DeltaPrime Hack Analysis
DeltaPrime Hack Analysis
On November 11th, 2024, DeltaPrime (@DeltaPrimeDefi) was targeted in a sophisticated exploit on both the Arbitrum and Avalanche networks, leading to a total loss of approximately $4.75 million. This marks DeltaPrime’s second major security breach, following a $6 million exploit in September. In this latest attack, a vulnerability in the periphery adapter contract allowed the attacker to exploit unchecked borrowing and repayment logic in swapDebtParaSwap, enabling them to borrow more assets than their collateral. Additionally, the claimReward function was vulnerable to arbitrary contract input, allowing the attacker to manipulate internal balances and withdraw rewards unchecked, draining several pools.
Smart Contract Hack Overview:
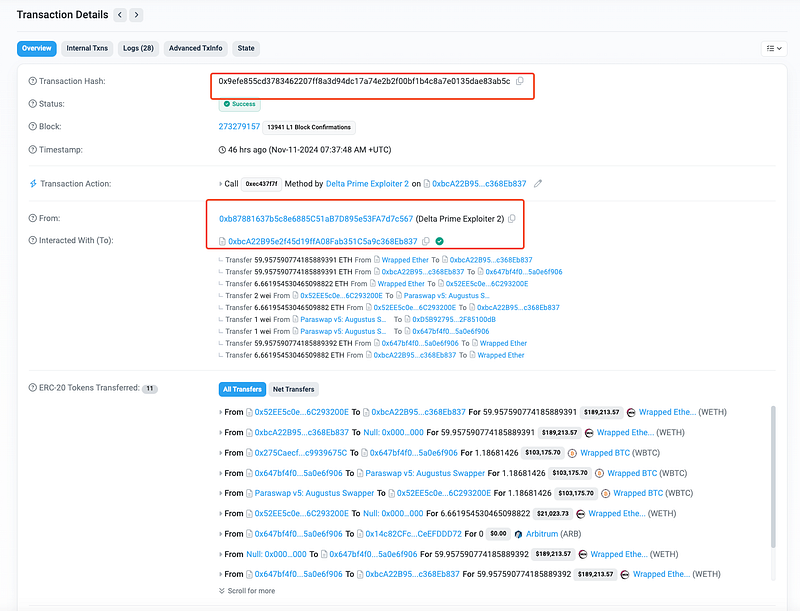
- ARB Attack Transaction: 0x9efe8
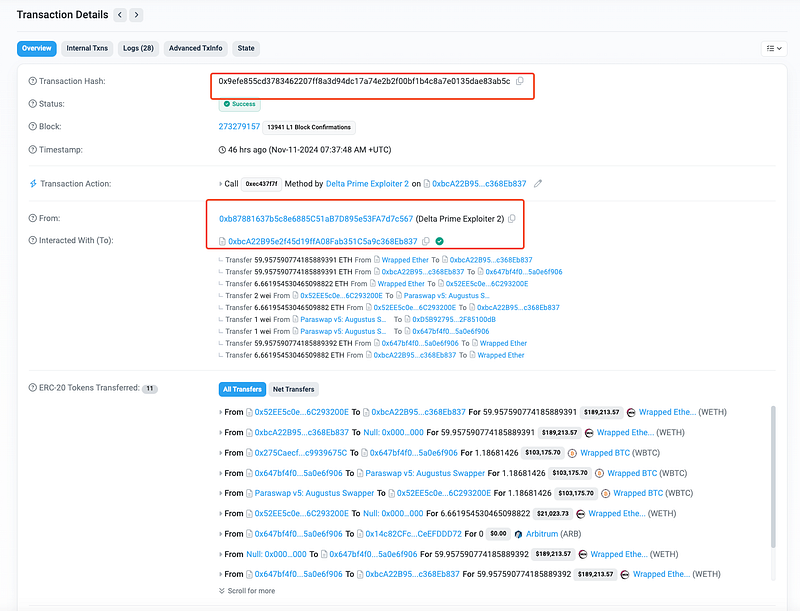
- AVAX Attack Transaction: 0xece4e
- ARB Attacker Addresses: 0xb8788, 0x56e7f, 0x10172
- AVAX Attacker Addresses: 0xd3d53, 0xd5381
Decoding the Smart Contract Vulnerability:
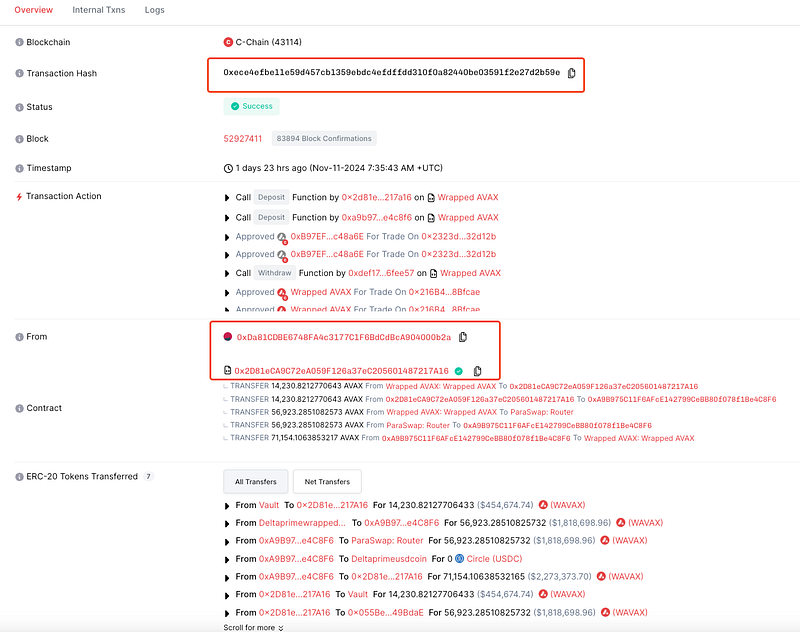
- The root cause of the exploit in DeltaPrime lies in two main vulnerabilities: unchecked input in the
swapDebtParaSwapfunction and arbitrary external contract input in theclaimRewardfunction. These flaws allowed the attacker to borrow more assets than their collateral and withdraw collateral as rewards without proper validation.
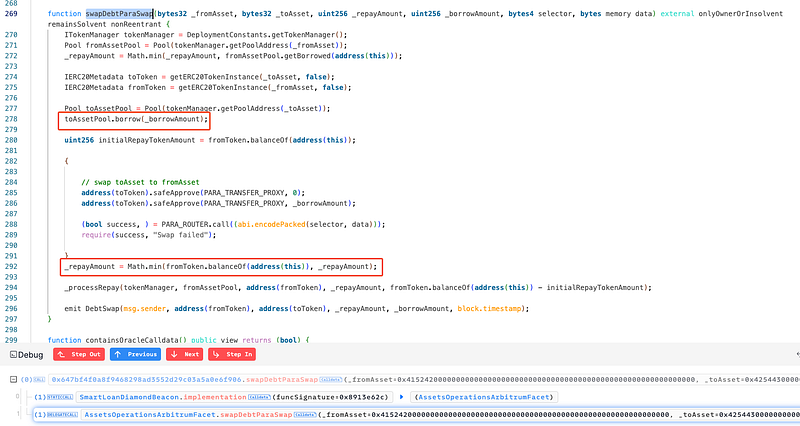
- The
_repayAmountwas not correctly validated before being passed to theswapAdapter, which led to the borrowed WBTC being transferred out of the attacker’s account to their malicious contract (0x52ee). - The attacker borrowed 1.18 WBTC using their collateral of 59.9 ETH, then used the swap adapter to send the borrowed WBTC to a different address without triggering a repayment check.
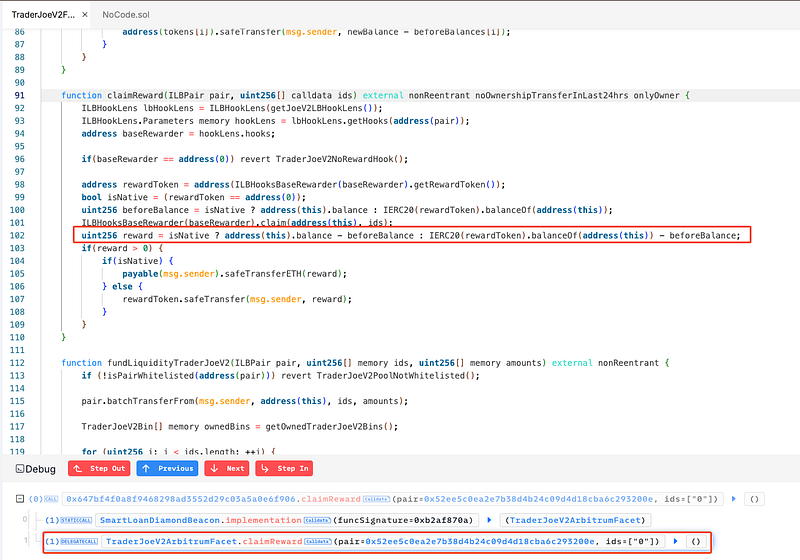
- The second vulnerability involved the
claimReward()function, which allows users to claim rewards from the platform. In theTraderJoeV2ArbitrumFacetcontract, thepairparameter (used in the reward claim mechanism) was not properly validated, allowing the attacker to pass a malicious contract address. - This malicious contract was designed to manipulate the internal balances of the DeltaPrime contract and trick the system into awarding more rewards than intended. Specifically, the attacker used this flaw to trigger the
wrapNative()function within their contract, which wrapped the collateral (ETH) into WETH, altering the contract’s balance and causing the protocol to mistakenly pay out 59.9 ETH as a reward. - The malicious contract was passed as an argument in the
claimReward()function, causing the system to believe that the wrapped ETH (WETH) was part of the reward. - The attacker siphoned off significant funds from DeltaPrime’s smart contracts, totaling approximately $4.75 million (across both Arbitrum and Avalanche networks). However, instead of fleeing with the loot, the attacker chose to stake and invest it strategically in various DeFi protocols to generate passive income.
- While many exploiters typically try to quickly launder or disperse stolen funds, this attacker took an unconventional approach by turning the stolen funds into an opportunity for yield generation on Avalanche.
Staked USDC: $600K staked through Stargate.
Liquidity Providing: $518K in USDC/USDT liquidity on LFJ.
AVAX: 4,865 AVAX staked.
WETH.e: 49.68 WETH.e staked.
BTC.b: 6.34 BTC.b staked.
- DeltaPrime Team acknowledged the rekt via X: https://x.com/DeltaPrimeDefi/status/1855899502944903195.

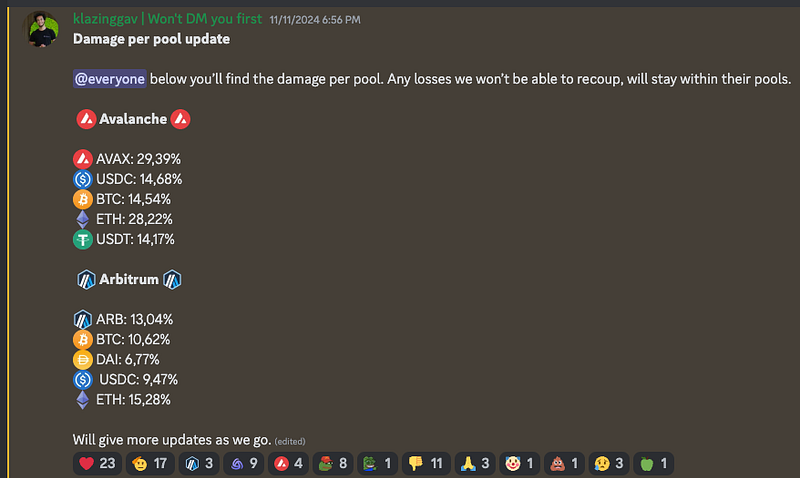
- They have also provided detailed summary of losses on their official discord server. In both networks, the most significant losses occurred in AVAX and ETH pools on the Avalanche network, while ARB and ETH pools experienced the highest losses on the Arbitrum network.
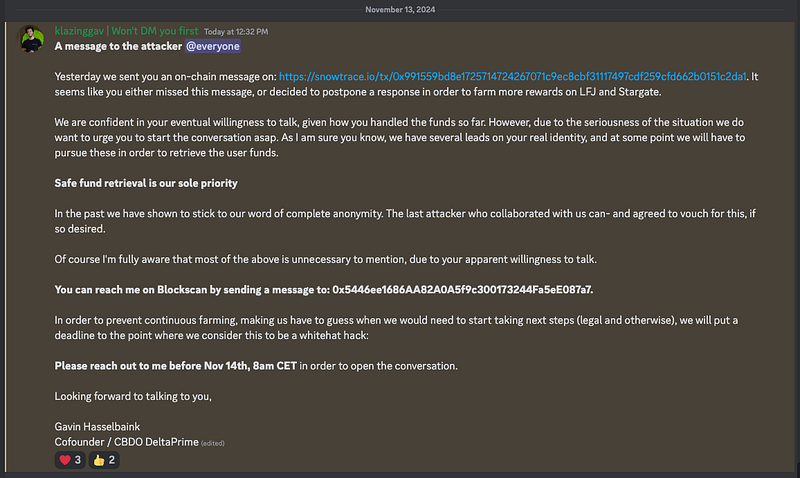
- The DeltaPrime Team has also initiated communication efforts with the attacker inorder to retrieve stolen funds.
Mitigation and Best Practices:
- Ensure that the _repayAmount is properly validated before being passed to the swapAdapter in the swapDebtParaSwap function.
- Ensure that the _repayAmount is properly validated before being passed to the swapAdapter in the swapDebtParaSwap function.
- In the claimReward() function, when interacting with external contracts or wrapping assets, ensure that collateral (e.g., ETH) is not inadvertently treated as part of the reward.
- Introduce a solvency check for reward claims to ensure that rewards do not push the system into insolvency or allow withdrawals that would exceed the platform’s available liquidity.
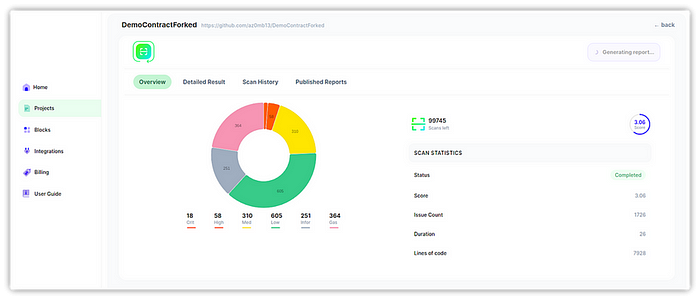
- To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Our public audit reports can be found on https://github.com/Credshields/audit-reports. Schedule a call at https://credshields.com/
- Scan your Solidity contracts against the latest common security vulnerabilities with 280+ detections at SolidityScan.
Conclusion:
SolidityScan is an advanced smart contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
