Convergence Finance Hack Analysis
Convergence Finance Hack Analysis
Overview:
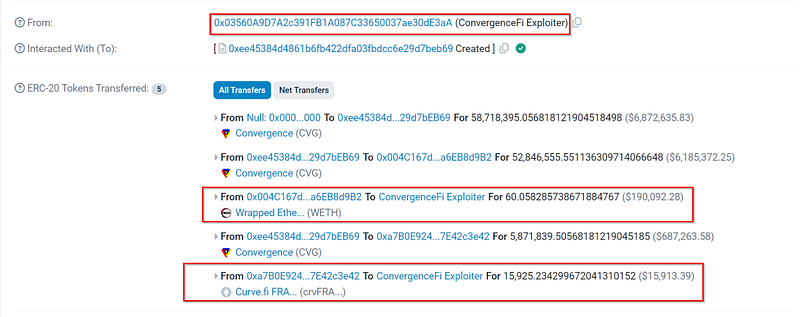
On August 1st, 2024, Convergence Finance (@Convergence_fi) — a Curve-based yield-enhancing protocol fell victim to an attack due to lack of proper input validation; which resulted in loss of 58M CVG — nearly amounting to 210K USD.
Smart Contract Hack Overview:
- Attacker’s Address: 0x03560
- Malicious Contract: 0xee453
- Victim’s Proxy Contract Address: 0x2b083
- Victim’s Implementation Contract Address: 0x47c69
- Attack Transaction: 0x636be
Decoding the Smart Contract Vulnerability:
- The root cause of the vulnerability was the lack of proper input validation for the
cvxRewardCountparameter in theclaimMultipleStakingfunction inCvxRewardDistributor.sol. - It did not validate the staking contracts provided in the
claimContractsarray. This allowed the attacker to exploit the function by manipulating the reward distribution process.
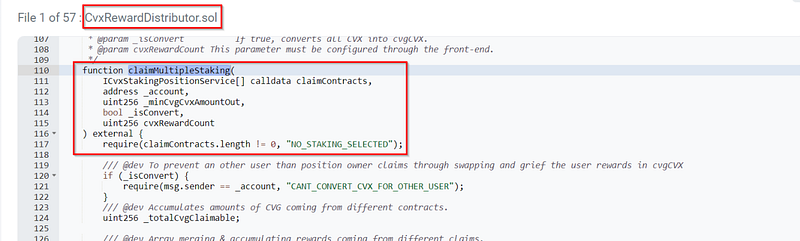
- The
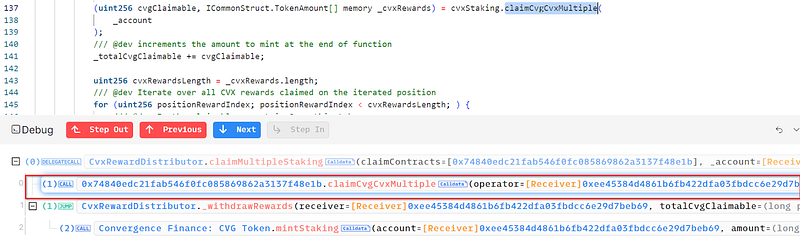
claimMultipleStakingfunction is designed to handle claiming rewards from multiple staking contracts. It accumulates amounts of CVG tokens and Convex rewards from various staking contracts and processes them accordingly. - The attacker deployed a malicious contract that had a function with the same signature as
claimCvgCvxMultiple. This function was intended to process reward claims.
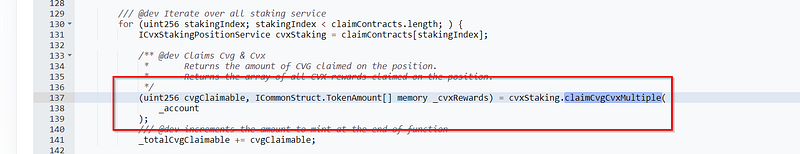
- The attacker included the address of their malicious contract in the
claimContractsarray when invoking theclaimMultipleStakingfunction. Since the function lacked validation, it called the malicious contract as if it were a legitimate staking contract. - The malicious contract’s
claimCvgCvxMultiplefunction was executed, which was designed to mint CVG tokens and transfer Convex rewards. This allowed the attacker to mint a significant amount of CVG tokens — specifically, 58M CVG tokens meant for staking emissions.
- The stolen funds have currently been moved via Tornado Cash Routers.
- Official X account of Convergence Finance has acknowledged the hack and issued a security advisory.
Mitigation and Best Practices:
- Ensure that all inputs, including addresses and contract calls, are validated against expected formats and constraints. This prevents malicious or unexpected values from being processed.
- Restrict access to critical functions by ensuring that only authorized addresses or entities can call them. For example, limit the ability to execute sensitive functions to trusted addresses, specific roles, or the owners of related assets. This prevents unauthorized parties from performing actions that could compromise the system’s integrity.
- Always validate your code by writing comprehensive test cases that cover all the possible business logic.
- To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Our public audit reports can be found at https://github.com/Credshields/audit-reports. Schedule a call at https://credshields.com/
- Scan your Solidity contracts against the latest common security vulnerabilities with 225+ detections at SolidityScan.
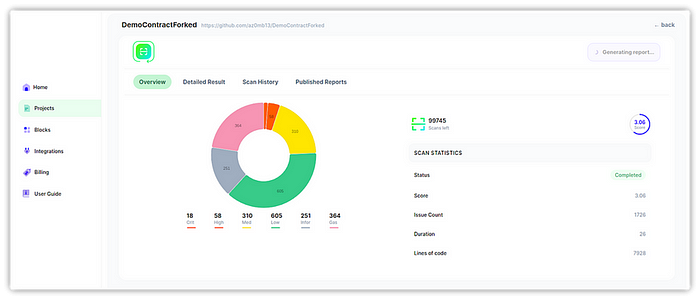
Fig: SolidityScan — Smart Contract Vulnerability Scanner
Conclusion:
SolidityScan is an advanced smart contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
SolidityScan — LinkedIn | Twitter | Telegram | Discord
