CUT Token Hack Analysis
CUT Token Hack Analysis
Overview:
On September 10th, 2024, Caterpillar Coin ($CUT token) was targeted in a flashloan attack, leading to a substantial loss of approximately $1.4M USD. The attacker exploited vulnerabilities in the token’s price protection mechanisms, which allowed for manipulation of token reserves and rewards, resulting in a 99% slippage on the token.
Smart Contract Hack Overview:
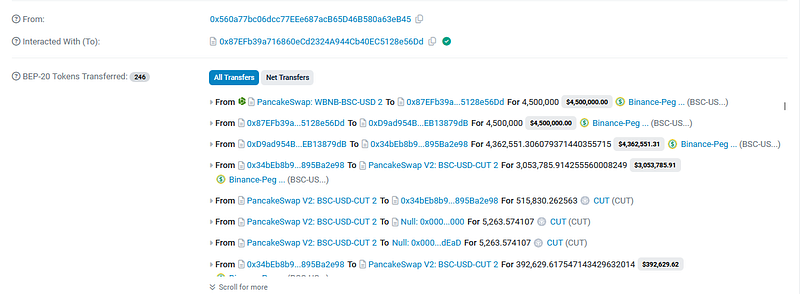
- Attack Transactions: 0x2c123d , 0xce6e47 , 0x6262c0
- Attacker’s Address: 0x5766d1
- Exploit contract: 0x87EFb3
- CUT token: 0x7057f3
Decoding the Smart Contract Vulnerability:
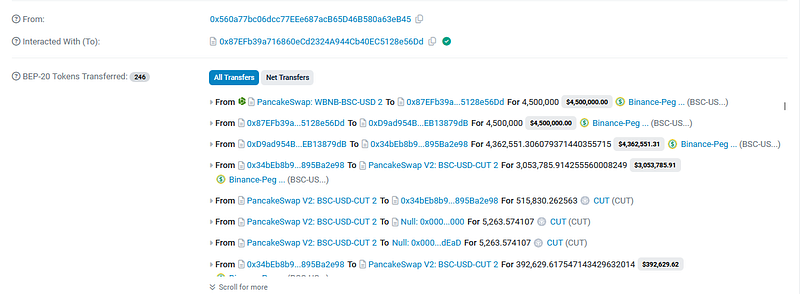
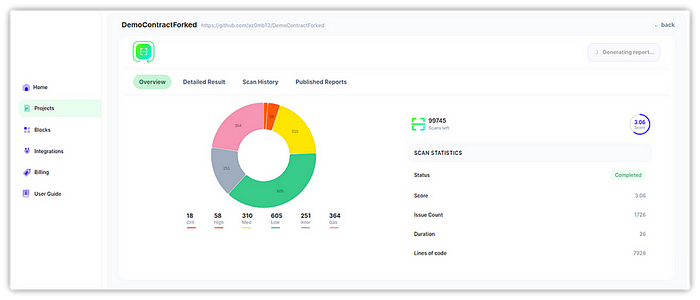
- The vulnerability stemmed from the price protection mechanism involving the external contracts at 0x7b2e7c. This mechanism was responsible for generating reward records when liquidity was added to the USDT-CUT liquidity pool.
- The attacker used a flashloan of 4,500,000 USDT, swapped a portion for CUT tokens, and added liquidity to the pool. The price manipulation occurred during the liquidity addition, where the CUT tokens and USDT reserves were unbalanced, triggering a flaw in the reward calculation.
- Order 3157 was created upon liquidity addition, recording a reward based on the current price. The exploiter was able to manipulate the reward by modifying the reserve ratio of the liquidity pool, swapping their CUT tokens for a larger amount of USDT.
- The vulnerability lies in the calculation process, which naively computes rewards by comparing token balances before and after the liquidity addition, ignoring possible manipulations. The attacker exploited this, leading to a significant increase in their CUT token holdings and subsequent USDT gains.
- The exploiter repeatedly performed these transactions, increasing their profits over multiple swaps. Eventually, they drained the pool, withdrew their profits, and repaid the flashloan, retaining ~$1.4M USD in stolen funds.
Mitigation and Best Practices:
· Instead of relying on a static reward calculation based solely on token balances before and after liquidity addition, introduce a dynamic calculation that accounts for market conditions and liquidity pool reserves over time. This would prevent attackers from exploiting momentary imbalances to inflate rewards.
· Introduce a cooldown period or time-based restrictions for liquidity pool interactions, such as adding and removing liquidity. This would limit the frequency at which liquidity can be added or removed, reducing the ability of attackers to perform rapid consecutive swaps to manipulate the reserves and reward mechanism.
· Always validate your code by writing comprehensive test cases that cover all the possible business logic.
· To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Our public audit reports can be found on https://github.com/Credshields/audit-reports. Schedule a call at https://credshields.com/
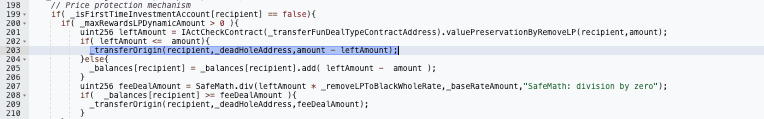
· Scan your Solidity contracts against the latest common security vulnerabilities with 225+ detections at SolidityScan.
Conclusion:
SolidityScan is an advanced smart contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
