Li.Fi Hack Analysis
Li.Fi Hack Analysis
Overview:
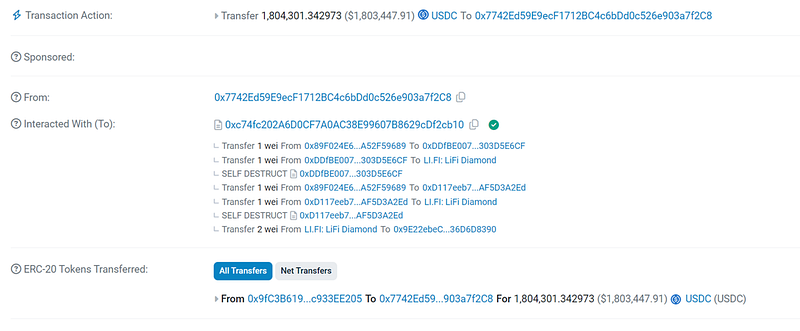
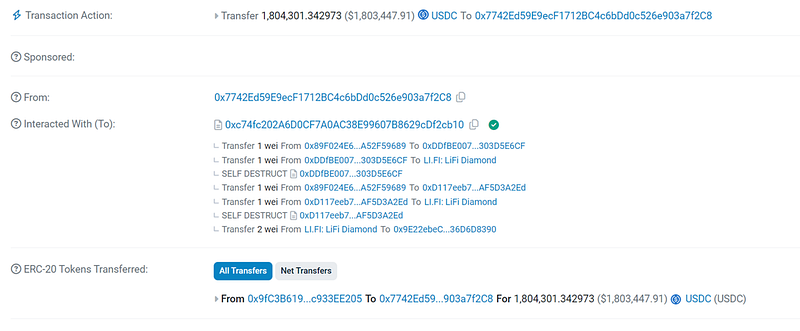
On July 16th, 2024, Li.Fi- a cross-chain DeFi protocol (@lifiprotocol) fell victim to an attack exploiting arbitrary call vulnerability, resulting in a loss of approximately $8 Million.
Smart Contract Hack Overview:
- Attacker’s Address: 0x7742E
- Related Address Chain: 0x8B3Cb, 0x53671, 0x9cc93, 0x6a6df
- Exploit Address: 0xc74fc
- Vulnerable Contract: 0xf28A3
- LiFi Router: 0x1231D
- Attack Transactions: 0xd82fe, 0x65a92
Decoding the Smart Contract Vulnerability:
· The root cause is that the function depositToGasZipERC20 in GasZipFacet.sol allowed _swapData to be passed directly to LibSwap.swap, which included a low-level call (shown in Fig: Vulnerable Code) that can execute arbitrary functions. As _swap.callTo and _swap.callData is user-controlled, the attacker could craft a malicious calldata with transferFrom() calls.
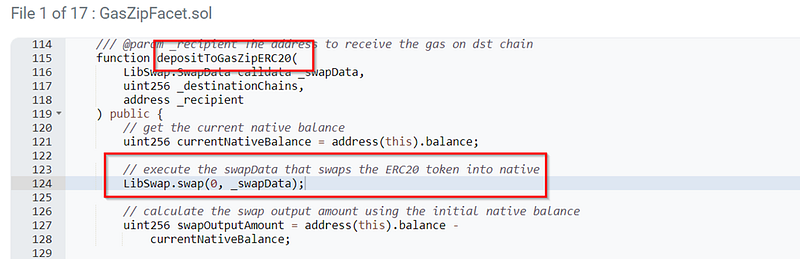
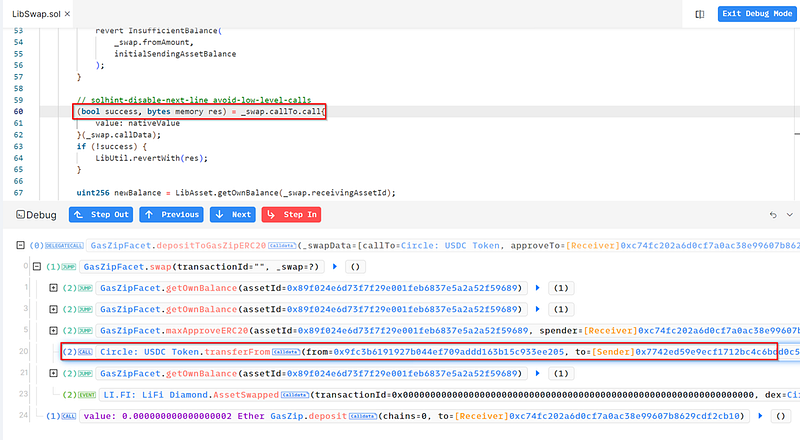
· Since the attacker could control _swapData and the contract had sufficient approval to spend tokens, they were able to steal from the bridge by making unauthorized transferFrom() calls.
· Li.Fi protocol’s X account has already issued warnings suggesting users should revoke all approvals for:
0x1231deb6f5749ef6ce6943a275a1d3e7486f4eae
0x341e94069f53234fE6DabeF707aD424830525715
0xDE1E598b81620773454588B85D6b5D4eEC32573e
0x24ca98fB6972F5eE05f0dB00595c7f68D9FaFd68
· LiFi protocol posted that the exploit has been contained and the affected smart contract facet disabled. The only wallets affected were set to infinite approvals and represented only a very small number of users.
· Revoking information can be found at https://revoke.cash/ and https://revoking-li.fi/
· Interesting thing that Li.Fi protocol lost nearly $600,000 in 2022 to the same bug in the protocol’s swapping feature.
Mitigation and Best Practices:
· Validate and sanitize the _swapData input to ensure it cannot be used to make arbitrary calls. Specifically, restrict the possible destinations and function signatures that can be called.
· Instead of granting infinite approvals, set token allowances to the exact amount needed for each transaction.
· Always validate your code by writing comprehensive test cases that cover all the possible business logic.
· To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Our public audit reports can be found on https://github.com/Credshields/audit-reports. Schedule a call at https://credshields.com/
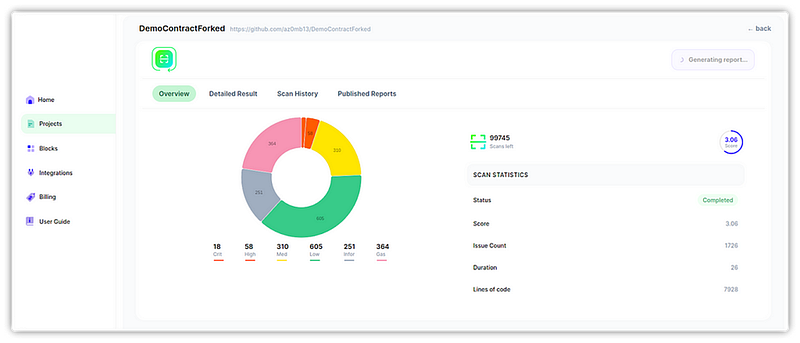
· Scan your Solidity contracts against the latest common security vulnerabilities with 225+ detections at SolidityScan.
Conclusion:
SolidityScan is an advanced smart contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
