Orbit Chain Hack Analysis
Orbit Chain Hack Analysis
Overview:
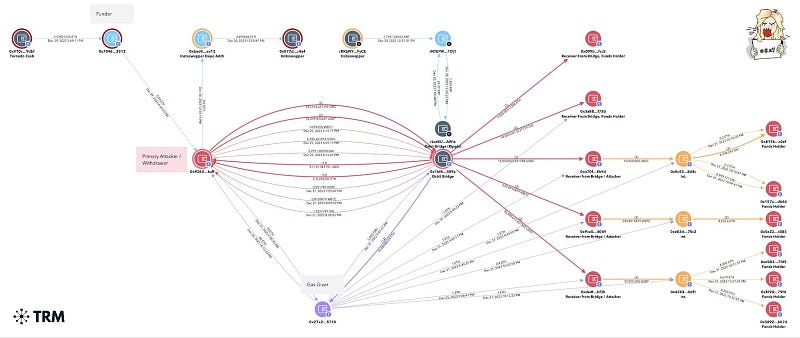
On January 1, 2024, Orbit Chain suffered an attack due to weak validation in the “withdraw” function and a weak signature validation issue, leading to an approximate loss of over 81M USD.
Smart Contract Hack Overview:
- Attacker address: 0x9263e7
- Vulnerable Contract: 0x1bf68a
- FundHolders:0x009b60 ,0x3a886a ,0x817bb1 ,0x157a40 ,0x5e22cb ,0xd283fa, 0xf49de4, 0x589257
- Receivers:0x009b60,0x3a886a,0xa70f89,0x9ca536,0xdadfa3
- Intermediaries:0x0c43ed, 0x42839f, 0xe03d37
- Attacker Funder: 0x70462b
- Attack Transactions: 0x958aee, 0xe0bada,0x64a6f4,0x639d27
Decoding the Smart Contract Vulnerability:
1. Inadequate Validation in the “withdraw” Function

The “withdraw” function lacks sufficient validation for the token parameter, as well as ensuring the withdrawal amount (uint[0]) is available in the vault. While the function checks signatures, chain IDs, and used withdrawals for validation, critical checks are missing:
-No validation on the provided token parameter, allowing an exploiter to specify any token address for withdrawal.
– Absence of a check ensuring that the uint[0] (amount) matches the actual vault balance of the specified token.
– Direct transfer of tokens based on supplied parameters without verifying if ‘msg.sender’ has the proper authorization to withdraw that token and amount.
– Failure to check whether Vault balances are greater than or equal to withdrawal amounts for the specified token.
This oversight allows overdrawing arbitrary amounts of any token, completely bypassing access controls and vault balance protections.
This vulnerability is not limited to a single instance of exploitation; it can be systematically abused, potentially depleting the vault of various tokens. This flaw resulted in the exploitation of significant assets, including $30M USDT, $10M DAI, $10M USDC, 231 wBTC (~$10M), and 9,500 ETH (~$21.5M). Further details and references can be found in the comments.
2. Inadequate Signature Validation in the “_validate” Function
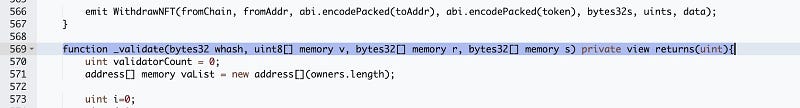
The “_validate” function exhibits two significant flaws, compromising the security of the system:
– Lack of Signature-Data Match Verification: The function fails to verify whether the signatures are associated directly with the specific withdrawal details. Instead, it only checks the validity of signers as owners. This vulnerability enables an exploiter to craft fake signatures using any owner’s private keys.
– Insufficient Signature Threshold Verification: The “_validate” function counts valid signatures without ensuring that the final count meets the required threshold for withdrawal. This oversight allows withdrawals to proceed with fewer signatures than expected.
As a result, the transfer process relies solely on unvalidated external input, enabling an exploiter to create and execute withdrawal transactions with any token addresses, withdrawal amounts, or recipient addresses
This unrestricted access facilitates fund theft without proper authorization or balance verification. The combination of these flaws could potentially allow an exploiter to generate fake signatures for a withdrawal transaction using a limited number of compromised owner keys, suggesting a potential compromise of private keys.

Mitigation and Best Practices:
- Before executing the token transfer, validate that ‘msg.sender’ has the proper authorization to withdraw the specified token and amount.
- Enhance the “_validate” function to validate that signatures correspond to the specific withdrawal details. This ensures that fake signatures cannot be constructed using unauthorized owner private keys.
- Always validate your code by writing comprehensive test cases that cover all the possible business logic.
- To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Schedule a call at https://credshields.com/
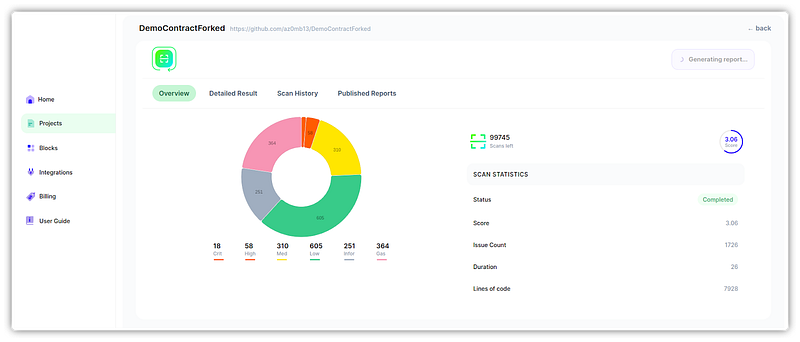
- Scan your Solidity contracts against the latest common security vulnerabilities with 130+ detections at SolidityScan
Conclusion:
SolidityScan is an advanced smart contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
SolidityScan — LinkedIn | Twitter | Telegram | Discord
