JAY Token Exploit — Reentrancy Attack
JAY Token Exploit — Reentrancy Attack
Overview:
A tax-loss harvesting app for NFTs called Jaypeggers was breached on December 29, 2022, and the attacker stole about 15.32 ether, or about $18.5k. The price of the JAY token was effectively manipulated using a contract-level reentrancy attack. This vulnerability could have been found if SolidityScan had been used to scan the contract.
Smart contract hack overview:
- Attackers Address: 0x0348d2
- Attackers Transaction: 0xd4fafa1
- Attacker’s exploit contract: 0xed42cb1
- JAY Token’s official contract: 0xf2919d1
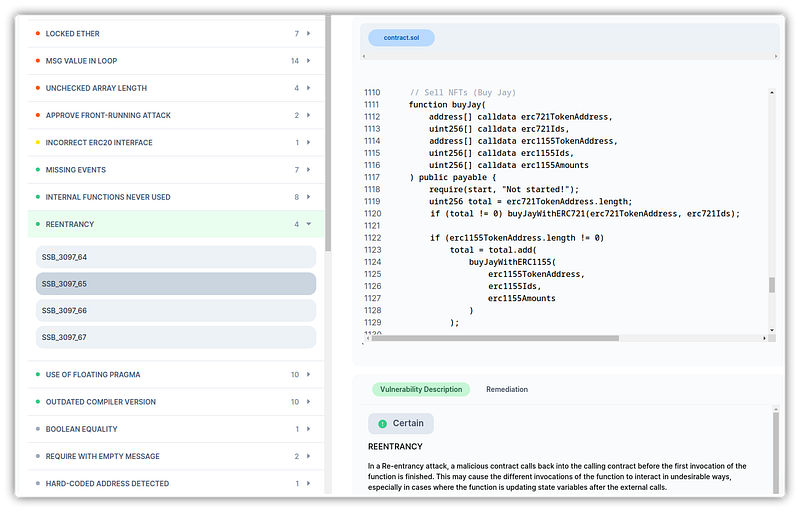
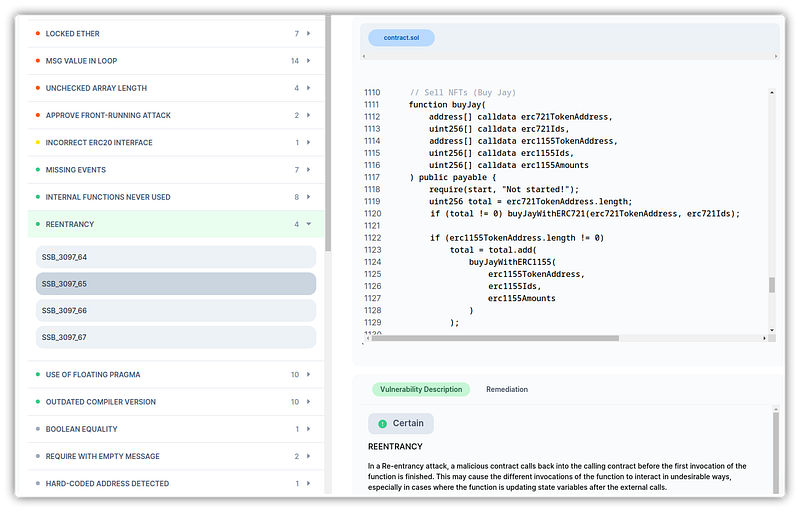
Decoding the smart contract vulnerability
- The buyJay() method in the JAY contract supported any ERC-721 token as a parameter.
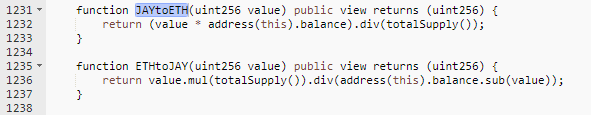
JAY Token price = Total Ether balance in JAY contract / Total Supply of JAY token
- The attacker used the buyJay() method, submitted a fraudulent ERC-721 token, and purchased the corresponding JAY token.
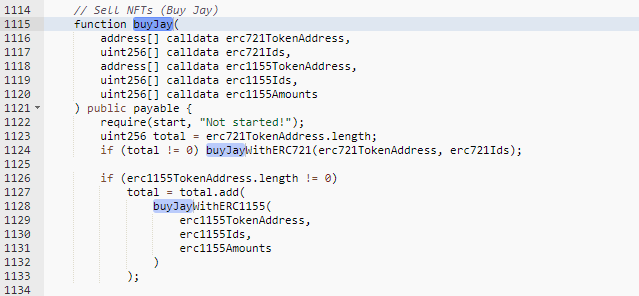
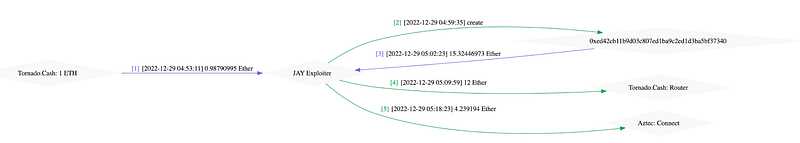
- The attacker specifically borrowed 72.5 ETH for a flash loan and then spent 22 ETH to purchase the JAY token. The buyJay function was called with another 50.5 ETH with the fake ERC-721 token.
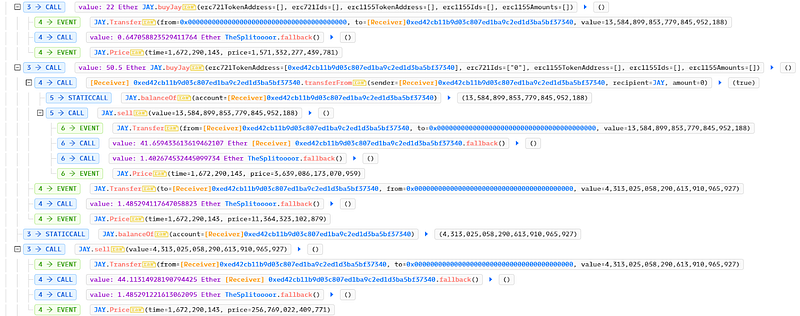
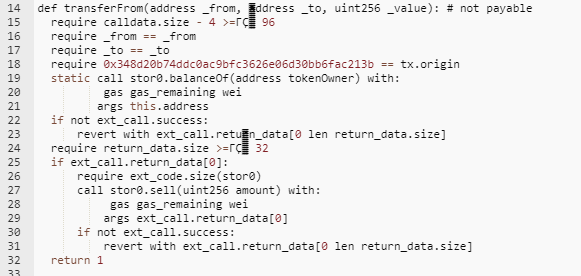
- During the transfer, the attacker executed and reentered the JAY contract by invoking the sell function on the fake ERC-721 token and sold all JAY tokens. The JAY token price got manipulated since the Ether balance was raised before the buyJay function was initiated.
- With a profit of 15.32 Ether, the attacker carried out the method twice in a single transaction. Tornado Cash was used to launder the attacker’s funds.
Mitigation and best practices:
- Always verify user inputs such as token addresses, amounts, and IDs to prevent manipulation and exploitation to steal users’ funds.
- Use function modifiers that prevent reentrancy, such as Open Zepplin’s Re-entry Guard.
- Always ensure that any state changes, such as updating balances or calling internal functions before executing external code, take place internally first. Follow the checks-effects-interactions pattern.
- To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Schedule a call at https://credshields.com/
- Scan your contract against the latest common security vulnerabilities with 130+ patterns at SolidityScan, which includes the detection of Re-entrancy vulnerabilities.

Conclusion:
SolidityScan is an advanced smart-contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
