with 280+ detections at SolidityScan.
Conclusion:
SolidityScan is an advanced smart contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
