MIMSpell Hack Analysis
MIMSpell Hack Analysis
Overview:
On January 30, 2024, MIMSpell suffered an attack due to a precision loss vulnerability, leading to an approximate loss of ~6.5M USD.
Smart Contract Hack Overview:
- Attacker address: 0x87f585
- Vulnerable Contract: 0x7259e1
- Attack contract: 0x193e04
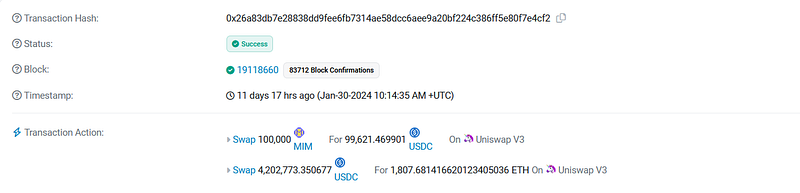
- Attack Transaction: 0x26a83d
Decoding the Smart Contract Vulnerability:
- The attacker exploited a vulnerability in the lending protocol by putting up an extremely low amount of collateral (100 wei), which allowed them to manipulate borrow and repay actions.
- Initially, the attacker engaged in borrowing and repaying a single token to inflate the ‘part’ variable, representing the borrowed amount of the user’s share in the total debt. Additionally, they executed the repayForAll function, reducing the ‘elastic’ variable.
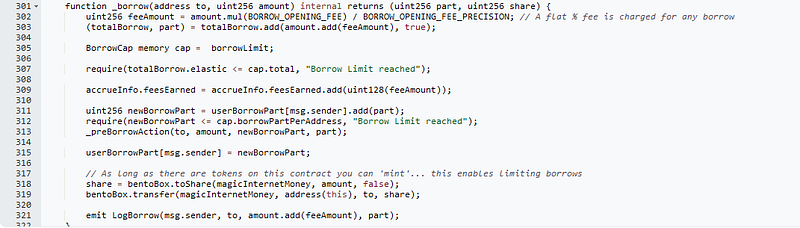
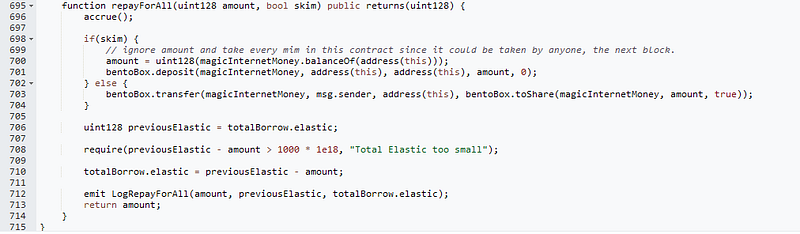
3. Due to the manipulation of variables, specifically the inflation of the base variable and deflation of the ‘elastic’ variable, a discrepancy arose in the Rebase Library.
4. The protocol’s rounding mechanism favoured the attacker, causing even negligible repayments to be rounded up in the protocol’s favour, essentially making the attacker repay more assets than borrowed shares.
5. Through this loop, the attacker managed to inflate totalBorrowShares to infinity while maintaining totalBorrowAssets at 1 wei, exploiting the protocol’s vulnerability.
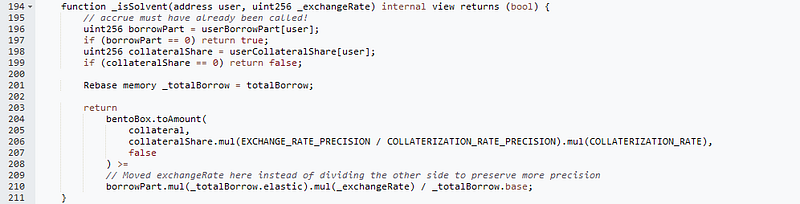
6. Despite having borrowed almost all the funds in the protocol with virtually no collateral, the attacker managed to evade detection during health checks. This evasion was due to the protocol’s incorrect calculation of borrowed amounts, which did not accurately reflect the magnitude of the attacker’s borrowing compared to another attacker with infinite borrowed shares.
Mitigation and Best Practices:
- A proposed fix for such vulnerabilities in lending protocols involves ensuring that the totalBorrowShares cannot be reduced to a value lower than totalBorrowAssets. This fix would prevent attackers from manipulating borrowing and repayment actions to exploit the protocol’s rounding mechanisms and evade detection during health checks.
- Always validate your code by writing comprehensive test cases that cover all the possible business logic.
- To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Schedule a call at https://credshields.com/
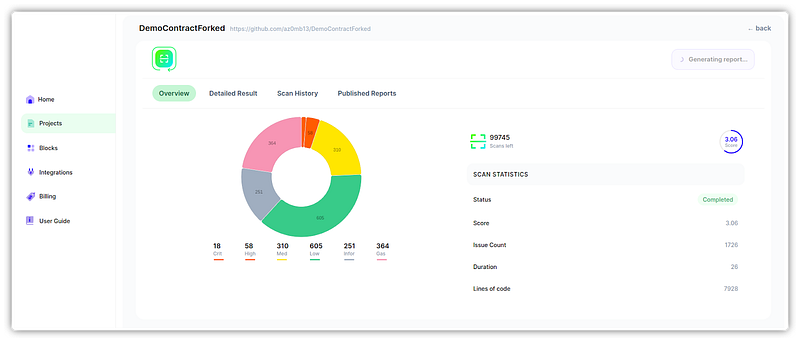
- Scan your Solidity contracts against the latest common security vulnerabilities with 130+ detections at SolidityScan
Conclusion:
SolidityScan is an advanced smart contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
SolidityScan — LinkedIn | Twitter | Telegram | Discord
