Jimbo Protocol Hack Analysis
Jimbo Protocol Hack Analysis
Overview:
On May 29, 2023, Jimbo protocol suffered a protocol-specific price manipulation attack, leading to a loss of ~8M USD.
Smart Contract Hack Overview:
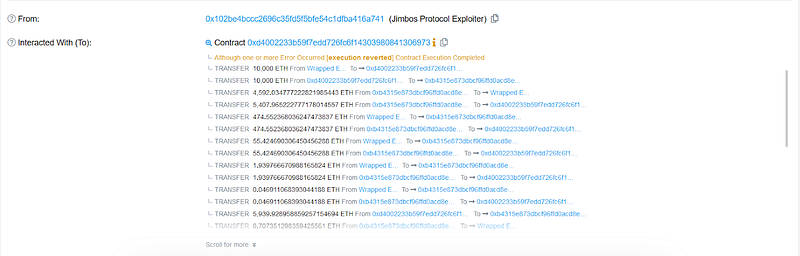
- Attackers address: 0x102be4
- Contract ($JIMBO): 0xc38136
- Contract(JimboController): 0x271944
- Attackers transaction: 0x44a0f5
Working of JIMBO Protocol :
$JIMBO is a Self Market-Making Liquidity Bin Token integrated with TraderJoe. In TraderJoe, a bin is similar to a tick in Uniswap V3. $JIMBO automatically adjusts its liquidity distribution when the price changes.
Here are some key points about how $JIMBO works:
- When the active bin is above the trigger bin, you can call the shift function to create anchor bins and a new floor bin. This helps to prevent the price from decreasing too much.
- When the anchor bins are depleted, the price is about to fall to the floor price, you can call the reset function to flatten the $JIMBO liquidity above the floor bin. This encourages users to buy back Jimbo at a relatively lower price.
Decoding the Smart Contract Vulnerability:
- The hacker used flash loans to borrow 10,000 WETH and exchanged them for $JIMBO tokens, artificially inflating their price.
- They transferred 100 $JIMBO tokens to the JimboController contract for liquidity addition.
- By invoking the shift function, the hacker allowed anyone to remove existing liquidity and add new liquidity, resulting in all WETH funds from the JimboController contract being used for liquidity.
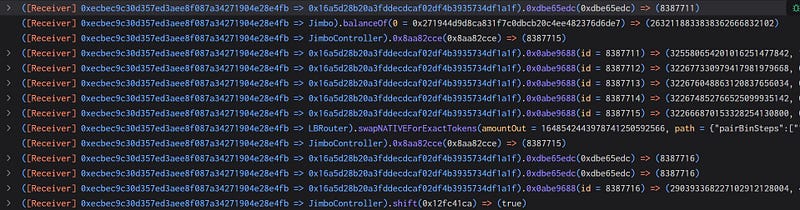
- Due to the imbalanced situation caused by the inflated $JIMBO price, the hacker obtained a greater amount of WETH when adding liquidity.
Mitigation and Best Practices:
- Ensure that the token calculation is done properly keeping in mind the external factors.
- Thoroughly test the contract’s functionality under various scenarios and edge cases to identify and address potential logic flaws or vulnerabilities. Write test cases for each possible scenario.
- To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Schedule a call at https://credshields.com/
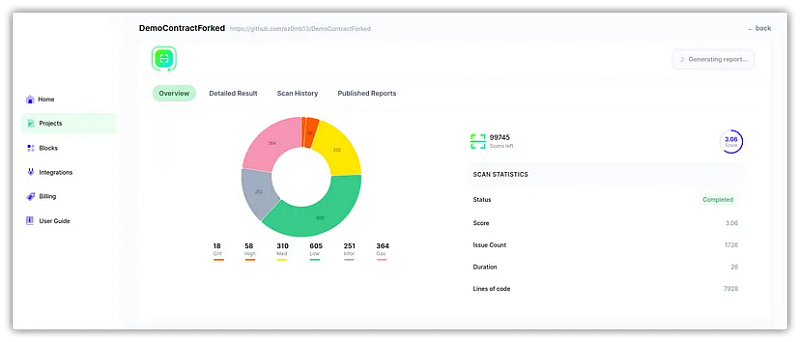
- Scan your Solidity contracts against the latest common security vulnerabilities with 130+ detections at SolidityScan.
Conclusion:
SolidityScan is an advanced smart-contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
SolidityScan — LinkedIn | Twitter | Telegram | Discord
