Jarvis Polygon Pool Hack Analysis — Read Only re-entrancy
Jarvis Polygon Pool Hack Analysis — Read Only re-entrancy
Overview:
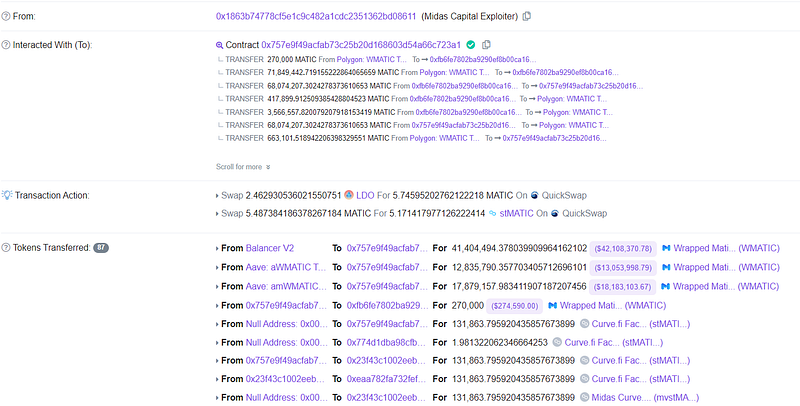
- On January 15, 2023, a read-only reentrancy exploit on the Jarvis pool of Midas Capital resulted in a loss of 663101 MATICs, which almost rounded to 650k.
Smart Contract Hack Overview:
- Attacker’s transaction: 0x00534
- Attacker’s address: 0x1863b7
- Attacker’s Contract: 0x757e9f
- Jarvis jFIAT Contract: 0x23f43c
- Re-entrancy vulnerable contract Vyper: 0xfb6fe780
Decoding Smart Contract Vulnerability
- The attacker flash loaned a huge amount of WMATIC tokens and modified the jFIAT token’s liquidity after transferring the tokens to the Jarvis pool.

- Another 270k MATIC was spent, and 131k jFIAT tokens were created by the attacker. As a result, the price of jFIAT tokens was fraudulently manipulated and inflated by 10 times.
- The debt was settled using the attacker’s contract, and 103k jFIAT tokens were redeemed in return.
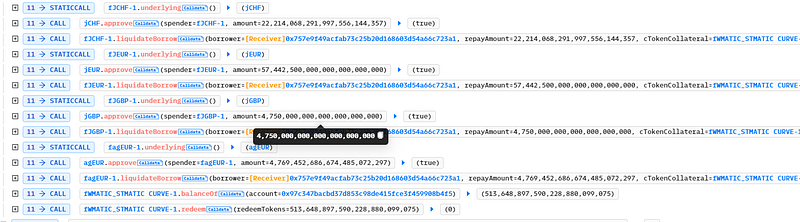
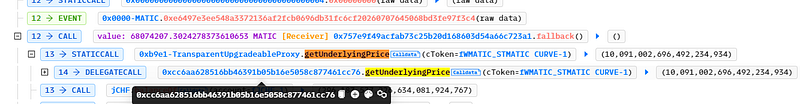
- The remove liquidity function, which gave the user tokens after removing liquidity, was vulnerable to re-entrancy. When MATIC transferred tokens to the contract, it was reentered.
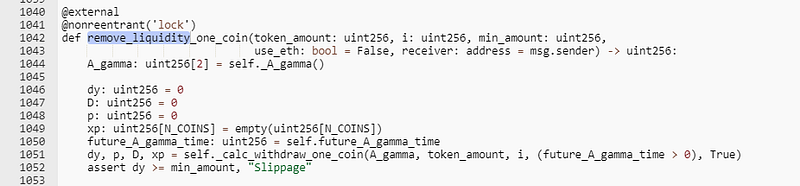
- Since the initial price was checked before & was not checked after the removal of tokens, the attacker raised the price before invoking the remove liquidity function and exploited the re-entrancy problem in removing liquidity which resulted in an incorrect price and profited for the attackers.
Mitigation and Best Practices:
- To ensure that the pricing data is appropriately updated and that there are no conflicts, state variables in the case of the external calls must be updated before the call is completed. Follow a checks-effects-interactions pattern.
- To avoid vulnerabilities brought on by flash loans that might result in price manipulation, it is advised to employ price oracles from chainlink.
- Always ensure that every state change happens before calling external contracts, i.e., update balances or code internally before calling external code.
- Use Open Zepplin’s Re-entrancy Guard.
- Always verify user inputs such as token addresses, amounts, and IDs to prevent manipulation and exploitation to steal users’ funds.
- To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Schedule a call at https://credshields.com/
- Scan your Solidity contracts against the latest common security vulnerabilities with 130+ patterns at SolidityScan, which includes the detection of Re-entrancy vulnerabilities.

Conclusion:
SolidityScan is an advanced smart-contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
SolidityScan — LinkedIn | Twitter | Telegram | Discord
