DoughFina Hack Analysis
DoughFina Hack Analysis
Overview:
On July 12th, 2024, Dough Finance (@DoughFina) fell victim to a flash loan attack, resulting in a loss of approximately $1.8 Million.
Smart Contract Hack Overview:
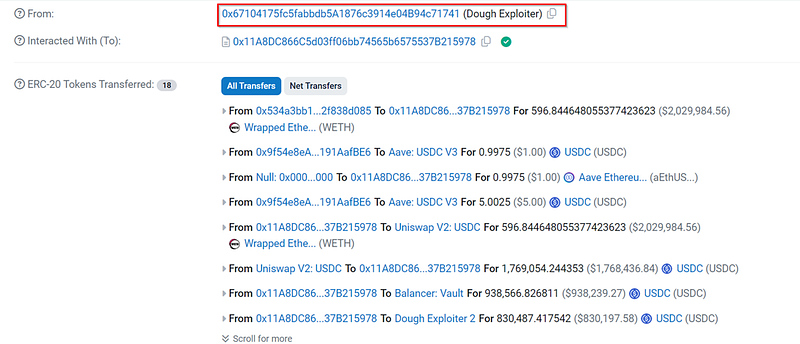
Related Address Chain-
- Dough Exploiter 3: 0x34611
- Dough Exploiter 4: 0x932e7
- Dough Exploiter 5: 0xBA256
- Dough Finance’s Contract: 0x9f54e
- Attack Transaction: 0x92cdc
Tornado Cash Txn: 0xd5c92, 0x8ffe4, 0x4e55f, 0xa2cda, 0xc1946, 0x07e31
Decoding the Smart Contract Vulnerability:
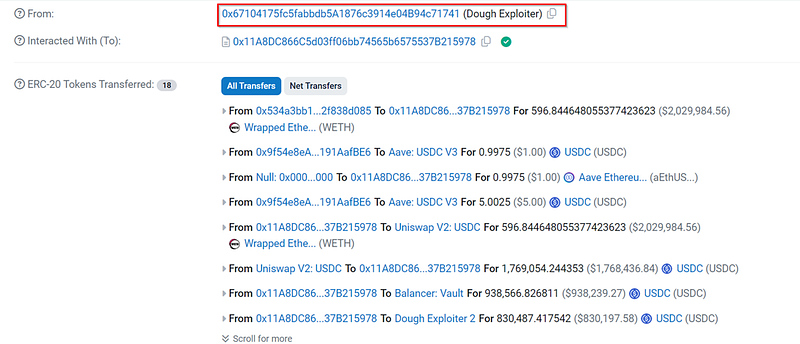
· The root cause is that the ConnectorDeleverageParaswap contract did not validate flash loan callback data which led to WETH transfer.
· Here, the deloopAllCollaterals function did not verify the parameters extracted by _getParaswapData; which allowed the attacker to craft a malicious multiTokenSwapData containing attacker-controlled tokenTransferProxy address.
· During the loop execution, the contract used safeIncreaseAllowance to increase the allowance for the attacker’s address instead of the intended ParaSwap proxy.
· The attacker then used this increased allowance to transfer tokens from the contract’s balance to their own address.
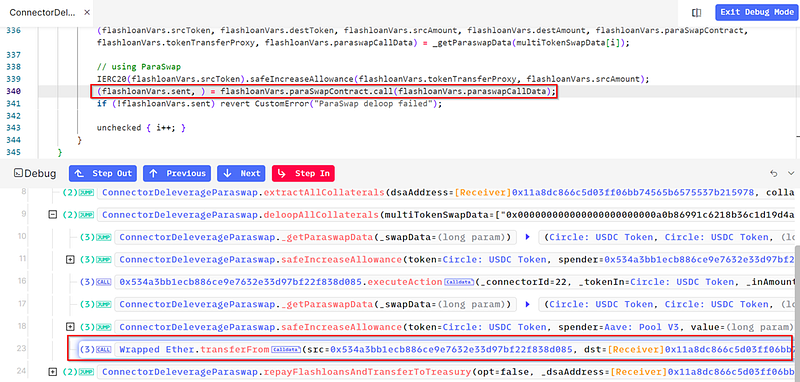
· As observed in the attack flow image above, the original intention of the contract was to call ParaSwap, but instead the `transferFrom` method was called, thus resulting in a loss of funds to nearly 608 ETH or $1.8 Million.
· The attacker has already transferred the misappropriated funds to Tornado Cash.
· DoughFina’s Team also has issued an ultimatum (0xa5eed) to the attacker by writing an on-chain message to ‘discuss further steps’ and recover stolen $1.8 Million.
Mitigation and Best Practices:
· Include comprehensive validation checks for calldata and sender authenticity during all transaction callbacks, ensuring that only authorized transactions can be executed.
· Always validate your code by writing comprehensive test cases that cover all the possible business logic.
· To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Our public audit reports can be found on https://github.com/Credshields/audit-reports. Schedule a call with us at https://credshields.com/
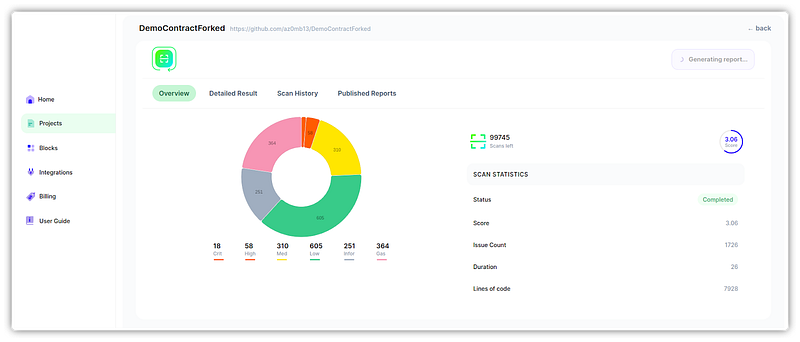
· Scan your Solidity contracts against the latest common security vulnerabilities with 225+ detectors at SolidityScan.
Conclusion:
SolidityScan is an advanced smart contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
