GDS Chain Hack Analysis — Flash Loan Exploit
GDS Chain Hack Analysis — Flash Loan Exploit
Overview:
- A flash loan attack occurred on the GDS chain on January 3, 2023. Following the attack, the project’s BSC lending pool was compromised. This attack resulted in a total loss of $187,000 and an 84% decline in the price of GDS currency.
Smart contract hack overview
- Attacker’s address: 0xcf2362
- Attacker’s transaction: 0x2bb7
- Attacker’s remaining balance: 0xcf2362
- GDS Contract code: 0xc1bb12
- GDS Pool closed after the attack: 0x06d236
- 10.3M $GDS tokens reward: 0x43b487c
Decoding the smart contract vulnerability:
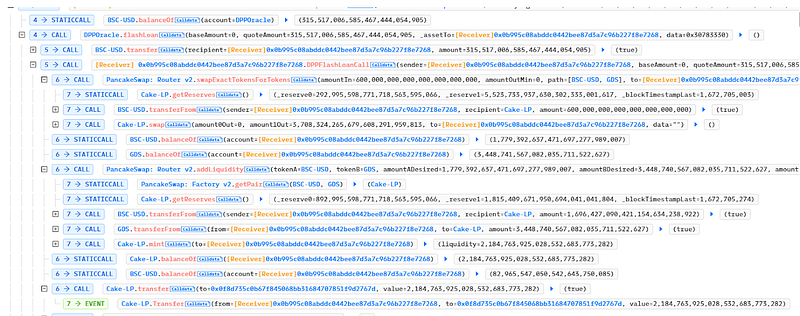
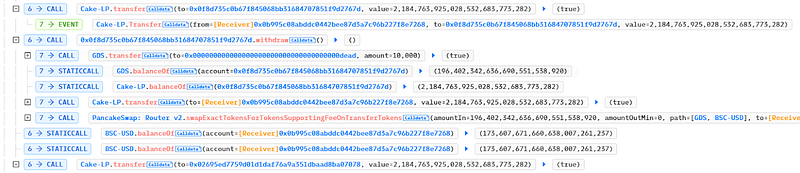
- The Attacker first borrowed 2.38 million $USDT using a flash loan and then used a pancake swap to trade 0.6 million $USDT for 3.4 million $GDS tokens.
- The attacker then used the remaining $1.7 million in USDT in the liquidity pool to obtain a large amount of LP tokens.
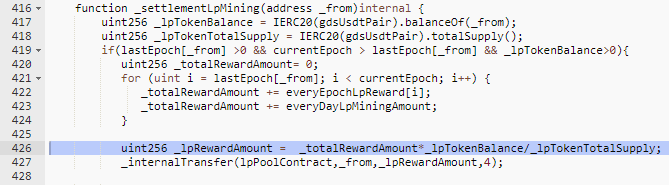
- There was a flaw in the” _lpRewardAmount” calculation function that only validates the weights for the lp token and does not check the time and other factors to avoid a flash loan.
lpRewardAmount = ( total reward amount globally * LP token balance )/ total supply for the liquidity pool token
- Misusing it they were able to collect the profits from the $GDS token contract and then transfer the LP tokens to another contract 70 times to earn higher rewards until the flash loan was totally repaid.
Mitigation and best practices:
- Critical functions responsible for rewarding and transferring funds from the liquidity pool should be thoroughly audited for flash loan and arbitrage cases, and checks such as time should also be considered when rewarding users, and it should not rely heavily on the available balance of LpTokens in attacker’s wallet.
- The logic of rising balance resulting in increased profits should be validated properly to prevent flash loans and not cause injustice to other users’ funds in the liquidity pool.
- Rather than depending on a single DEX platform, employ decentralized pricing oracles such as Chainklink and Band Protocol to obtain price feeds.
- Open Zeppelin Contracts can help reduce risk by utilizing battle-tested smart contract libraries for Ethereum and other blockchains. It comprises the most widely used ERC standard implementations.
- To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShieldsprovide smart contract security and end-to-end security of web applications and externally exposed networks. Schedule a call at https://credshields.com/
- Scan your contract against the latest common security vulnerabilities with 130+ patterns at SolidityScan, which includes the detection of Re-entrancy vulnerabilities.

Conclusion:
SolidityScan is an advanced smart-contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security related updates.
SolidityScan — LinkedIn | Twitter | Telegram | Discord
