Midas Capital Hack Analysis
Midas Capital Hack Analysis
Overview
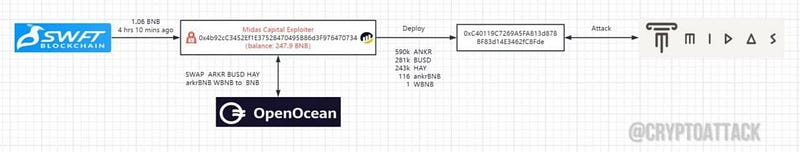
On June 18, 2023, Midas Capital suffered an attack, due to a rounding issue in its lending protocol leading to a loss of ~600K USD.
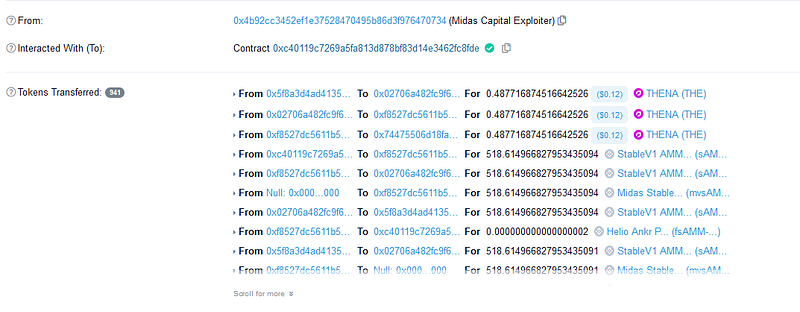
Smart Contract Hack Overview:
- Attackers address: 0x4b92cc
- Attack contract: 0xc40119
- Vulnerable contract: 0xf8527d
- Attack transaction: 0x1ebc03
Decoding the Smart Contract Vulnerability:
Let’s break down the hack into 2 phases:
Phase 1: Supplying Collateral and Minting LP Tokens
- The hacker used a special smart contract called “borrower” at address 0xd2094b870D80Cfb7DaDa4893aD0030d642CA9f72.
- They minted and supplied 21,184 LP tokens using the root attack contract.
- Most of the cTokens were redeemed, leaving only 1001 wei in the address.
- The hacker donated the redeemed 21,184 LP tokens to the market.
- The total supply of 1001 wei LP tokens was transferred to the borrower contract.
- Using a flash loan of ANKR, the hacker borrowed $25,000 worth of HAY and 1,148 ankrBNB.
- The ankrBNB was swapped for BUSD using the root attack contract.
- With these assets, they minted 259,826.61 HAY/BUSD LP tokens valued at around $519,000.
- These LP tokens included the hacker’s initial funding of $220,000 worth of HAY and $22.3k worth of BUSD.
- Additional assets were borrowed from the Ankr-Helio pool: $251,000 BUSD and $25,000 worth of HAY.
- The core of the exploit relied on the redeemability of 1001 wei of cTokens for such a significant value.
Phase 2: Borrowing Assets, Repaying Flash Loan Fees and Exploitation of the vulnerability
- The hacker borrowed assets from the Ankr-Helio pool by supplying $689,000 worth of ANKR collateral.
- They also borrowed 115 ankrBNB (worth approximately $28,700) from the pool and supplied it back from another contract (liquidator).
- This bypassed the debt ceilings on borrowing ankrBNB collateralized by HAY/BUSD LP Tokens.
- Using the fresh collateral, they borrowed a smaller amount of ANKR (around $13,500) to repay the flash loan fees.
- The hacker redeemed the supplied $689,000 worth of ANKR, leaving $519,000 worth of collateral and $320,000 worth of debt in the pool.
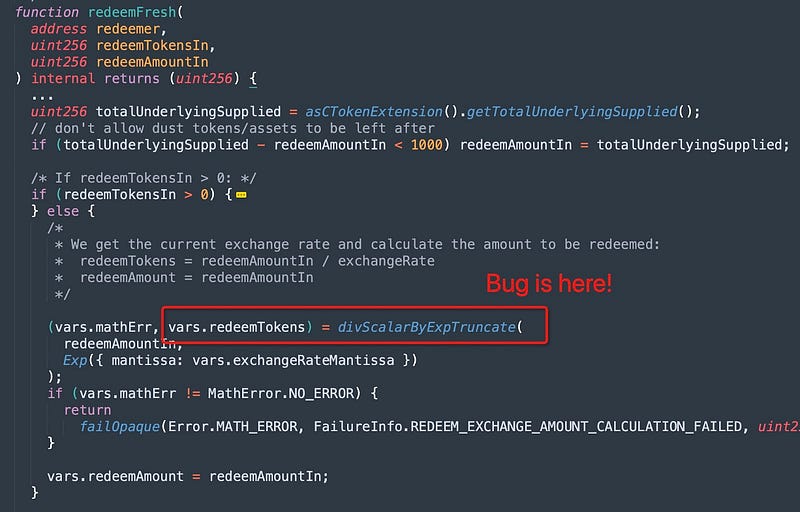
- They repaid the flash loan and withdrew 519.13 LP tokens, using just 1 wei of the market cToken.
- The reason for choosing 519.13 LP tokens out of the currently held 259,826.61 LP tokens in the market is due to a specific calculation. This calculation is based on the fact that 519.13 LP tokens represent 0.1998% (1.998 wei) of the total supply of 1001 wei. However, there is a bug in the system, causing the calculation to round down to just 1 wei instead of rounding up to 2 wei.
- In the final phase, the hacker performed self-liquidations. When the value of the partially damaged LP tokens reached approximately $30,000, they utilized 90.9 out of the 115 ankrBNB they had supplied to settle their own outstanding debt. This self-liquidation process allowed them to take possession of the LP tokens and redeem them for the remaining value they held.
Mitigation and Best Practices:
- Performing multiplication before division is a recommended practice in Solidity to minimize rounding errors. By multiplying before dividing, you can maintain higher precision in your calculations. This practice helps preserve the accuracy of the final result and reduces the potential for rounding issues that could affect the outcome of your smart contract operations.
- Always validate your code by writing comprehensive test cases that cover all the possible business logic.
- To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Schedule a call at https://credshields.com/
- Scan your Solidity contracts against the latest common security vulnerabilities with 130+ detections at SolidityScan

Conclusion:
SolidityScan is an advanced smart-contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
SolidityScan — LinkedIn | Twitter | Telegram | Discord
