Sharwa Finance Hack Analysis

Sharwa Finance Hack Analysis

Overview:
On October 20, 2025, Sharwa Finance (@SharwaFinance), a decentralized margin-trading protocol on Arbitrum, suffered a critical price manipulation exploit that allowed attackers to extract approximately $146,000 USD in two separate incidents (~$61k and ~$85k).
Sharwa Finance offered one-click leveraged long/short trading, using AMM-based price quotes (Uniswap V3-style getAmountOut/getAmountIn) to determine swap amounts, collateral health, and solvency metrics during trade execution.
The exploit originated from the reliance on the instantaneous AMM reserve-based quotes from Uniswap’s Quoter,without any time-weighted or external oracle validation. This design flaw let the attacker artificially inflate or deflate swap output prices, creating false solvency conditions and draining protocol liquidity.
With assistance from Binance, the Sharwa Finance Team has recovered 40,000 USDT, which represents approximately 80% of the funds stolen in the first attack. The second attack was executed by a different actor, who has not yet been identified.
Smart Contract Hack Overview:
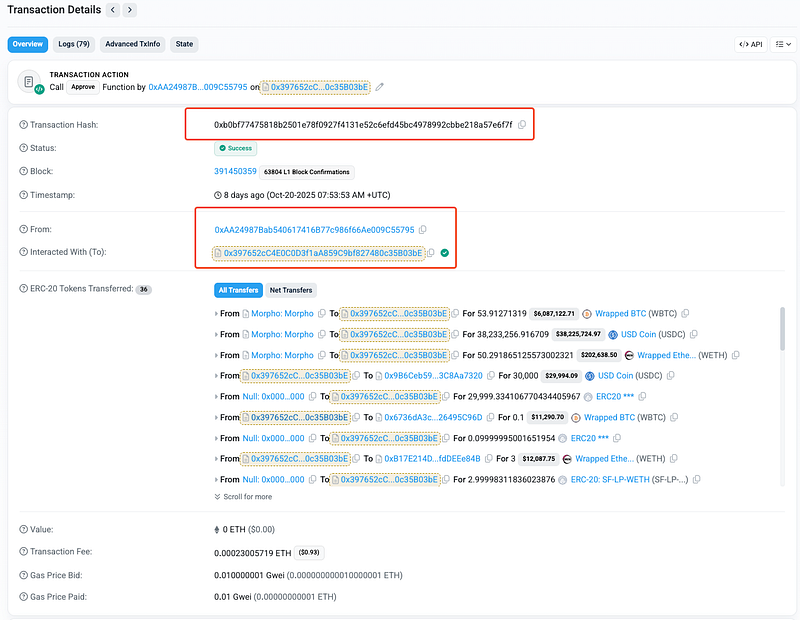
- Attack Transactions:
0x9f8b4 , 0xb0bf7 - Victim Contracts:
0xb8494 - Attacker Addresses:
0xd356c, 0xaa249 - OWASP SC Top 10: SC03:2025 Logic Errors
Decoding the Smart Contract Vulnerability:
- The root cause of the exploit is that the protocol trusted a manipulable AMM spot quote (
getAmountOut) for critical solvency decision and swap execution, lacked slippage minimums, and performed no post-swap health check. - Thus enabling an attacker to exploit the temporal gap between quote and actual execution under manipulated liquidity conditions. A classic Time-of-Check to Time-of-Use (TOCTOU) failure in DeFi systems.
- Sharwa Finance’s
FacadeTradeRoutercontract uses Uniswap V3’sQuotercontract viagetAmountOut()to determine the output amount of a swap. - However,
getAmountOut()is not an oracle; it simply performs a mathematical computation based on the current liquidity reserves of the AMM pool. Because AMM reserves can change at any time within a single block, this value can be easily manipulated by an attacker who controls the price curve before the quote is taken. - For example, when closing a leveraged position, the router calculates how much USDC will be received for selling the collateral (e.g., WBTC). If an attacker temporarily dumps WBTC into the pool, the reserves shift, and the quoted price returned by
getAmountOut()drastically decreases. The router, trusting this manipulated quote, proceeds to execute swaps and repayment logic based on the falsified rate. - In multiple swap-building branches of
fillSwapData()andexecuteSwap(), the protocol constructs Uniswap swap payloads withamountOutMinimum = 0. - This effectively means the router accepts any output amount from the swap; no matter how bad the exchange rate becomes during execution. Even if the AMM price drastically deviates from the quoted rate due to front-running or liquidity manipulation, the swap does not revert; instead, it executes at the attacker’s chosen price. This removes the most fundamental on-chain protection mechanism against price manipulation: slippage bounding.
- After executing swaps to repay debts or close positions, the router never re-evaluates the user’s solvency using updated balances. The solvency check occurs only before the swaps are performed; using the manipulated
getAmountOut()result. Once the swap completes at an adversarial rate, no subsequent validation ensures that the borrower’s position remains solvent. - This sequencing flaw means the system confirms health under assumptions that may no longer hold after external state changes.
- As a result, the attacker could orchestrate a transaction where the system believes enough collateral was sold to repay the loan, even though, in reality, the manipulated execution left significant undercollateralization and bad debt on the protocol.
Attack Sequence:
Mitigation and Best Practices:
- To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Our public audit reports can be found on https://github.com/Credshields/audit-reports. Schedule a call at https://credshields.com/
- Scan your Solidity contracts against the latest common security vulnerabilities with 494+ detections at SolidityScan.
Conclusion:
SolidityScan is an advanced smart contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
