Curve Finance DNS Hijack Vulnerability Explained
Curve Finance DNS Hijack Vulnerability Explained
Overview:
On August 10, 2022, one of the most trustworthy and dependable coin-swapping pool platforms in the Defi, Curve Finance protocol, was hacked. This was due to a web2 vulnerability in the frontend, which emptied around $575K from users’ accounts.
The attackers hijacked the DNS and injected malicious contract address via javascript, which allowed them to reroute the user’s funds and approval from Curve.fi into their wallet.
Decoding the Vulnerability:
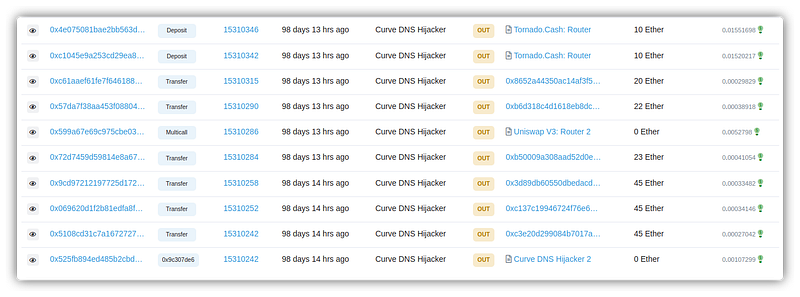
- Attacker’s address: 0x50f9
- Attacker’s Contract Address: 0x9eb5
- Attacker’s Transaction: 0x525
- User’s Authorization transaction: 0xf63d
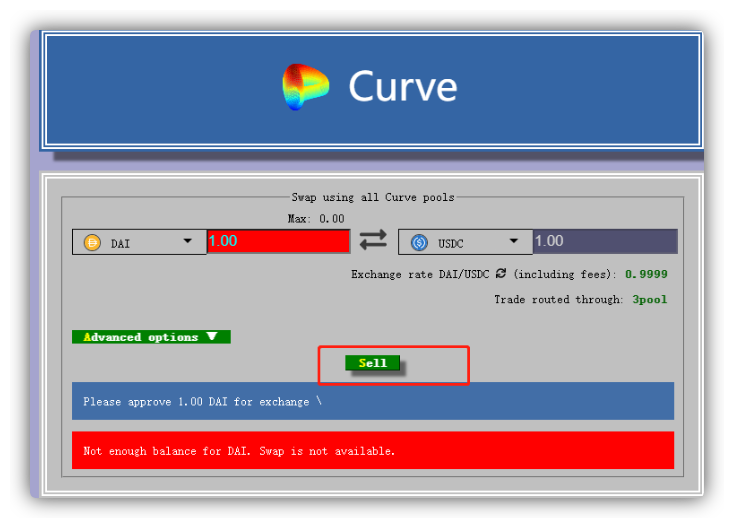
- The attacker hacked Curve Finance’s DNS, redirecting users to a malicious URL comparable to phishing assaults.
- The attacker constructed their own contract and inserted the contract address into the javascript for further user authorization.
- When consumers accepted the transaction, they unintentionally authorized the hacker’s contract.
- When the hacker contract address obtained the users’ token authorization, it could immediately execute the transfer function in the attack contract to transfer the tokens in the user’s wallet to the hacker’s address.
- Attackers stole users’ tokens from decentralized exchanges and transferred them using Tornado Cash.
Technical Analysis:
- The domain name system (DNS) of @CurveFinance was compromised.
What does a DNS do?
- It converts human-readable website names to IP addresses.
- In this scenario, the IP address is utilized to communicate with a server, which offers the Curve Finance online application to the user’s browser.
- A DNS, for example, converts https://google.com to a machine-readable IP address.
- In this attack, the hackers changed the IP address translated by DNS to http://curve.fi.
- They gave their own server’s IP address and built an identical web application.
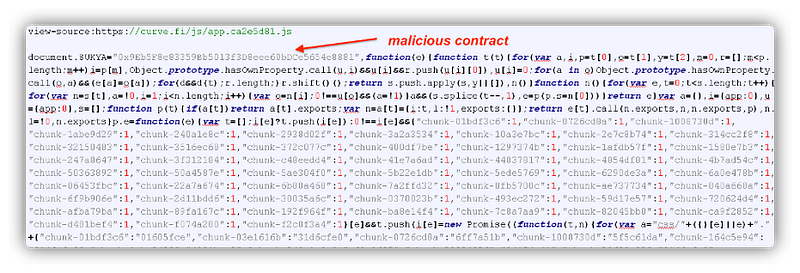
However, they installed new smart contracts to steal money and inserted their contract address into the source code’s javascript at curve[.]fi/js/app.ca2e5d81.js
Unaware users thought they were utilizing @CurveFinance, but they were really authorizing transactions that stole their money.
Mitigation best practices:
- Decentralization does not imply reliance on centrally housed front-end servers. It should execute full stack on chain servers with no centralized control.
- Check all smart contracts with which you interact.
- Name the authentic smart contract that addresses anything interesting.
- Always investigate and check whether everything appears real and if there are no modifications on the application side that might influence money before approving application access to your wallet.
Conclusion
Sometimes Smart Contract owners focus way too much on the security of smart contracts and completely forget the security of web applications and external networks. However, the frontend and exposed external network need an audit too. We at CredShields provide not only Smart Contract security but also provide end-to-end security of web applications and externally exposed networks. Schedule a call at https://credshields.com/