CloberDEX Liquidity Vault Hack Analysis
CloberDEX Liquidity Vault Hack Analysis
Overview:
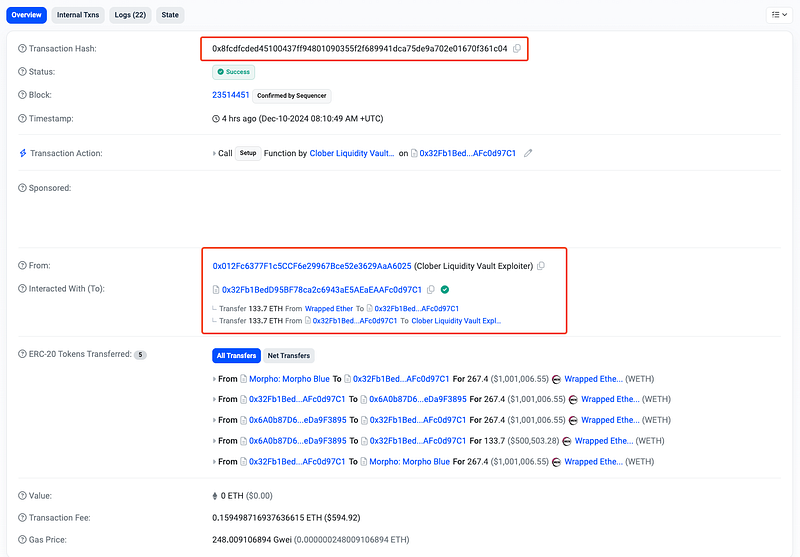
On December 10, 2024, CloberDEX (@CloberDex) suffered an exploit targeting its Liquidity Vault on the Base network. The attacker exploited a reentrancy vulnerability in the _burn function of the Rebalancer contract, resulting in a loss of approximately 133.7 ETH (~$501,279).
The core Clober protocol remains unaffected, and all primary functionalities continue to operate securely. However, the breach highlights critical flaws in the vault’s contract logic, which were exploited using a malicious strategy crafted by the attacker.
Smart Contract Hack Overview:
- Attack Transaction: 0x8fcdf
- Attacker’s Address: 0x012Fc6
- Vulnerable Contract Address: 0x6a0b8
- Stolen Funds Parked At: 0x711C8 , 0x7760d
Decoding the Smart Contract Vulnerability:
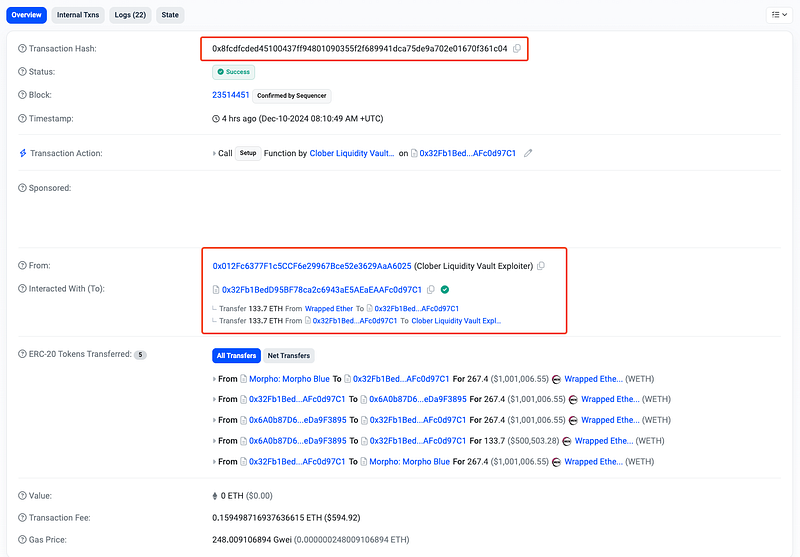
- The root cause of the exploit lies in the improper handling of external calls within the
_burnfunction. Specifically, the function performs token transfers (bookKeyA.quote.transferandbookKeyA.base.transfer) to the user before updating critical state variables (pool.reserveAandpool.reserveB).
- This sequence of operations violates the recommended checks-effects-interactions pattern, making the contract susceptible to reentrancy attacks.

- The external token transfer calls (
transfer) allowed the attacker to execute malicious contracts or reenter the same function, taking advantage of the fact that the state variablespool.reserveAandpool.reserveBhave not yet been updated. This opened the door for repeated exploitation within the same transaction. - Additionally, the withdrawal amounts for
withdrawalAandwithdrawalBare calculated based onpool.reserveAandpool.reserveB, which are only updated after the transfers are executed. During the reentrancy attack, these unmodified reserve values are exploited to miscalculate the token amounts repeatedly. - The Clober team has taken immediate action following the recent security breach affecting the Liquidity Vault on Base. The team has made efforts to communicate with the attacker to request the return of the misappropriated funds. They have assured that no legal action will be pursued if the funds are returned to the following address:
- Return Address: 0x83E66fBfB14758dA99462F389F54D4003DFB95b4
- The team is also collaborating with relevant parties to track and recover the stolen assets. Ref: https://x.com/CloberDEX/status/1866457314078998750
- The team also clarified that the security breach is limited to the Liquidity Vault on Base. They have reassured the community that Clober Core remains unaffected by the incident. Additionally, users of the Mitosis testnet are advised to continue using the platform without any security concerns.
Mitigation and Best Practices:
- To prevent reentrancy attacks, Clober should refactor the _burn function to follow the Checks-Effects-Interactions pattern. Introduce reentrancy guards to prevent reentrant calls within sensitive functions. A simple
nonReentrantmodifier can be added to functions like_burn, and other critical functions. - Check token balances before and after each transfer to ensure the correct amount is being transferred. For example, ensure the token balance before calling the
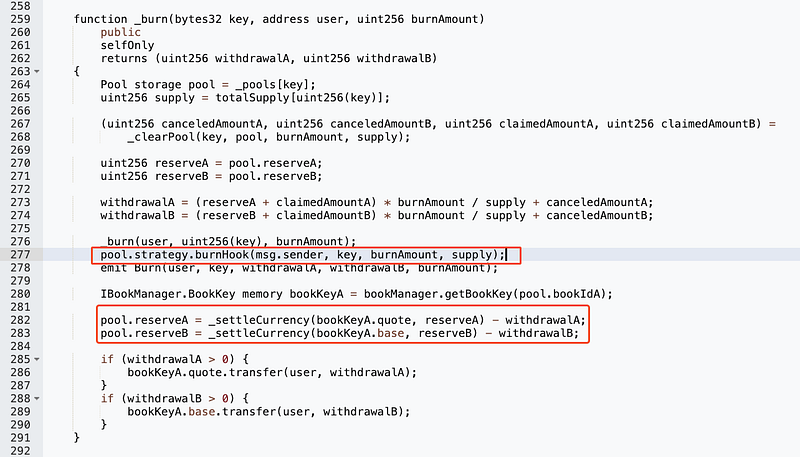
transferfunction is at least the expected amount and verify after the transfer. - To prevent such vulnerabilities, the best Smart Contract auditors must examine the Smart Contracts for logical issues. We at CredShields provide smart contract security and end-to-end security of web applications and externally exposed networks. Our public audit reports can be found on https://github.com/Credshields/audit-reports. Schedule a call at https://credshields.com/
- Scan your Solidity contracts against the latest common security vulnerabilities with 280+ detections at SolidityScan.
Conclusion:
SolidityScan is an advanced smart contract scanning tool that discovers vulnerabilities and reduces risks in code. Request a security audit with us, and we will help you secure your smart contracts. Signup for a free trial at https://solidityscan.com/signup
Follow us on our Social Media for Web3 security-related updates.
