Exactly Protocol Hack Analysis
Exactly Protocol Hack Analysis
Overview:
On August 18, 2023, Exactly Protocol suffered a hack due to an insufficient validation vulnerability in the DebtManager contract, leading to an approximate loss of ~7M USD.
Smart Contract Hack Overview:
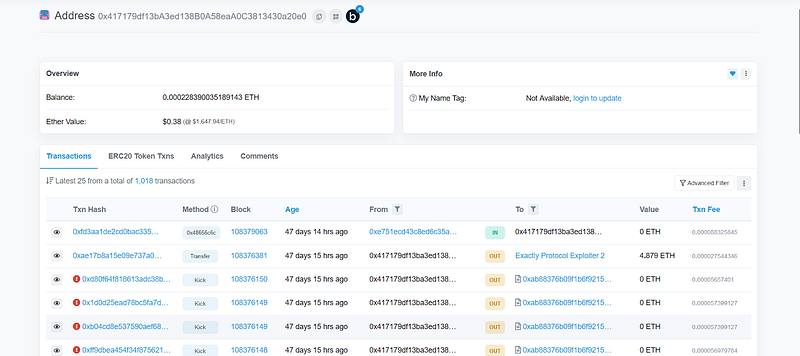
- Exploiter address 1: 0x3747db
- Exploiter address 2: 0xe4f34a
- Exploiter address 3: 0x417179
- Attack Contract: 0x6dd61c
- Vulnerable Contract: 0x16748C
- Attack Transaction: 0x417179
Decoding the Smart Contract Vulnerability:
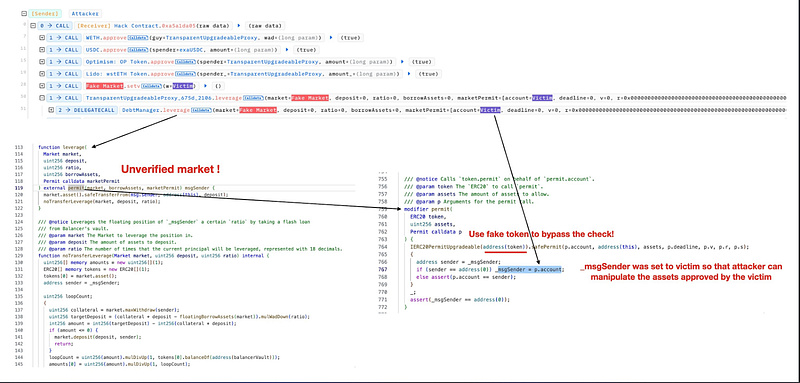
- The root cause of the issue was an insufficient check in the DebtManager.
- The attacker managed to bypass the permit verification in the DebtManager contract’s leverage function by inserting a fake market address without validation and altering the _msgSender to mimic the victim’s address.
- Subsequently, in an untrusted external call, the attacker re-entered the crossDeleverage function in the DebtManager contract and successfully stole collateral from the _msgSender.
Mitigation and Best Practices:
- Always validate your code by writing comprehensive test cases that cover all the possible business logic.
- To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Schedule a call at https://credshields.com/
- Scan your Solidity contracts against the latest common security vulnerabilities with 130+ detections at SolidityScan
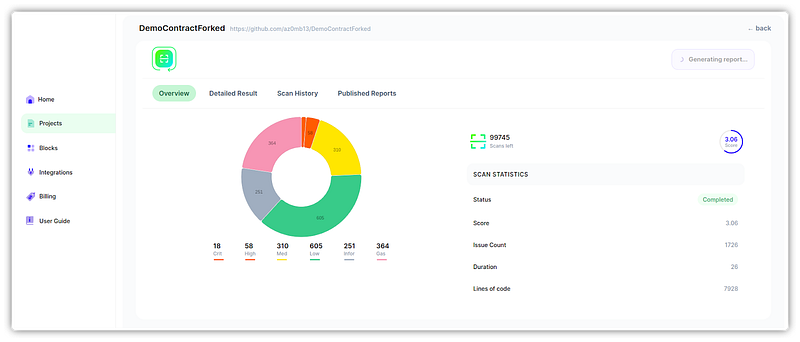
Conclusion:
SolidityScan is an advanced smart contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
SolidityScan — LinkedIn | Twitter | Telegram | Discord
