DMC Hack Analysis — Free Mint Vulnerability
DMC Hack Analysis — Free Mint Vulnerability
Overview
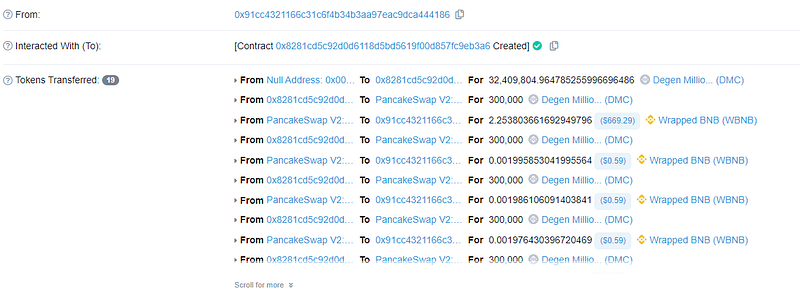
On February 6, 2023, a hack on the DMC project took place, resulting in the loss of about 60 WBNB because of a flaw in their smart contract that permitted the free mint for any external caller.
Smart Contract Hack Overview:
- Attacker’s address: 0x8faa29efb,0x91cc4321
- Attacker’s transaction: 0x6563608a,0x80bc025
- DMC-official contract code: 0xa176c5288
- Pancake Swap Contract: 0x6ce9b411
Decoding the Smart Contract Vulnerability:
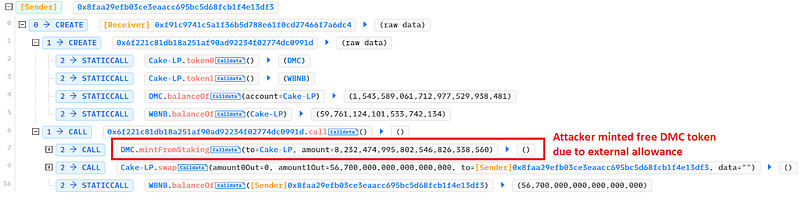
- During the investigation into the attack, it was discovered that the access restriction on the mintFromStaking() function was seriously violated, allowing any caller to mint any number of tokens to their address.
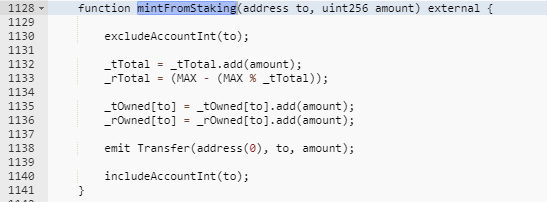
- By exploiting this missing access control, the attackers created 4,06,42,278 DMC tokens and exchanged them for WBNB equivalents via a pancake swap, costing DMC holders roughly 60 WBNB. The project was informed of the compromise and relaunched the initiative as a result.
Mitigation and Best Practices:
- Consider implementing an access control mechanism to ensure that only authorized accounts can call the mintFromStaking function. One approach to implementing access control is to use the OpenZeppelin Access Control library, which provides a robust, battle-tested implementation of access control.
- Make sure to validate the input parameters to the mintFromStaking function to ensure that they meet certain requirements. For example, ensure that the to parameter is a valid Ethereum address and that the amount parameter is greater than zero.
- To prevent reentrancy attacks, use the OpenZeppelin ReentrancyGuard library, which provides a way to protect functions from reentrant calls.
- Consider using the
requirestatement to check that any state changes that occur within the mintFromStaking function are valid. For example, you could check that the _tTotal and _rTotal variables are not exceeding the maximum supply of the token. - Consider setting a gas limit for the mintFromStaking function to prevent it from consuming too much gas and potentially causing the transaction to fail. You can set a gas limit using the gas keyword.
- To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Schedule a call at https://credshields.com/
- Scan your Solidity contracts against the latest common security vulnerabilities with 130+ detection at SolidityScan including access control vulnerabilities.

Conclusion:
SolidityScan is an advanced smart-contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
SolidityScan — LinkedIn | Twitter | Telegram | Discord
