Nimbus DAO hack Analysis — Oracle Price Manipulation Bug
Nimbus DAO hack Analysis — Oracle Price Manipulation Bug
Overview:
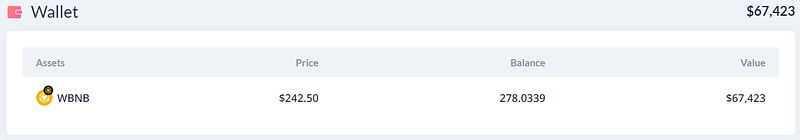
Yet another flash loan attack happened on December 14, 2022, which allowed attackers to steal 278 BNB worth around $76,000 from Nimbus DAO.
Smart Contract Hack Overview:
- Attacker’s transaction: 0x42f56d3
- Attacker’s address: 0x86aa1
- Flash loan transaction: 0x42f56d
- Staking contract: 0x3aa2b
- LockedStaking contract: 0x7060657
- Attacker’s wallet with tokens: 0x9D3B564983fd
Decoding the smart contract vulnerability:
- Because the reward computation depended on the number of tokens in the pool, the attacker attacked the logic by exploiting a flash loan to benefit.
- The price feeds of $NIMB and $GNIMB, the reward token, are necessary to determine the staking reward. The altered $NIMB minus $NBU WBNB pair is used to determine the price of $NIMB.
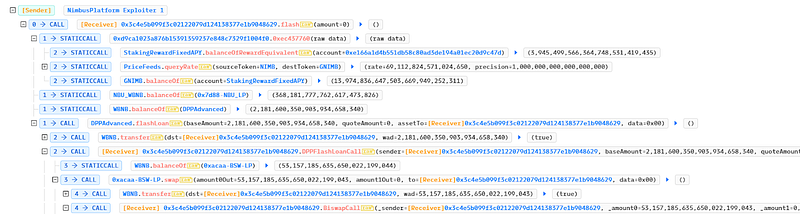
- As a result, the oracle’s price got tampered with, allowing the hacker to collect additional collateral incentives.
- To remove the majority of the $NIMB from the pool, the exploiter borrowed 75,477 $BNB and exchanged it for $NBU WBNB.
- The
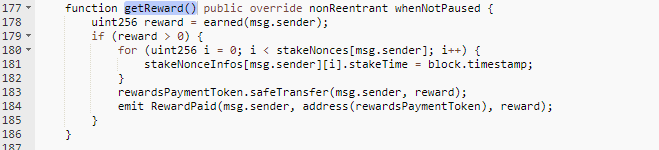
getReward()method permitted the hacker to earn a greater reward since the computation of the token reward was proportional to the ratio of $NIMB and $GNIMB in the pool.
- Following the flashloan attack, the ratio of Nimbus Utility tokens to Nimbus Governance tokens increased to 2919.7:1, which resulted in a greater payment. To repay the flash loan, the exploiter exchanged $GNIMB for $BNB.
Mitigation and best practices:
- The token’s logic must be evaluated, and it should not get inflated suddenly due to sudden price increases due to certain flash loan transactions.
- Protocols need to add security layers. In this case, use at least two oracles to verify the price. This would mitigate the hack and ensure proper checks on critical functions and publicly accessible variables.
- Price manipulation attempts can be mitigated to a greater extent via oracles such as Chain Links and input validation on those feed parameters to prevent stale data.
- To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShieldsprovide not only Smart Contract security but also provide end-to-end security of web applications and externally exposed networks. Schedule a call at https://credshields.com/
- Scan your contract against the latest common security vulnerabilities with 130+ patterns at SolidityScan, which includes the detection of Re-entrancy vulnerabilities.

Conclusion:
SolidityScan is an advanced smart-contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
