Harmony Bridge Hack Analysis
Harmony Bridge Hack Analysis
Overview:
The Harmony Bridge hack occurred on June 24, 2022, draining around $100 million from the Harmony bridge. This attack was not caused by a flaw in the smart contract code or bridge but rather by the attackers who compromised at least two of the four bridge validators’ multi-sig wallet private keys and gained control of the spanned assets.
The private keys were only saved in an encrypted format on the server, and their logic was only available on the server. An attacker could not gain access to those keys without compromising any internal employees. It was suspected that the attackers used a phishing scheme to trick at least one software developer into installing malicious software on their laptop, which allowed the attackers to either read chat threads to understand how to operate the bridge and/or gain access to non-public bridge infrastructure code and backdoor access to one or more servers to perform the hack.
The attack resulted in the loss of 85,867 ETH, 990 AAVE, and 78,500,000 AAG on Ethereum, 5,000 BNB, and 640,000 BUSD on BNB Chain, for a total of about $100,428,116.
Decoding the Hack:
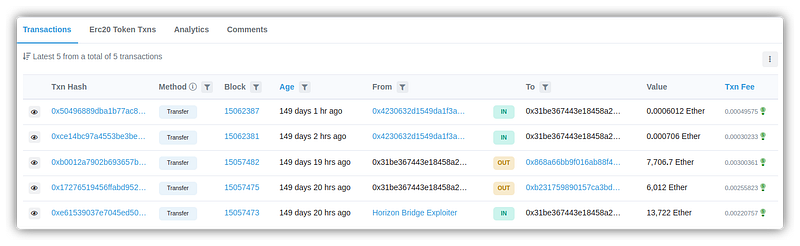
- Attacker’s address: 0x0d0431
- Harmony ETH Bridge address: 0xf9fb1
- Harmony ERC20 Bridge address: 0x2dCCD
- Harmony BUSD Bridge address: 0xfd53b1
- Harmony Bridge all ERC20 token transactions: 0x0d0431
- Victim contract: 0x715cd
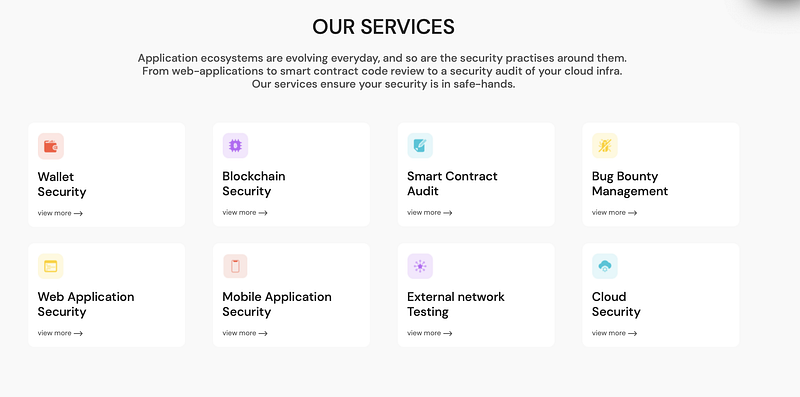
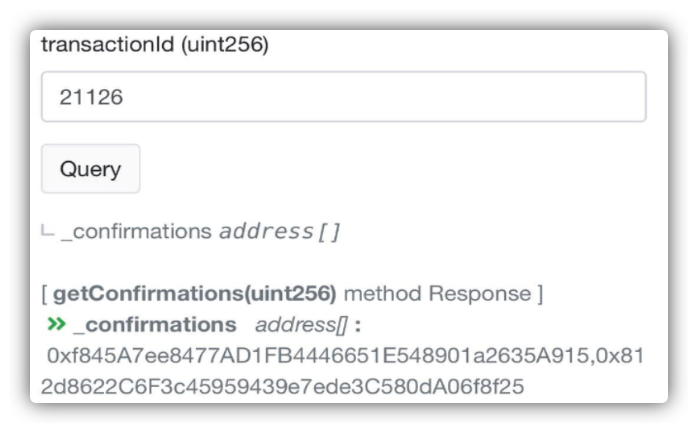
- Wallets that confirmed
unlockTokenstransaction: 0xf845A7 0x812d8 - Transaction hash: 0x6e5251068
- Related TransactionId:
21106–21118 (ETH)
120515–120518 (BNB)
Technical Analysis:
- A week before the attack, it was revealed that there was a vulnerability in software packages supplied with our internal subgraph service that exposed all server addresses within a private cloud environment.
- Prior to the June 23rd bridge attack, the technical team was working to resolve this issue.
- There were server logs with date and timestamps discovered, which indicated that the culprit began analyzing Horizon Bridge implementations as early as June 2nd and managed to decode various keys on the server. The above combination demonstrated a well-planned attack to carry out the hack.
- It was also discovered that Harmony’s multi-sig wallet code was not verified and was derived from the ConsenSys multi-sig wallet contract code.
Root Cause Analysis:
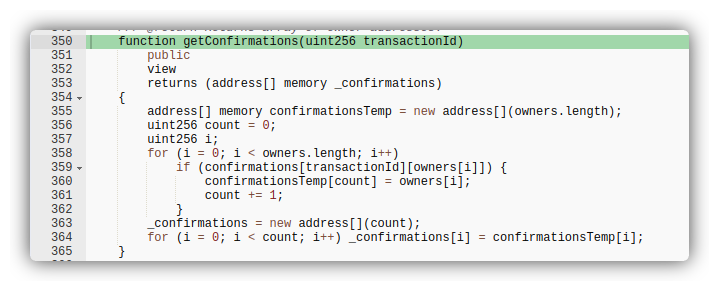
getConfirmations()function was responsible for confirming all the transactions.
- After inspecting transaction 21108, it was discovered that two multi-sig wallets were utilized to confirm the transactions.
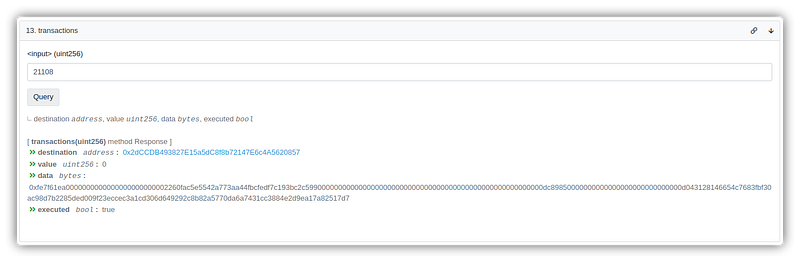
- Wallets that verified the transaction involving unlockTokens:
1. 0xf845A7ee8477AD1FB4446651E548901a2635A915
2. 0x812d8622C6F3c45959439e7ede3C580dA06f8f25 changeRequirement()function which allowed the change of the number of required confirmations.
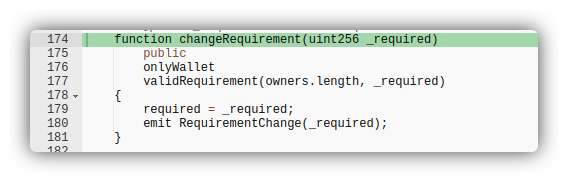
- TransactionId 21126 increased the minimum to four, which was also approved by the same two wallets in the multi-signature transaction. It meant that the five-person harmony bridge had two wallets approve the transactions.
- Following the attack, the number of validators necessary to sign a transaction was increased to four, and signatures were changed to improve security.
Mitigation best practices:
- Need additional validators and make sure that others are not put in danger if one private key is compromised.
- The recommended practice for managing high-value assets is to employ multiple signatures, although additional validators should be used to achieve the highest level of security.
- Use the latest versions and fix all security holes in the utilized libraries.
- Review larger transaction amounts actively and employ bots to halt problematic transactions and notify the community and the responsible teams.
Conclusion:
Sometimes Smart Contract owners focus too much on the security of smart contracts and completely forget awareness training of all employees and overall organization security and implementation of company-wide security practices. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Schedule a call at https://credshields.com/