Jump & Oasis Crypto Counter-Exploit Hack Analysis
Jump & Oasis Crypto Counter-Exploit Hack Analysis
Overview:
Due to a misconfiguration in the roles and privileges of the Oasis automation bot, which allowed the attacker to get access to the vault by adding an automation trigger to the Oasis vault, a $227 million counter-exploit for wormhole exploit occurred on February 21, 2023.
Smart Contract Hack Overview:
- Oasis Auto Buy/Sell service:auto-buy-and-auto-sell
- wstETH vaults:30100,30179
- Oasis Multisig contract: 0x85f9b7
- Holder’s Address: 0x5fec2f3
- Sender’s Address(Jump) : 0x04e1e2
- Wormhole Deployer 1: 0xf8aae8
- Jump Trading: 0xf584f87
- Stop-Loss Trigger: 0xf11f1225
- Execution trace: 0xf11f1
- Upgradable Proxy Pattern: upgrading/#proxy-patterns
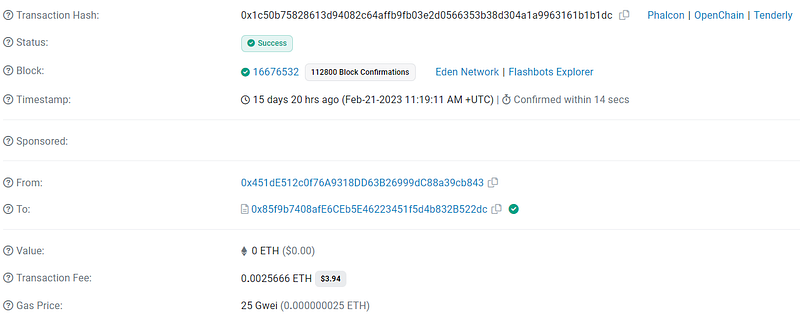
- Attacker’s Transaction: 0x4f41173,0x1c50b75
- Multi-sig signers addresses: 0x9365,0xBc2e,0x81a68,0x451dE
Decoding the Smart Contract Vulnerability:
- The Oasis multi-sig contract was first signed by the sender’s address (0x04e1e2) as part of the attack. This utilized an upgradeable proxy contract to allow the sender to modify the oasis contract’s settings. After the first five transactions, the sender’s address was taken out of the multi-sig, yet it was still permitted to sign for 1 hour and 53 minutes.
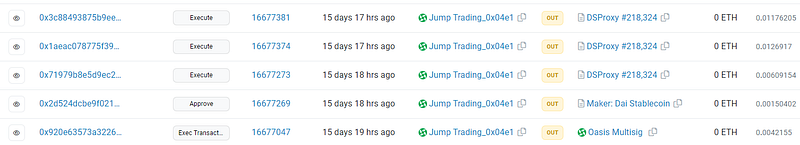
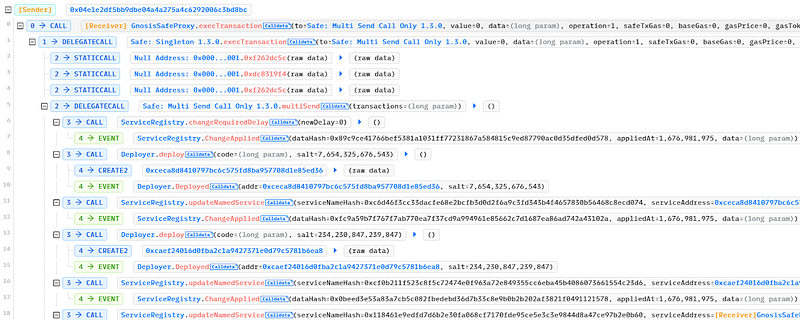
2. To allow the counter exploit, the limited time signer (0x04e1e2) initialized a few settings.
- Using its rights, the Sender first changed the ServiceRegistry’s change delay setting to 0 so that it could immediately update proxy contract addresses.
- The two Oasis proxy contracts were then updated by the Sender to attacker-controlled addresses. In Layman’s terms, one was utilized for logic execution and the other for authorization.
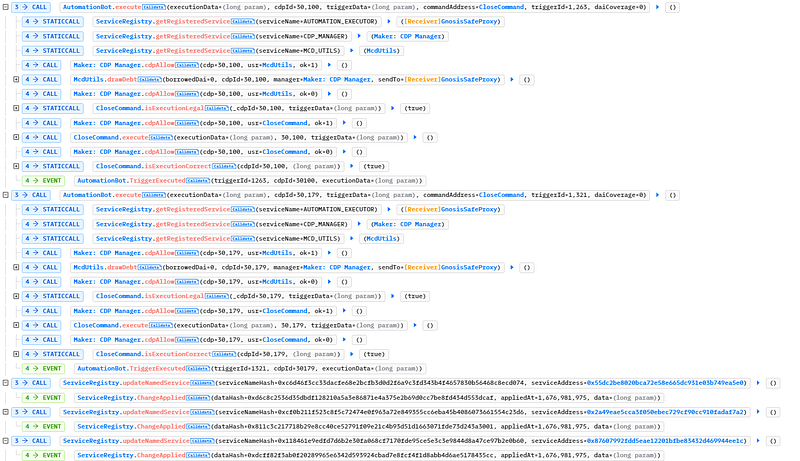
- The Oasis Multisig proxy address was then changed to the AutomationExecutor proxy address, giving the Sender full authority over vault 30100.
3. The sender (0x04e1e2) closed vault 30100 and moved its positions to a different vault that is under the control of the multi-sig in the following exploit phase.
- The AutomationExecutor contract, which gave vault 30100 complete control, was replaced with Oasis multi-sig.
- The Sender was able to close the vault when the attacker’s tricked Authorize contract was called.
- The Executor contract was then carried out, creating the new vault 30231, and migrating the debt and collateral from 30100 to the 30231 vaults. At last transferred Oasis Multisig ownership of 30231.
- The final result was the transfer of 76.39M of borrowed DAI and 120,695.43 of wstETH collateral from vault 30100 to vault 30231.
- The counter-exploit was finished, Vault 30100 was confirmed, and the proxy contract addresses were returned to their original addresses.
4. The collateral was taken out of the wstETH and rETH vaults after the DAI debt( flash loan) was paid off and the remaining tokens were transferred to the holder’s address (0x5fec2f3).
Mitigation and Best Practices:
- Nevertheless, neither Oasis nor Jump has officially addressed or confirmed these counter-exploits. The contract must have appropriate access controls and roles.
- There shouldn’t be any system that allows a user to sign in for an extended period of time.
- The upgradeable proxy should be protected from all potential threats in order to update logic.
- To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Schedule a call at https://credshields.com/
- Scan your Solidity contracts against the latest common security vulnerabilities with 130+ detection at SolidityScan including access control vulnerabilities.

Conclusion:
SolidityScan is an advanced smart-contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
SolidityScan — LinkedIn | Twitter | Telegram | Discord
