Fortress Protocol Oracle Vulnerability Explained

Fortress Protocol Oracle Vulnerability Explained
Overview:
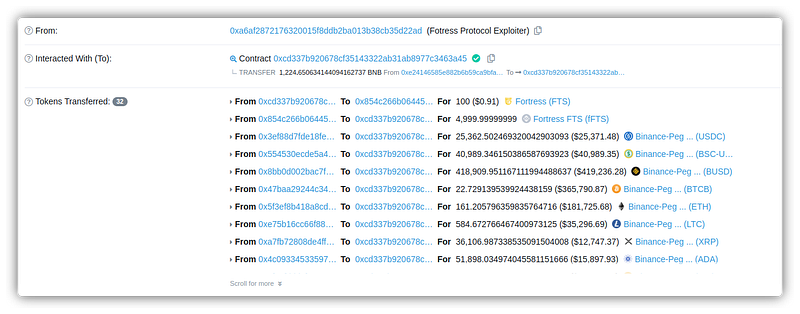
The hack occurred on May 08, 2022, amounting to a loss of ~$3 million. The attacker was able to manipulate the project’s oracle [used for interacting with the real world with the blockchain world], which allowed the attacker to upsurge the collateral by price manipulation and swap tokens to drain funds.
Smart Contract Hack Overview:
- Fortress used Umbrella Network Oracle. The Hack comprised a chain of two vulnerabilities that enabled the attacker to manipulate
FTStoken price. - The Fortress Protocol Contract’s code: 0xC1B
- Attacker’s Address: 0xA6A
- Exploit transaction: 0x13D
Decoding the Smart Contract Vulnerability:
Vulnerability 1:
- An attacker could manipulate the lending-related configuration of the fortress governance contract if the minimum FTS required token to Vote, i.e., 400,000, is met.
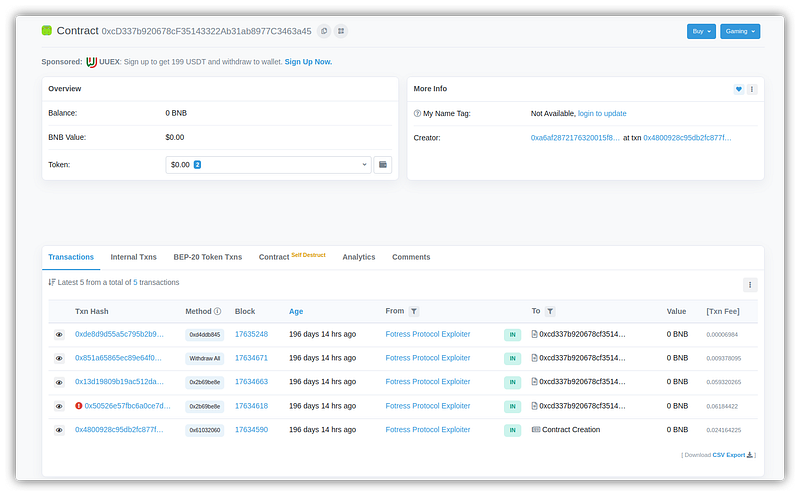
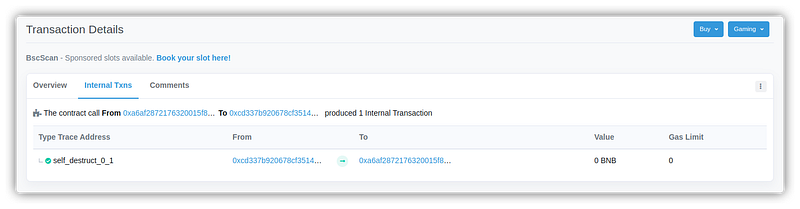
- Attacker’s self-destruct contract: 0xCD3
- The attacker swapped ~11 ETH for over 400,000 FTS tokens which allowed him to create a malicious proposal that was successfully executed as it was controlled and voted on by the attacker itself.
- The attacker voted for the proposal: 0x83A
- Thus Proposal 11 gets executed to add FTS token collateral to 700000000000000000, which was further utilized to make a profit.
- The contract that the attacker deployed had a “self-destruct” clause that was triggered by the attacker as soon as the malicious transactions were completed.
Vulnerability 2:
- An attacker manipulates the publicly accessible variable with improper verification checks, allowing an attacker to trigger the function call responsible for updating the oracle price by increasing the power value [limitation & checks were also not made in power value and can be directly controlled].
- Vulnerability type: SWC-121
- Vulnerable Code: 0xC11
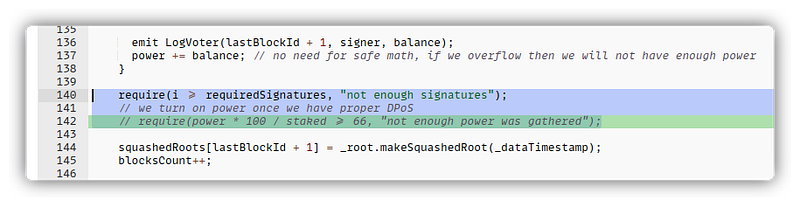
- The L142 was used to verify the power value. The code was commented out. The attacker used the signature function and triggered the function call to upsurge the oracle price.
- At L142, it’s clear that signature verification functions have no verification to ensure that the function call is triggered properly.
Mitigation & Best practices:
- Protocols need to add security layers. In this case, use at least two oracles to verify the price. This would mitigate the hack and ensure proper checks on critical functions and publicly accessible variables.
- As the price of governance tokens and how many governance tokens will be circulated are unknown, it is exceedingly difficult to spot this issue during an audit.
- Raise the number of validators.
- Consider hiring professionals to conduct an audit like CredShields. Find out if they utilize the most recent cross-chain tracking techniques.
- Scan your contract against the latest common security vulnerabilities with 130+ patterns at SolidityScan.

Conclusion:
This incident emphasizes the importance of smart contract audits because both vulnerabilities are inherent in the contract. Due to these flaws, the attacker was able to manipulate the project’s price oracle, allowing them to borrow a variety of tokens with inflated collateral, exchange them, and cause a loss.
SolidityScan is an advanced smart-contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
