ElasticSwap Hack Analysis — Erroneous calculations bug
ElasticSwap Hack Analysis — Erroneous calculations bug
Overview:
A price manipulation hack occurred on December 13th, 2022, allowing attackers to steal $845K from the Avalanche and Ethereum chains. Two different accounting systems were used at the time of the attack, which resulted in erroneous calculations for adding and subtracting liquidity from contracts, which resulted in a price manipulation attack.
Smart Contract Hack Overview:
- Ethereum chain details:
- AMPLvUSDC Contract: 0xa0c5a
- MEV Owner: 0xBeAdeD
- MEV BOT Contract: 0xE9115
- Attacker’s transaction: 0xc2d86
- MEV front-run transaction: 0xb3648
2. Avalanche chain details:
- Attacker’s address: 0x3bd, 0x25fD, 0xdd84
- Attacker’s contract: 0xa274
- AVA Exploit transaction: 0x782b241
- TICvUSDC.e Contract: 0x4ae1da
3. Erroneous calculation Logic code: #L88 , #L191
Decoding the smart contract vulnerability:
- The attack occurred because the
addLiquidityused a constant K value algorithm for internal accounting while theremoveLiquidityused a balance of two tokens (baseToken and quoteToken) in the current pool to calculate the amount internally.
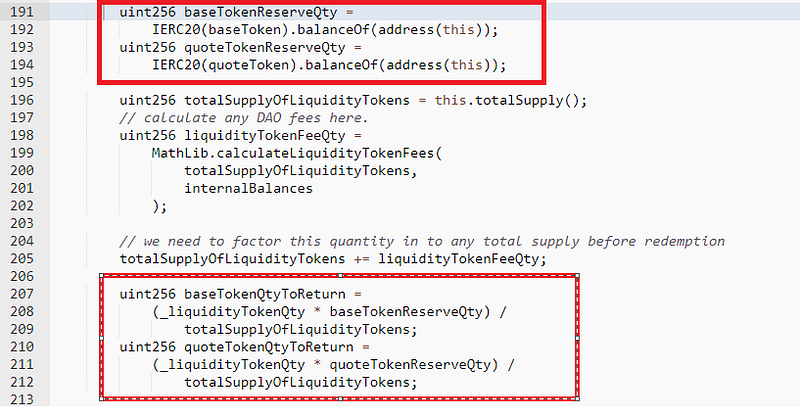
- In order to increase liquidity, the exchange contract utilized a constant K value method; however, in order to decrease liquidity, it computes the tokens to return by calculating the token balance in the current pool and decreases the internal accounting reserves.
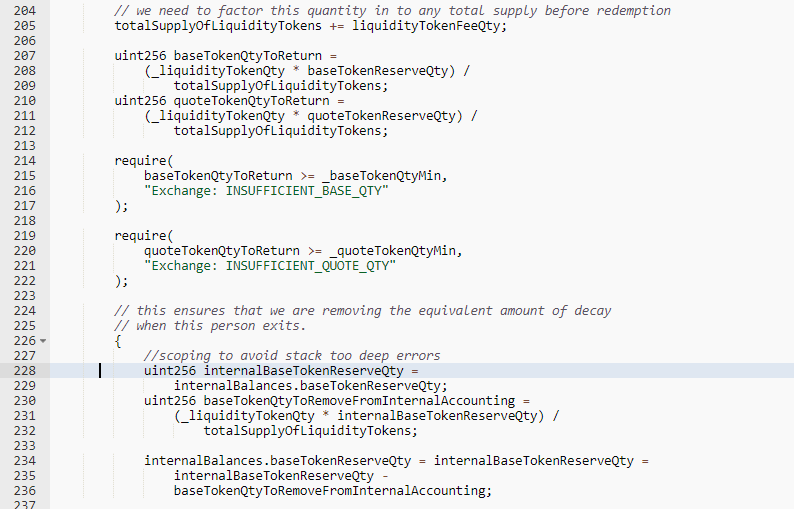
- Before moving some funds (USDC.e) to the TIC-USDC pool, the attacker first created liquidity.
- The quantity of LP tokens was multiplied by the amount of USDC.e that must be transmitted to the attacker, who then removed this liquidity, and the pool became unbalanced. The attacker swapped USDC for TIC tokens and made a profit out of it.
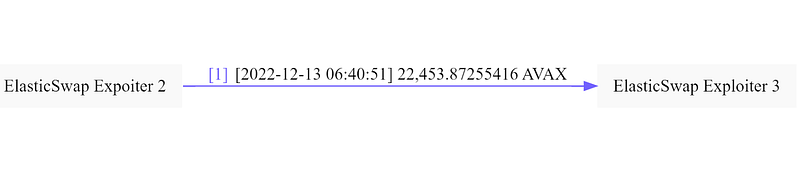
- $290,328 worth of profit totaling 22,454 AVAX were made by the attacker, who then moved them to another location.
- Using the same technique, the AMPL-USDC pool of ElasticSwap on Ethereum was also hacked.
- The exploit was front run by an MEV bot, and the exploiter’s attack transaction can be seen below.
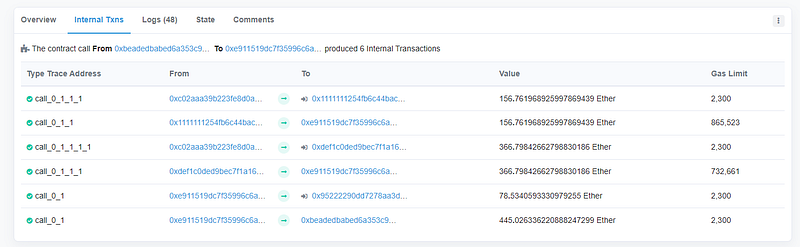
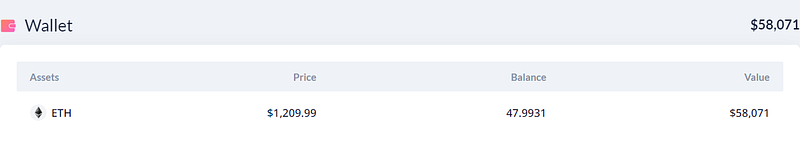
- A profit of around 445 ETH, or about $564,000, was earned by the attacker. This money is still in the attacker’s account.
- The MEV Bot Owner made about 445 ETH, of which he gave the protocol 400.5 ETH back and pocketed the rest as a reward.
Mitigation and Best Practices:
- It is crucial to remember that the reasoning for adding and removing liquidity uses the same logic and method and does not primarily rely on state variables that can be altered and cause the pool to collapse.
- To stop price manipulation attempts, implement validations on transaction variables and securely revoke transactions containing fraudulent deposits and transfers.
- Price manipulation attempts can be mitigated to a larger extent via oracles such as Chain Links and input validation on those feed parameters to prevent stale data.
- To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShieldsprovide not only Smart Contract security but also provide end-to-end security of web applications and externally exposed networks. Schedule a call at https://credshields.com/
- Scan your contract against the latest common security vulnerabilities with 130+ patterns at SolidityScan, which includes the detection of Re-entrancy vulnerabilities.

Conclusion:
SolidityScan is an advanced smart-contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
