Mosca Hack Analysis
Mosca Hack Analysis
Overview:
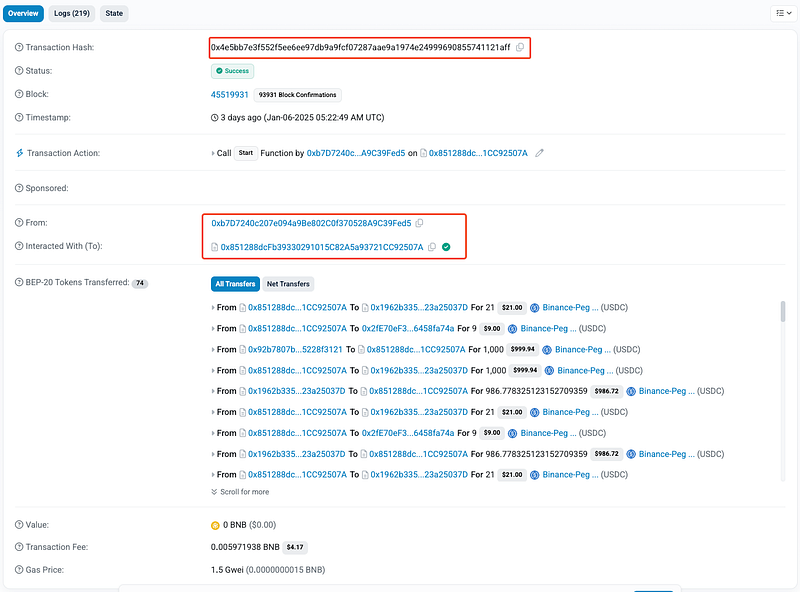
On January 8, 2025, the Mosca contract on Binance Smart Chain (BSC) was exploited due to incorrect balance calculations in the exitProgram function. The vulnerability allowed the attacker to withdraw tokens multiple times by exploiting improper state updates. The exploit resulted in a total loss of approximately $19.5K.
Smart Contract Hack Overview:
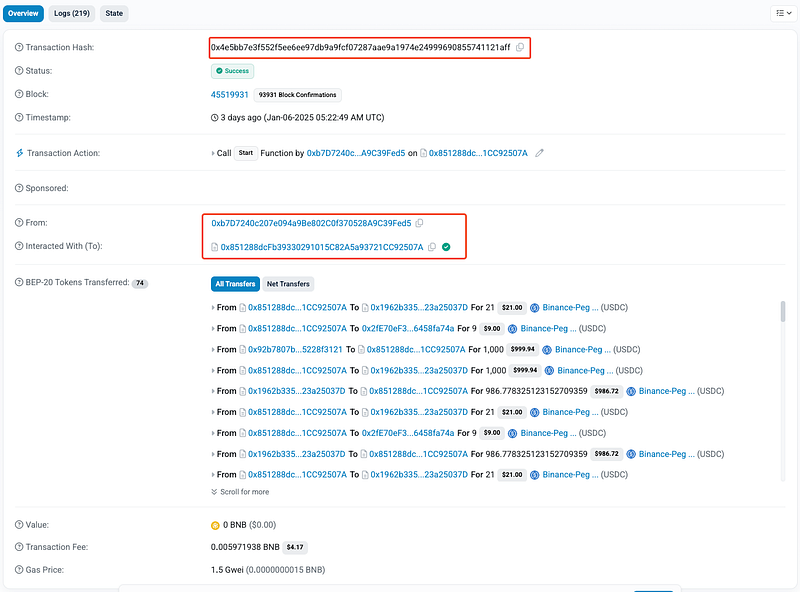
Decoding the Smart Contract Vulnerability:
- The root cause of the exploit lies in improper handling of balances and incomplete state updates in the
exitProgramfunction.
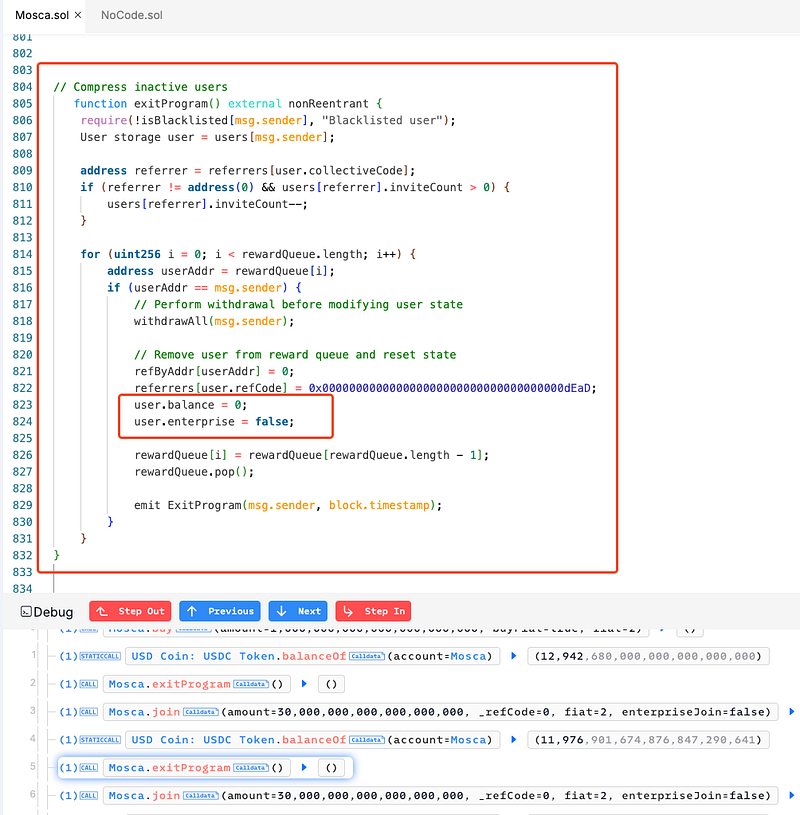
- Specifically, the
withdrawAllfunction calculates the total withdrawal amount usinguser.balance + user.balanceUSDT + user.balanceUSDC.
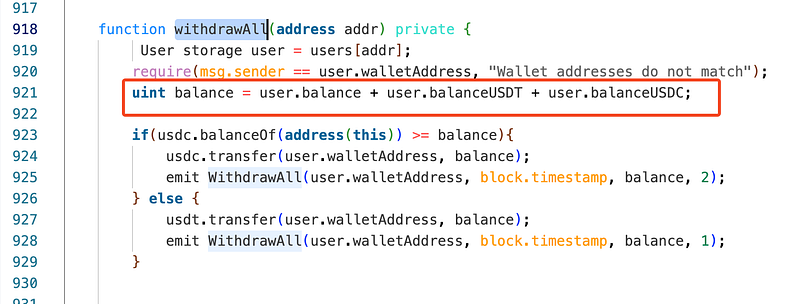
- However, after executing
withdrawAll, onlyuser.balanceis reset to 0, leavinguser.balanceUSDTanduser.balanceUSDCunchanged. - This oversight allowed repeated withdrawals when
user.balanceUSDToruser.balanceUSDCwas non-zero and therewardQueuewas not empty.
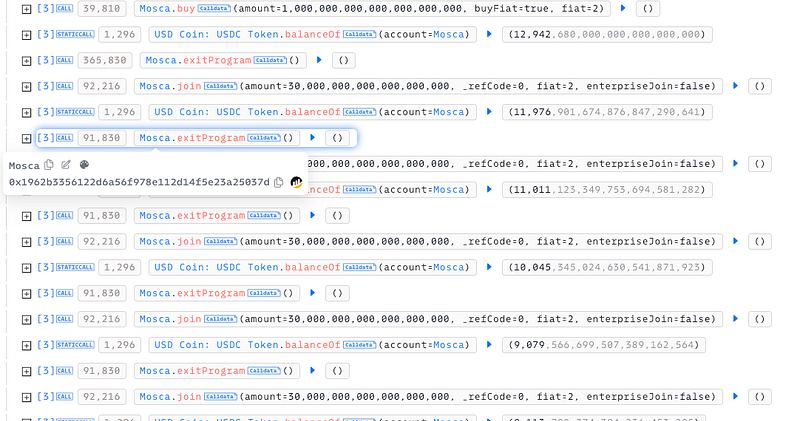
- The attacker called the
buyfunction to increase theiruser.balanceUSDC. Then, they invoked thejoinfunction to push their address into therewardQueue. And executed theexitProgramfunction multiple times, exploiting the incomplete reset ofuser.balanceUSDTanduser.balanceUSDC. - The attacker withdrew tokens repeatedly, ultimately gaining approximately $19.5K.
Mitigation and Best Practices:
- Ensure that all user balances (
user.balance,user.balanceUSDT,user.balanceUSDC) are reset to 0 immediately after withdrawal. This should be done before performing any other state-changing operations to prevent repeated withdrawals. - Also, introduce stricter access controls for critical functions such as
exitProgramandwithdrawAll. - Always reset all relevant variables after transactions, especially when handling funds or critical state changes. This helps ensure that once a withdrawal is completed, the user cannot exploit the contract by calling the withdrawal function again using the old balances.
- To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Our public audit reports can be found on https://github.com/Credshields/audit-reports. Schedule a call at https://credshields.com/
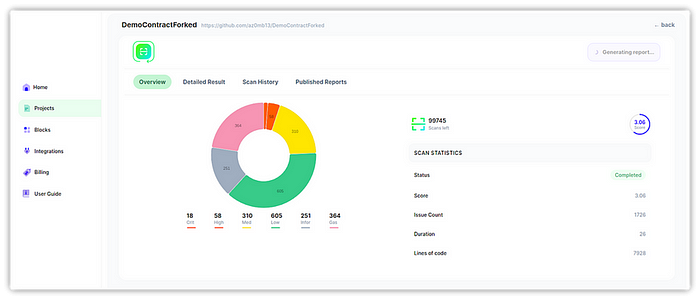
- Scan your Solidity contracts against the latest common security vulnerabilities with 280+ detections at SolidityScan.
Conclusion:
SolidityScan is an advanced smart contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
