GYM Network Hack Analysis
GYM Network Hack Analysis
Overview:
An attack happened on June 10, 2022, due to a newly released feature in the GYM NETWORK protocol.
While GYM NETWORK was focused on developing the ideal exercise for its members to receive the most yields and incentives, a new feature was implemented that caused the project to lose $2.1 million (or 7.5K BNB) and crashed the price of the GYMNET token.
The BSC-based yield aggregator, which has undergone many audits, recently updated its “claim and pool” functionality, introducing a pool contract vulnerability due to a lack of caller authentication. This vulnerability was used to grow the balance without making any payments.
Smart contract hack overview:
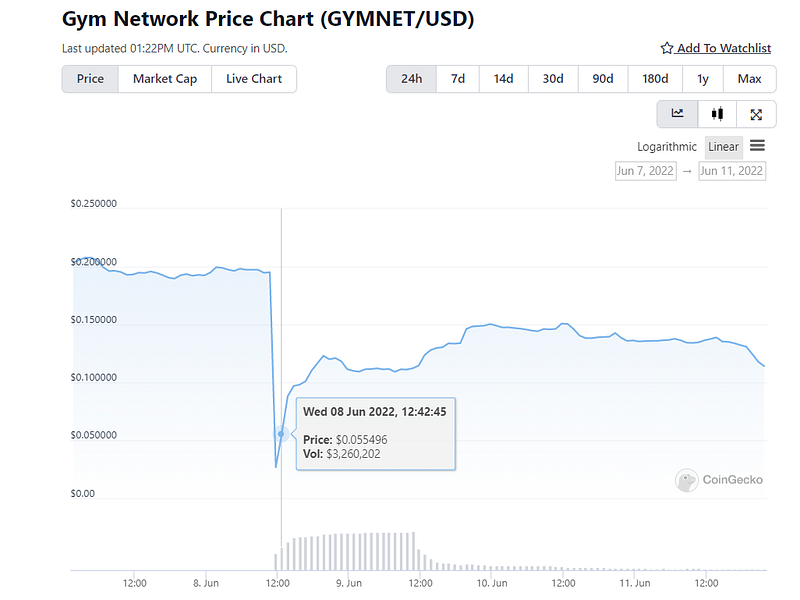
Fig: Sudden drop in GYMNET token price after the hack
Decoding the Smart Contract Vulnerability:
- The GymSinglePool contract added a new capability to deposit tokens from other contracts that lacked validation on visibility and access control of the function caller. The depositFromOtherContract() method was designated as “external,” meaning anybody could call it.
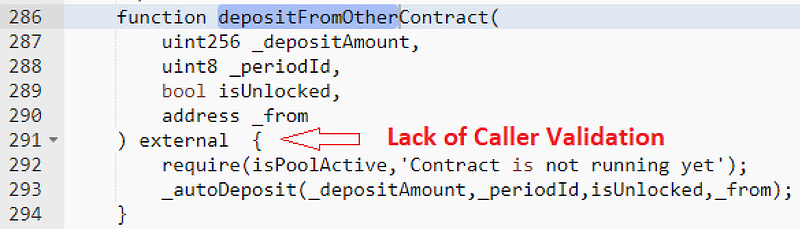
- The attackers repeatedly invoked the
depositFromOtherContract()function and made bogus/false deposits to the contract without spending any tokens, which increased their token balance. - Because the deposits were made from the attacker’s address, they simply withdrew the previously deposited tokens in the contract, which were in fact, fraudulent deposits that led to a sudden drop in the GYM token’s price after the rekt.
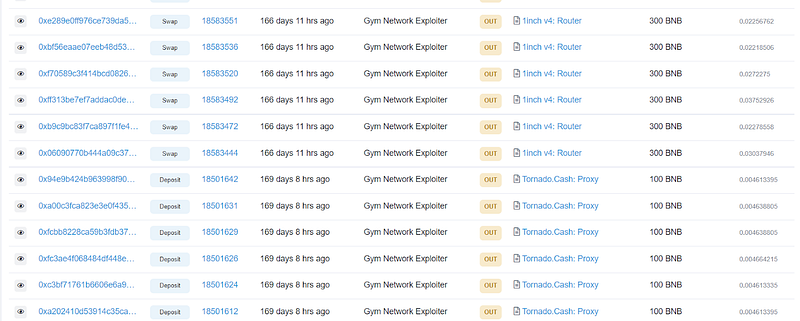
- The attacker rapidly moved 2k BNB to their wallet using Tornado Cash, while the remaining tokens remained on the attacker’s BSC address.

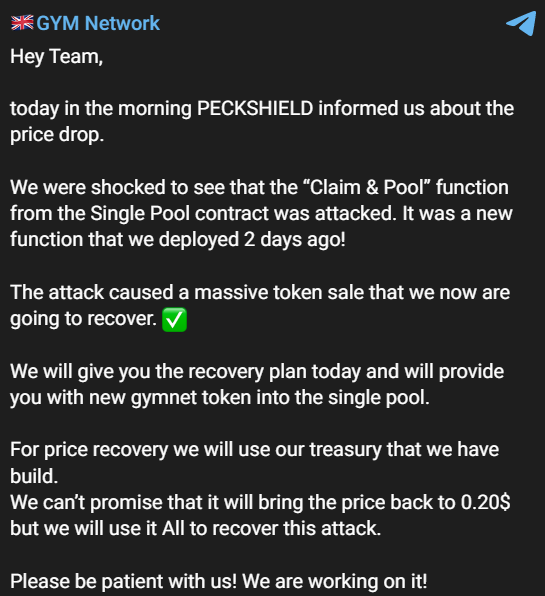
- Officials from GYM Network quickly located this incident and informed the community about the hack with the necessary details.
Mitigation & best practices:
- Access control modules are provided by OpenZeppelin for creating role-based access control. Its application is simple: for each role that you wish to design, you will create a new role identifier that will be used to grant, revoke, and verify if an account has that role.
- To do this, we may utilize the Ownable library from Openzeppelin. When a function call is made, OpenZeppelin’s Ownable defines modifiers like “onlyOwner” to determine if the user is the owner of the contract.
- To conserve gas, functions that are supposed to be public should be made external, while the rest of the functions should be made private or view only.
- To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShieldsprovide not only Smart Contract security but also provide end-to-end security of web applications and externally exposed networks. Schedule a call at https://credshields.com/
- Scan your contract against the latest common security vulnerabilities with 130+ patterns at SolidityScan, which includes the detection of Re-entrancy vulnerabilities.

Attack Summary:
Lack of caller validation and releasing new features without full testing resulted in the loss of 2.1M from the GYM Network Protocol; it is advised that every new release in the smart contracts be extensively audited, and Defi audits are handled with utmost care.
Conclusion:
SolidityScan is an advanced smart-contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
